1-15
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring Threat Detection
Configuring Scanning Threat Detection
Configuring Scanning Threat Detection
This section includes the following topics:
•
Information About Scanning Threat Detection, page 1-15
•
Guidelines and Limitations, page 1-16
•
•
Configuring Scanning Threat Detection, page 1-17
•
Monitoring Shunned Hosts, Attackers, and Targets, page 1-17
Information About Scanning Threat Detection
A typical scanning attack consists of a host that tests the accessibility of every IP address in a subnet (by
scanning through many hosts in the subnet or sweeping through many ports in a host or subnet). The
scanning threat detection feature determines when a host is performing a scan. Unlike IPS scan detection
that is based on traffic signatures, the ASA scanning threat detection feature maintains an extensive
database that contains host statistics that can be analyzed for scanning activity.
The host database tracks suspicious activity such as connections with no return activity, access of closed
service ports, vulnerable TCP behaviors such as non-random IPID, and many more behaviors.
If the scanning threat rate is exceeded, then the ASA sends a syslog message (733101), and optionally
shuns the attacker. The ASA tracks two types of rates: the average event rate over an interval, and the
burst event rate over a shorter burst interval. The burst event rate is 1/30th of the average rate interval or
10 seconds, whichever is higher. For each event detected that is considered to be part of a scanning
attack, the ASA checks the average and burst rate limits. If either rate is exceeded for traffic sent from
a host, then that host is considered to be an attacker. If either rate is exceeded for traffic received by a
host, then that host is considered to be a target.
Caution
The scanning threat detection feature can affect the ASA performance and memory significantly while
it creates and gathers host- and subnet-based data structure and information.
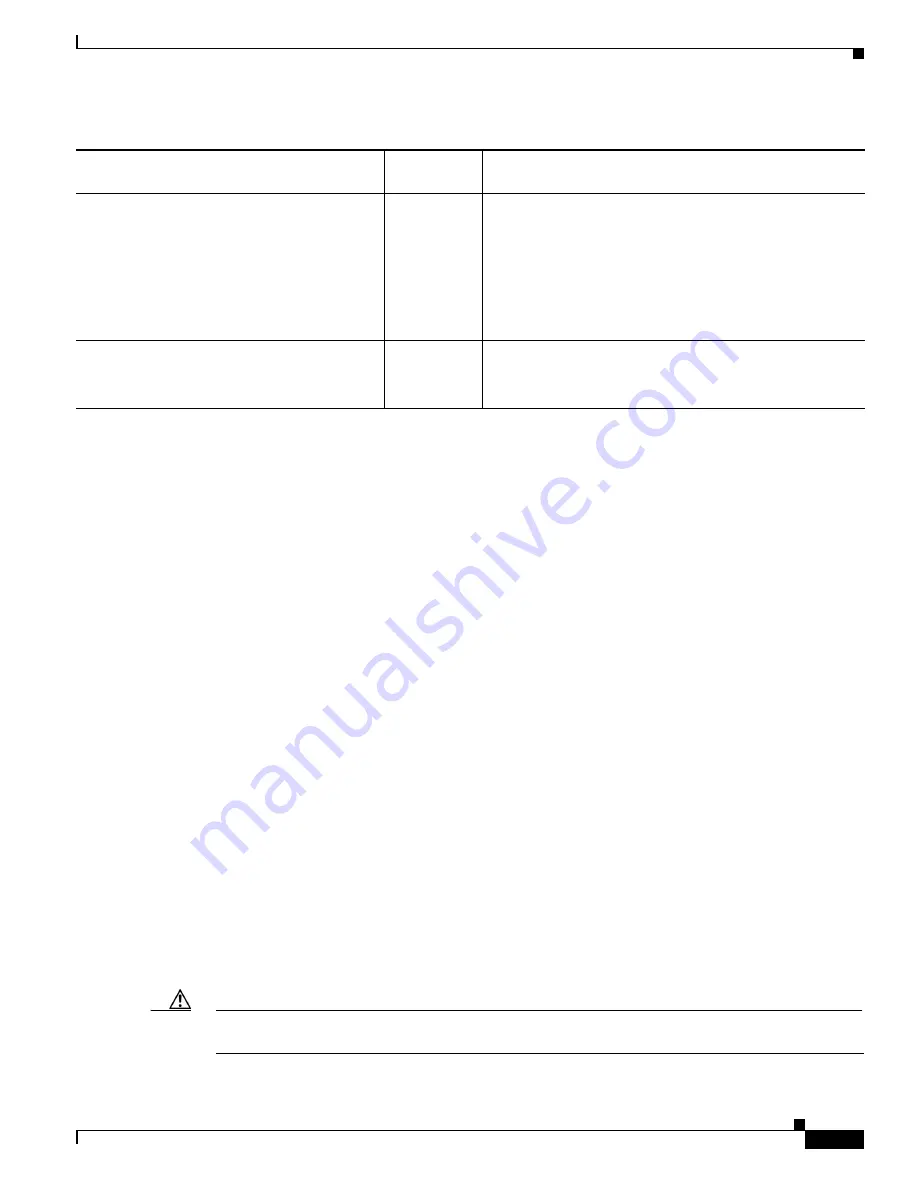
Customize port and protocol statistics rate
intervals
8.3(1)
You can now customize the number of rate intervals for
which statistics are collected. The default number of rates
was changed from 3 to 1.
The following commands were modified:
threat-detection
statistics port number-of-rates
,
threat-detection
statistics protocol number-of-rates
.
Improved memory usage
8.3(1)
The memory usage for threat detection was improved.
The following command was introduced:
show
threat-detection memory
.
Table 1-4
Feature History for Advanced Threat Detection Statistics (continued)
Feature Name
Platform
Releases
Feature Information
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......