1-3
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring the ASA IPS Module
Information About the ASA IPS module
Operating Modes
You can send traffic to the ASA IPS module using one of the following modes:
•
Inline mode—This mode places the ASA IPS module directly in the traffic flow (see
No traffic that you identified for IPS inspection can continue through the ASA without first passing
through, and being inspected by, the ASA IPS module. This mode is the most secure because every
packet that you identify for inspection is analyzed before being allowed through. Also, the ASA IPS
module can implement a blocking policy on a packet-by-packet basis. This mode, however, can
affect throughput.
•
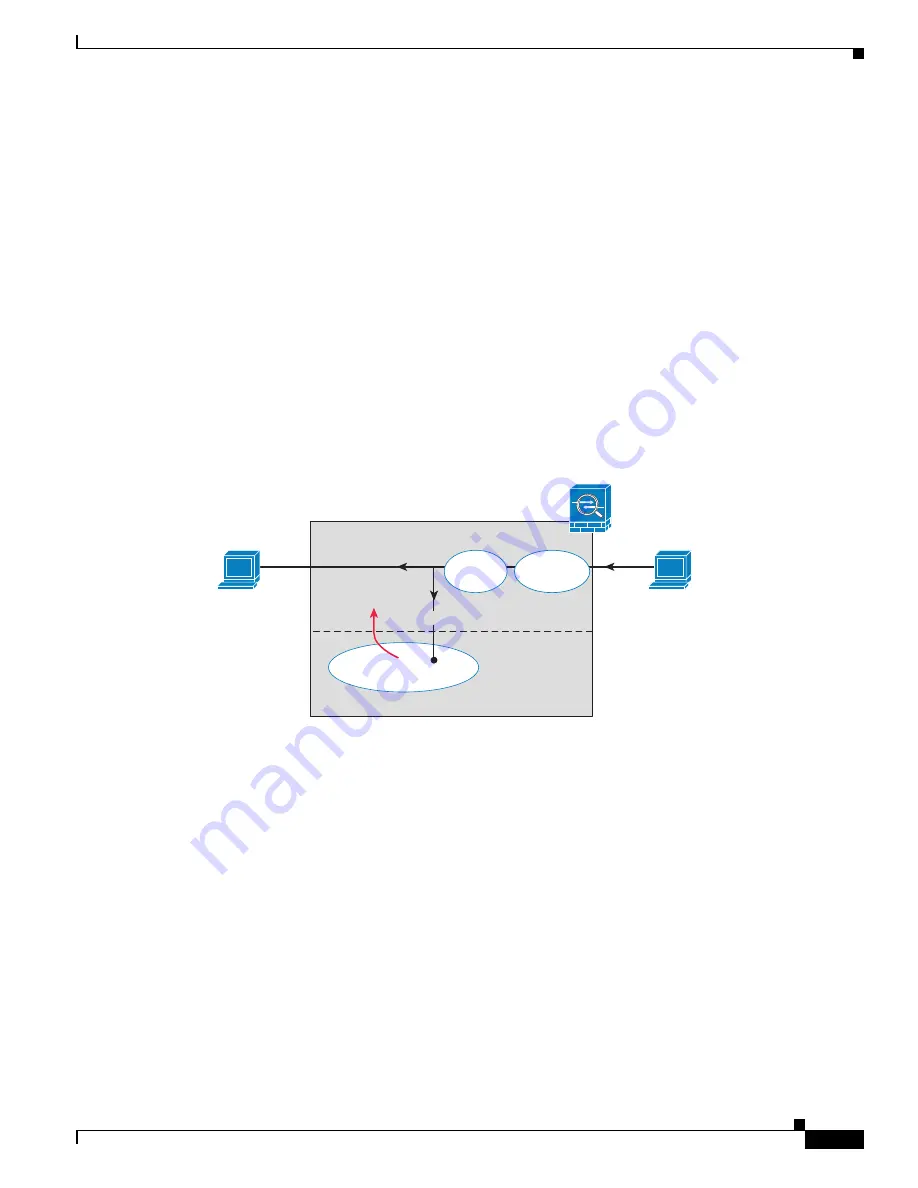
Promiscuous mode—This mode sends a duplicate stream of traffic to the ASA IPS module. This
mode is less secure, but has little impact on traffic throughput. Unlike inline mode, in promiscuous
mode the ASA IPS module can only block traffic by instructing the ASA to shun the traffic or by
resetting a connection on the ASA. Also, while the ASA IPS module is analyzing the traffic, a small
amount of traffic might pass through the ASA before the ASA IPS module can shun it.
shows the ASA IPS module in promiscuous mode. In this example, the ASA IPS module sends a
shun message to the ASA for traffic it identified as a threat.
Figure 1-2
ASA IPS module Traffic Flow in the ASA: Promiscuous Mode
Using Virtual Sensors (ASA 5510 and Higher)
The ASA IPS module running IPS software Version 6.0 and later can run multiple virtual sensors, which
means you can configure multiple security policies on the ASA IPS module. You can assign each ASA
security context or single mode ASA to one or more virtual sensors, or you can assign multiple security
contexts to the same virtual sensor. See the IPS documentation for more information about virtual
sensors, including the maximum number of sensors supported.
shows one security context paired with one virtual sensor (in inline mode), while two security
contexts share the same virtual sensor.
ASA
Main System
inside
IPS
IPS inspection
outside
VPN
Decryption
Firewall
Policy
Shun
message
2
51
158
Copied Traffic
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......












































