1-10
Cisco ASA Series CLI Configuration Guide
Chapter 1 Configuring IPsec and ISAKMP
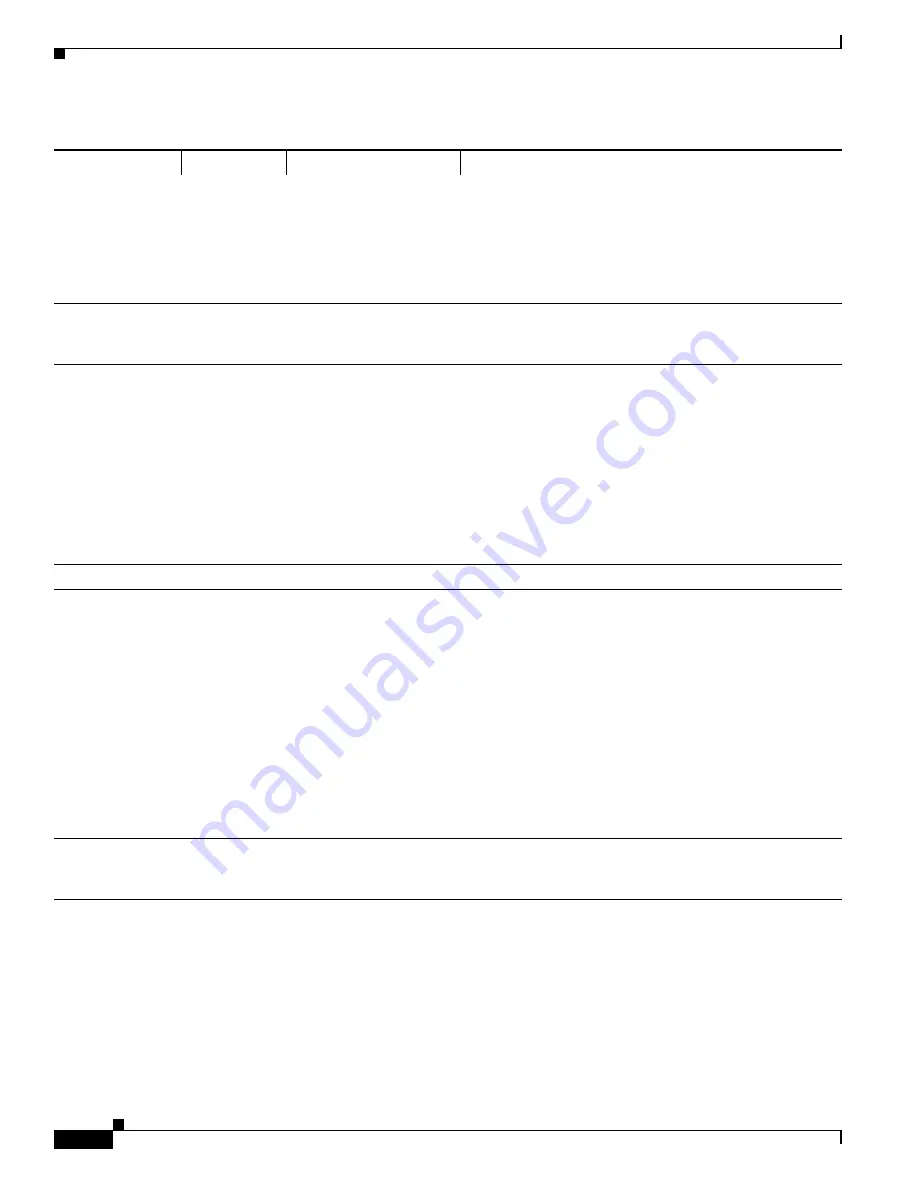
Configuring ISAKMP
sha256
SHA 2, 256-bit digest
Specifies the Secure Hash Algorithm SHA 2 with the
256-bit digest.
sha384
SHA 2, 384-bit digest
Specifies the Secure Hash Algorithm SHA 2 with the
384-bit digest.
sha512
SHA 2, 512-bit digest
Specifies the Secure Hash Algorithm SHA 2 with the
512-bit digest.
null
When AES-GCM is specified as the encryption algorithm,
an administrator can choose null as the IKEv2 integrity
algorithm.
encryption
des
3des
(default)
56-bit DES-CBC
168-bit Triple DES
Specifies the symmetric encryption algorithm that protects
data transmitted between two IPsec peers. The default is
168-bit Triple DES.
aes
aes-192
aes-256
The Advanced Encryption Standard supports key lengths of
128, 192, 256 bits.
aes-gcm
aes-gcm-192
aes-gcm-256
null
AES-GCM algorithm
options to use for IKEv2
encryption
The Advanced Encryption Standard supports key lengths of
128, 192, 256 bits.
policy_index
Accesses the IKEv2 policy sub-mode.
prf
sha
(default)
SHA-1 (HMAC variant)
Specifies the pseudo random function (PRF)—the
algorithm used to generate keying material.
md5
MD5 (HMAC variant)
The default is SHA-1. MD5 has a smaller digest and is
considered to be slightly faster than SHA-1. A successful
(but extremely difficult) attack against MD5 has occurred;
however, the HMAC variant IKE uses prevents this attack.
sha256
SHA 2, 256-bit digest
Specifies the Secure Hash Algorithm SHA 2 with the
256-bit digest.
sha384
SHA 2, 384-bit digest
Specifies the Secure Hash Algorithm SHA 2 with the
384-bit digest.
sha512
SHA 2, 512-bit digest
Specifies the Secure Hash Algorithm SHA 2 with the
512-bit digest.
priority
Extends the policy mode to support the additional IPsec V3
features and makes the AES-GCM and ECDH settings part
of the Suite B support.
Table 1-2
IKEv2 Policy Keywords for CLI Commands (continued)
Command
Keyword
Meaning
Description
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......








































