1-2
Cisco ASA Series CLI Configuration Guide
Appendix 1 Configuring an External Server for Authorization and Authentication
Configuring an External LDAP Server
For LDAP servers, any attribute name can be used to set the group policy for the session. The LDAP
attribute map that you configure on the ASA maps the LDAP attribute to the Cisco attribute
IETF-Radius-Class.
4.
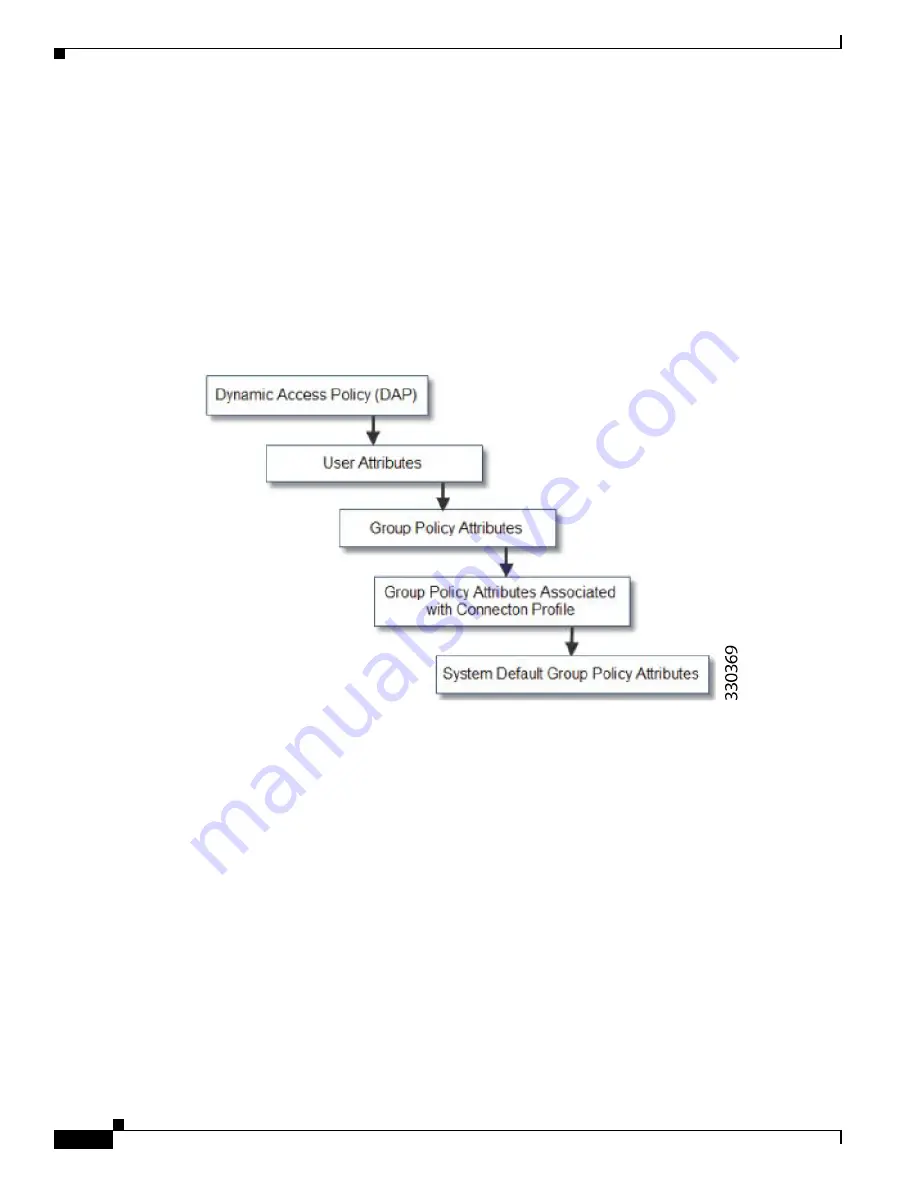
Group policy assigned by the Connection Profile (called tunnel-group in the CLI)—The Connection
Profile has the preliminary settings for the connection, and includes a default group policy applied
to the user before authentication. All users connecting to the ASA initially belong to this group,
which provides any attributes that are missing from the DAP, user attributes returned by the server,
or the group policy assigned to the user.
5.
Default group policy assigned by the ASA (DfltGrpPolicy)—System default attributes provide any
values that are missing from the DAP, user attributes, group policy, or connection profile.
Figure 1-1
Policy Enforcement Flow
Configuring an External LDAP Server
The VPN 3000 concentrator and the ASA/PIX 7.0 software required a Cisco LDAP schema for
authorization operations. Beginning with Version 7.1.x, the ASA performs authentication and
authorization using the native LDAP schema, and the Cisco schema is no longer needed.
You configure authorization (permission policy) using an LDAP attribute map. For examples, see the
“Active Directory/LDAP VPN Remote Access Authorization Examples” section on page 1-15
This section describes the structure, schema, and attributes of an LDAP server and includes the following
topics:
•
Organizing the ASA for LDAP Operations, page 1-3
•
Defining the ASA LDAP Configuration, page 1-5
•
Active Directory/LDAP VPN Remote Access Authorization Examples, page 1-15
The specific steps of these processes vary, depending on which type of LDAP server that you are using.
Summary of Contents for 5505 - ASA Firewall Edition Bundle
Page 28: ...Glossary GL 24 Cisco ASA Series CLI Configuration Guide ...
Page 61: ...P A R T 1 Getting Started with the ASA ...
Page 62: ......
Page 219: ...P A R T 2 Configuring High Availability and Scalability ...
Page 220: ......
Page 403: ...P A R T 2 Configuring Interfaces ...
Page 404: ......
Page 499: ...P A R T 2 Configuring Basic Settings ...
Page 500: ......
Page 533: ...P A R T 2 Configuring Objects and Access Lists ...
Page 534: ......
Page 601: ...P A R T 2 Configuring IP Routing ...
Page 602: ......
Page 745: ...P A R T 2 Configuring Network Address Translation ...
Page 746: ......
Page 845: ...P A R T 2 Configuring AAA Servers and the Local Database ...
Page 846: ......
Page 981: ...P A R T 2 Configuring Access Control ...
Page 982: ......
Page 1061: ...P A R T 2 Configuring Service Policies Using the Modular Policy Framework ...
Page 1062: ......
Page 1093: ...P A R T 2 Configuring Application Inspection ...
Page 1094: ......
Page 1191: ...P A R T 2 Configuring Unified Communications ...
Page 1192: ......
Page 1333: ...P A R T 2 Configuring Connection Settings and QoS ...
Page 1334: ......
Page 1379: ...P A R T 2 Configuring Advanced Network Protection ...
Page 1380: ......
Page 1475: ...P A R T 2 Configuring Modules ...
Page 1476: ......
Page 1549: ...P A R T 2 Configuring VPN ...
Page 1550: ......
Page 1965: ...P A R T 2 Configuring Logging SNMP and Smart Call Home ...
Page 1966: ......
Page 2059: ...P A R T 2 System Administration ...
Page 2060: ......
Page 2098: ...1 8 Cisco ASA Series CLI Configuration Guide Chapter 1 Troubleshooting Viewing the Coredump ...
Page 2099: ...P A R T 2 Reference ...
Page 2100: ......




































