34-29
Cisco Catalyst Blade Switch 3120 for HP Software Configuration Guide
OL-12247-01
Chapter 34 Configuring Network Security with ACLs
Configuring VLAN Maps
•
A Layer 2 interface can have only one MAC access list. If you apply a MAC access list to a Layer 2
interface that has a MAC ACL configured, the new ACL replaces the previously configured one.
Beginning in privileged EXEC mode, follow these steps to apply a MAC access list to control access to
a Layer 2 interface:
To remove the specified access group, use the no mac access-group {name} interface configuration
command.
This example shows how to apply MAC access list mac1 to a port to filter packets entering the port:
Switch(config)#
interface gigabitethernet1/0/2
Router(config-if)#
mac access-group mac1 in
Note
The mac access-group interface configuration command is only valid when applied to a physical
Layer 2 interface.You cannot use the command on EtherChannel port channels.
After receiving a packet, the switch checks it against the inbound ACL. If the ACL permits it, the switch
continues to process the packet. If the ACL rejects the packet, the switch discards it. When you apply an
undefined ACL to an interface, the switch acts as if the ACL has not been applied and permits all packets.
Remember this behavior if you use undefined ACLs for network security.
Configuring VLAN Maps
This section describes how to configure VLAN maps, which is the only way to control filtering within
a VLAN. VLAN maps have no direction. To filter traffic in a specific direction by using a VLAN map,
you need to include an ACL with specific source or destination addresses. If there is a match clause for
that type of packet (IP or MAC) in the VLAN map, the default action is to drop the packet if the packet
does not match any of the entries within the map. If there is no match clause for that type of packet, the
default is to forward the packet.
For complete syntax and usage information for the commands used in this section, see the command
reference for this release.
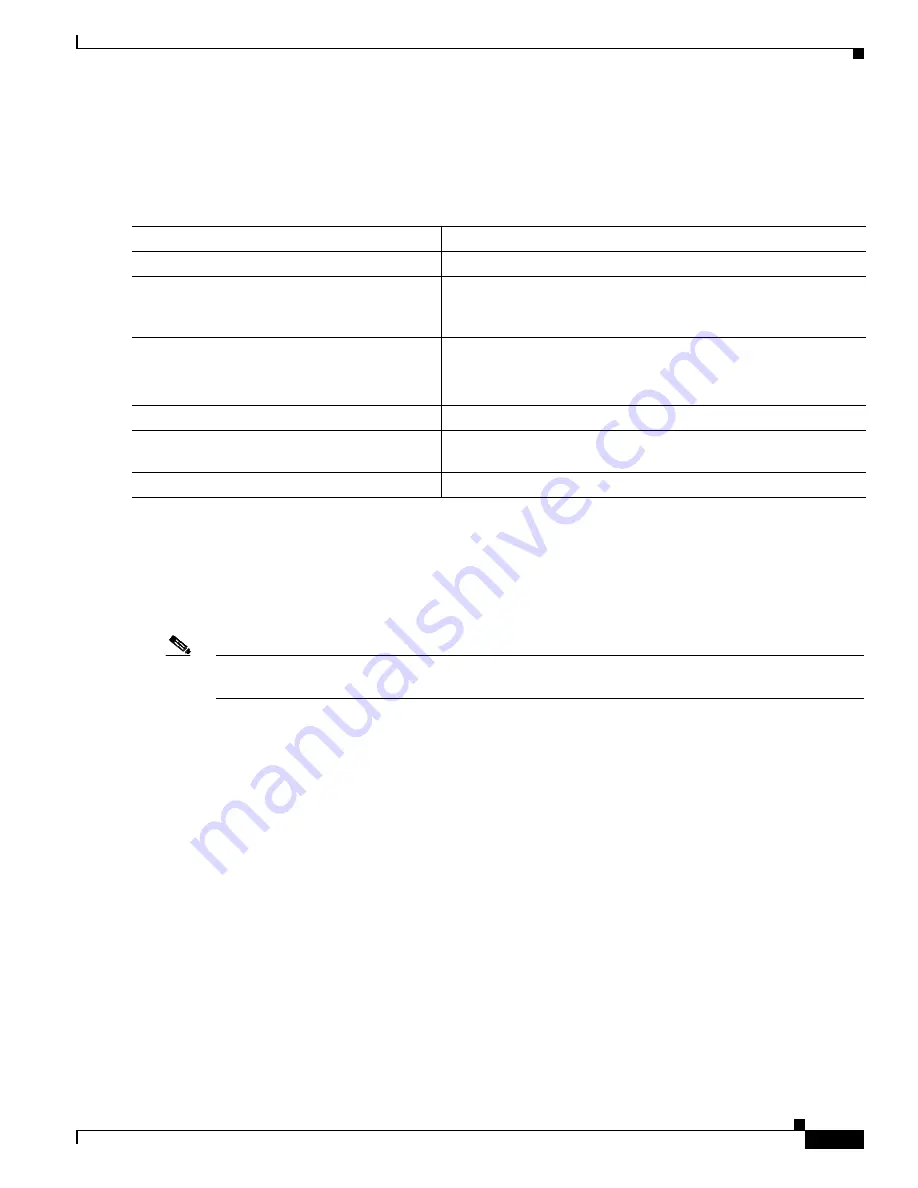
Command
Purpose
Step 1
configure terminal
Enter global configuration mode.
Step 2
interface interface-id
Identify a specific interface, and enter interface configuration
mode. The interface must be a physical Layer 2 interface (port
ACL).
Step 3
mac access-group {name} {in}
Control access to the specified interface by using the MAC access
list.
Port ACLs are supported only in the inbound direction.
Step 4
end
Return to privileged EXEC mode.
Step 5
show mac access-group [interface interface-id] Display the MAC access list applied to the interface or all Layer 2
interfaces.
Step 6
copy running-config startup-config
(Optional) Save your entries in the configuration file.













































