Chapter 2
Configuration
8
SubProduct
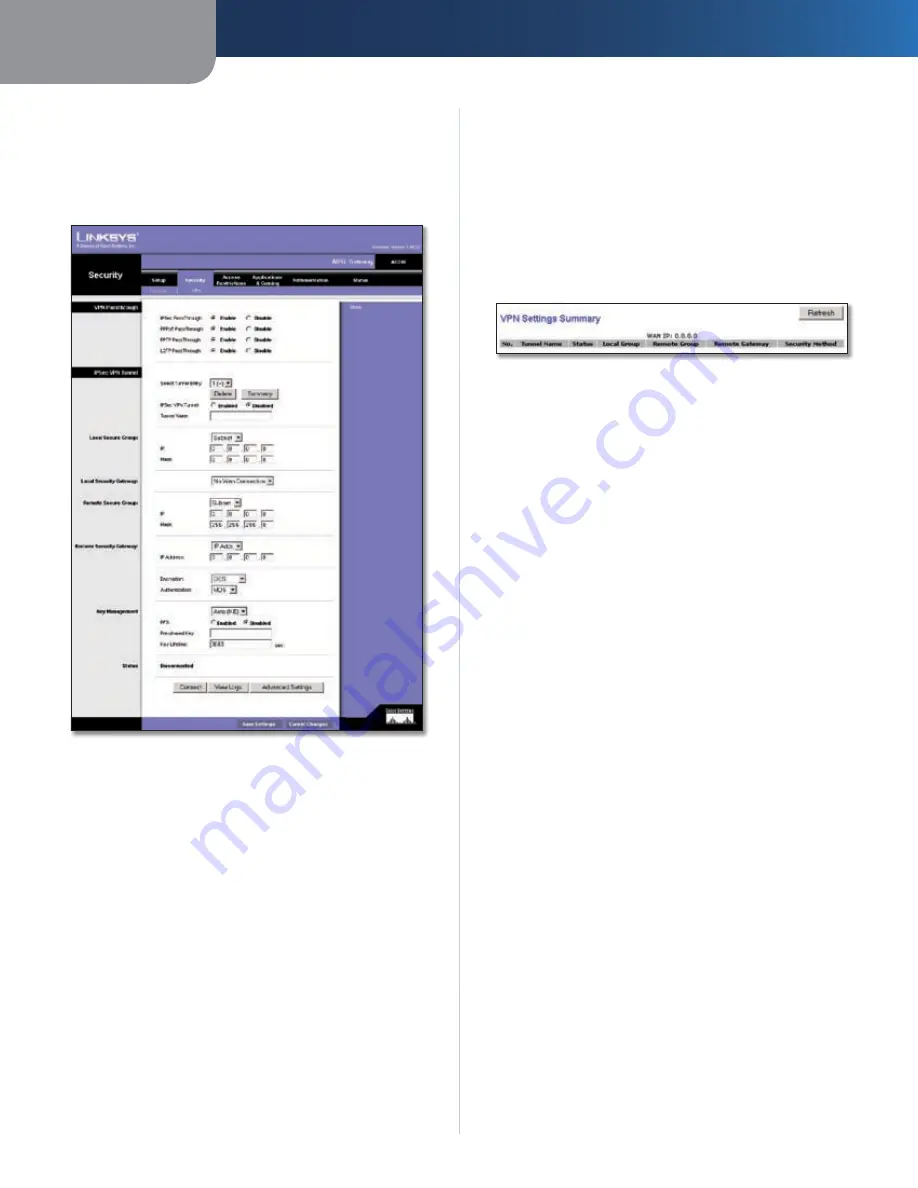
The Security Tab > VPN
Virtual Private Networking (VPN) is a security measure
that creates a secure connection between two remote
locations. The
Security
>
VPN
screen allows you to configure
your VPN settings to make your network more secure.
Security > VPN
VPN Passthrough
IPSec Passthrough
Internet Protocol Security (IPSec) is a
suite of protocols used to implement secure exchange of
packets at the IP layer. To allow IPSec Passthrough, click
Enable
. To disable IPSec Passthrough, click
Disable
.
PPTP Passthrough
Point-to-Point Tunneling Protocol
Passthrough is used to enable VPN sessions to a Windows
NT 4.0 or 2000 server. To allow PPTP Passthrough, click
Enable
. To disable PPTP Passthrough, click
Disable
.
L2TP Passthrough
Layering 2 Tunneling Protocol
Passthrough is used to enable the operation of a VPN over
the Internet.To allow L2TP Passthrough, click
Enable
. To
disable L2TP Passthrough, click
Disable
.
IPSec VPN Tunnel
The VPN Gateway creates a tunnel or channel between
two endpoints, so that the data or information between
these endpoints is secure.
To establish this tunnel, select the tunnel you wish to
create in the
Select Tunnel Entry
drop-down box. It is
possible to create up to five simultaneous tunnels. Then
click
Enabled
to enable the IPSec VPN tunnel. Once the
tunnel is enabled, enter the name of the tunnel in the
Tunnel Name
field. This is to allow you to identify multiple
tunnels and does not have to match the name used at the
other end of the tunnel. To delete a tunnel entry, select
the tunnel, then click
Delete
. To view a summary of the
settings, click
Summary
.
VPN Settings Summary
Local Secure Group and Remote Secure Group
The Local Secure Group is the computer(s) on your LAN
that can access the tunnel. The Remote Secure Group is
the computer(s) on the remote end of the tunnel that can
access the tunnel. These computers can be specified by a
Subnet, specific IP address, or range.
Local Security Gateway
Remote Security Gateway
The Remote Security Gateway is the VPN device, such as
a second VPN Gateway, on the remote end of the VPN
tunnel. Enter the IP Address or Domain of the VPN device
at the other end of the tunnel. The remote VPN device can
be another VPN Gateway, a VPN Server, or a computer with
VPN client software that supports IPSec. The IP Address
may either be static (permanent) or dynamic (changing),
depending on the settings of the remote VPN device. Make
sure that you have entered the IP Address correctly, or the
connection cannot be made. Note that this is NOT the IP
Address of the local VPN Gateway, but the IP Address of
the remote VPN Gateway or device with which you wish to
communicate. If you enter an IP address, only that specific
IP Address will be able to access the tunnel. If you select
Any
, any IP Address can access the tunnel.
Encryption
Using Encryption also helps make your
connection more secure. There are two different types of
encryption:
DES
(default) or 3DES (3DES is recommended
because it is more secure). You may choose either of these,
but it must be the same type of encryption that is being
used by the VPN device at the other end of the tunnel. Or,
you may choose not to encrypt by selecting
Disable
.
Authentication
Authentication acts as another level
of security. There are two types of authentication:
MD5
(default) and SHA (SHA is recommended because it is
more secure). As with encryption, either of these may be
selected, if the VPN device at the other end of the tunnel
is using the same type of authentication. Or, both ends of
the tunnel may choose to
Disable
authentication.












































