96
5.
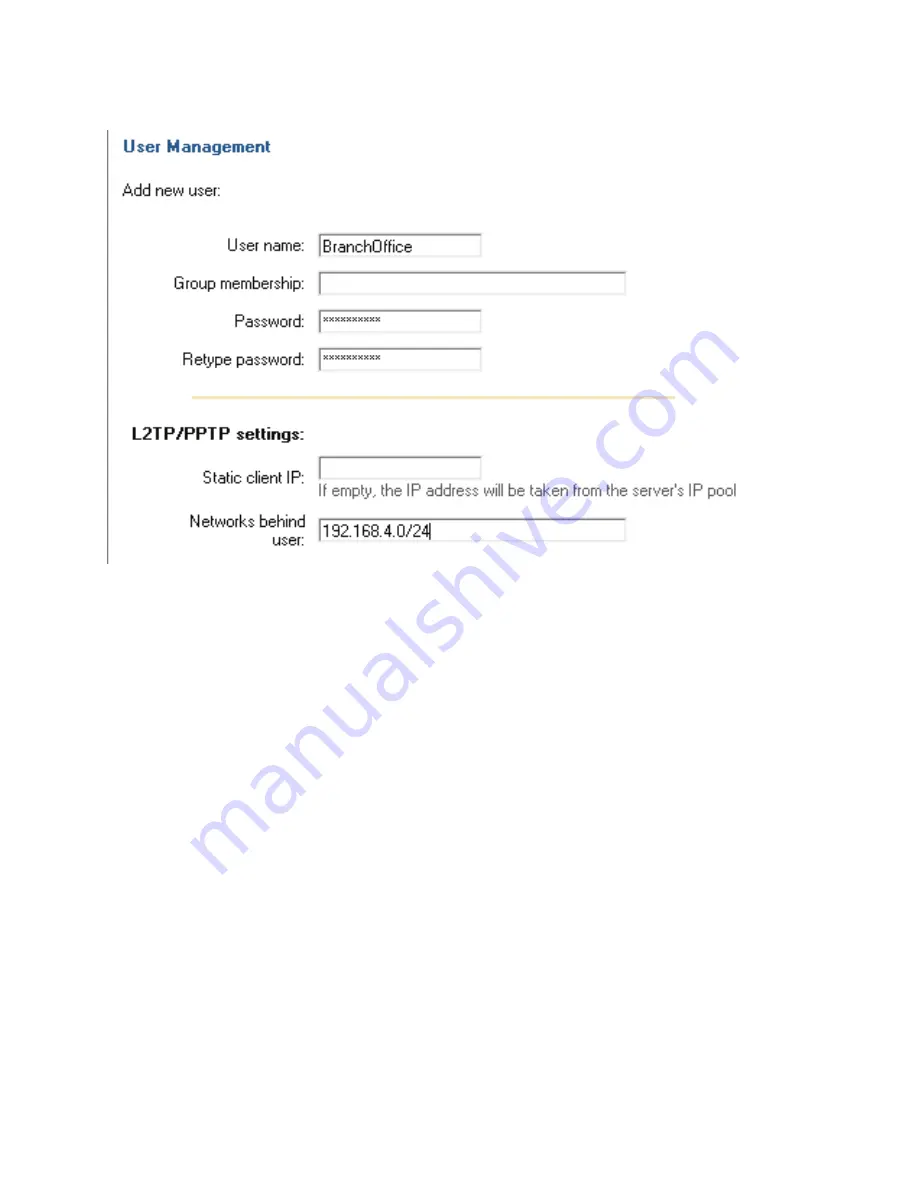
Add a new user,
Firewall->Users
:
Under
Users in local database
click
Add new
Name the new user
BranchOffice
Enter
password:
1234567890
Retype
password:
1234567890
Leave static client IP empty (could also be set to eg 192.168.1.200. If no IP is set
here the IP pool from the L2TP server settings are used).
Set Networks behind user to
192.168.4.0/24
Click
Apply
6.
Click
Activate
and wait for the firewall to restart.
This example will allow
all
traffic between the two offices. To get a more secure solution read
the
A more secure LAN-to-LAN VPN solution
section in this chapter.
Summary of Contents for DFL-700 - Security Appliance
Page 1: ...D Link DFL 700 Network Security Firewall Manual Building Networks for People 04 18 2005 TM ...
Page 102: ...102 5 Select Connect to the network at my workplace and click Next ...
Page 103: ...6 Select Virtual Private Network connection and click Next ...
Page 104: ...104 7 Name the connection MainOffice and click Next ...
Page 105: ...8 Select Do not dial the initial connection and click Next ...
Page 106: ...106 9 Type the IP address to the server 194 0 2 20 and click Next 10 Click Finish ...












































