The two above rules may both be carried out concurrently on the same connection. In this instance,
internal sender addresses will be translated to addresses in pubnet in a 1:1 relationship. In addition,
if anyone tries to connect to the public address of the web server, the destination address will be
changed to its private address.
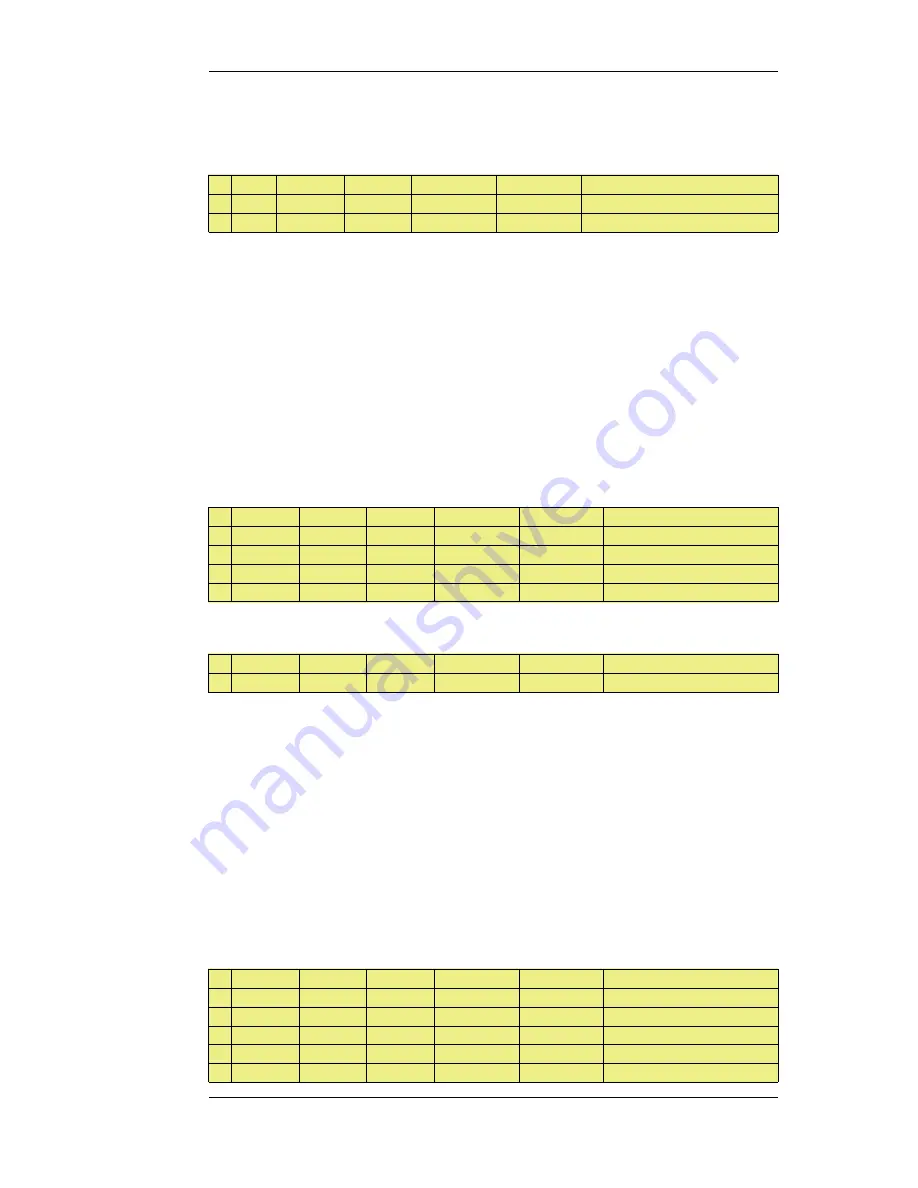
#
Action
Src Iface
Src Net
Dest Iface
Dest Net
Parameters
1
SAT
lan
lannet
wwwsrv_pub
TCP 80-85
SETDEST intrasrv 1080
2
SAT
any
all-nets
wwwsrv_pub
TCP 80-85
SETDEST wwwsrv-priv 1080
In this instance, both rules are set to translate the destination address, meaning that only one of them
will be carried out. If an attempt is made internally to communicate with the web servers public
address, it will instead be redirected to an intranet server. If any other attempt is made to
communicate with the web servers public address, it will be redirected to the private address of the
publicly accessible web server.
Again, note that the above rules require a matching Allow rule at a later point in the rule set in order
to work.
7.4.7. SAT and FwdFast Rules
It is possible to employ static address translation in conjunction with FwdFast rules, although return
traffic must be explicitly granted and translated.
The following rules make up a working example of static address translation using FwdFast rules to
a web server located on an internal network:
#
Action
Src Iface
Src Net
Dest Iface
Dest Net
Parameters
1
SAT
any
all-nets
core
wan_ip
http SETDEST wwwsrv 80
2
SAT
lan
wwwsrv
any
all-nets
80 -> All SETSRC wan_ip 80
3
FwdFast
any
all-nets
core
wan_ip
http
4
FwdFast
lan
wwwsrv
any
all-nets
80 -> All
We now add a NAT rule to allow connections from the internal network to the Internet:
#
Action
Src Iface
Src Net
Dest Iface
Dest Net
Parameters
5
NAT
lan
lannet
any
all-nets
All
What happens now is as follows:
•
External traffic to wan_ip:80 will match rules 1 and 3, and will be sent to wwwsrv. Correct.
•
Return traffic from wwwsrv:80 will match rules 2 and 4, and will appear to be sent from
wan_ip:80. Correct.
•
Internal traffic to wan_ip:80 will match rules 1 and 3, and will be sent to wwwsrv. This is almost
correct; the packets will arrive at wwwsrv, but:
•
Return traffic from wwwsrv:80 to internal machines will be sent directly to the machines
themselves. This will not work, as the packets will be interpreted as coming from the wrong
address.
We will now try moving the NAT rule between the SAT and FwdFast rules:
#
Action
Src Iface
Src Net
Dest Iface
Dest Net
Parameters
1
SAT
any
all-nets
core
wan_ip
http SETDEST wwwsrv 80
2
SAT
lan
wwwsrv
any
all-nets
80 -> All SETSRC wan_ip 80
3
NAT
lan
lannet
any
all-nets
All
4
FwdFast
any
all-nets
core
wan_ip
http
5
FwdFast
lan
wwwsrv
any
all-nets
80 -> All
7.4.7. SAT and FwdFast Rules
Chapter 7. Address Translation
358
Summary of Contents for NetDefend DFL-260E
Page 27: ...1 3 NetDefendOS State Engine Packet Flow Chapter 1 NetDefendOS Overview 27...
Page 79: ...2 7 3 Restore to Factory Defaults Chapter 2 Management and Maintenance 79...
Page 146: ...3 9 DNS Chapter 3 Fundamentals 146...
Page 227: ...4 7 5 Advanced Settings for Transparent Mode Chapter 4 Routing 227...
Page 241: ...5 4 IP Pools Chapter 5 DHCP Services 241...
Page 339: ...6 7 Blacklisting Hosts and Networks Chapter 6 Security Mechanisms 339...
Page 360: ...7 4 7 SAT and FwdFast Rules Chapter 7 Address Translation 360...
Page 382: ...8 3 Customizing HTML Pages Chapter 8 User Authentication 382...
Page 386: ...The TLS ALG 9 1 5 The TLS Alternative for VPN Chapter 9 VPN 386...
Page 439: ...Figure 9 3 PPTP Client Usage 9 5 4 PPTP L2TP Clients Chapter 9 VPN 439...
Page 450: ...9 7 6 Specific Symptoms Chapter 9 VPN 450...
Page 488: ...10 4 6 Setting Up SLB_SAT Rules Chapter 10 Traffic Management 488...
Page 503: ...11 6 HA Advanced Settings Chapter 11 High Availability 503...
Page 510: ...12 3 5 Limitations Chapter 12 ZoneDefense 510...
Page 533: ...13 9 Miscellaneous Settings Chapter 13 Advanced Settings 533...









































