i.
HTML form - The user is presented with an HTML page for authentication which is filled
in and the data sent back to NetDefendOS with a POST.
ii.
BASIC authentication - This sends a 401 - Authentication Required message back to
the browser which will cause it to use its own inbuilt dialog to ask the user for a
username/password combination. A Realm String can optionally be specified which will
appear in the browser's dialog.
HTML form
is recommended over BASICAUTH because, in some cases, the browser
might hold the login data in its cache.
iii.
MAC authentication - Authentication is performed for HTTP and HTTPS clients without a
login screen. Instead, the MAC address of the connecting client is used as the username.
The password is the MAC address or a specified string.
MAC authentication is explained further in
Section 8.3, “ARP Authentication”
•
If the Agent is set to
HTTPS
then the Host Certificate and Root Certificate(s) have to be
chosen from a list of certificates already loaded into NetDefendOS. Certificate chaining is
supported for the root certificate.
IP Rules are Needed
HTTP authentication cannot operate unless a rule is added to the IP rule set to explicitly allow
authentication to take place. This is also true with HTTPS.
If we consider the example of a number of clients on the local network
lannet
who would like
access to the public Internet through the
wan
interface then the IP rule set would contain the
following rules:
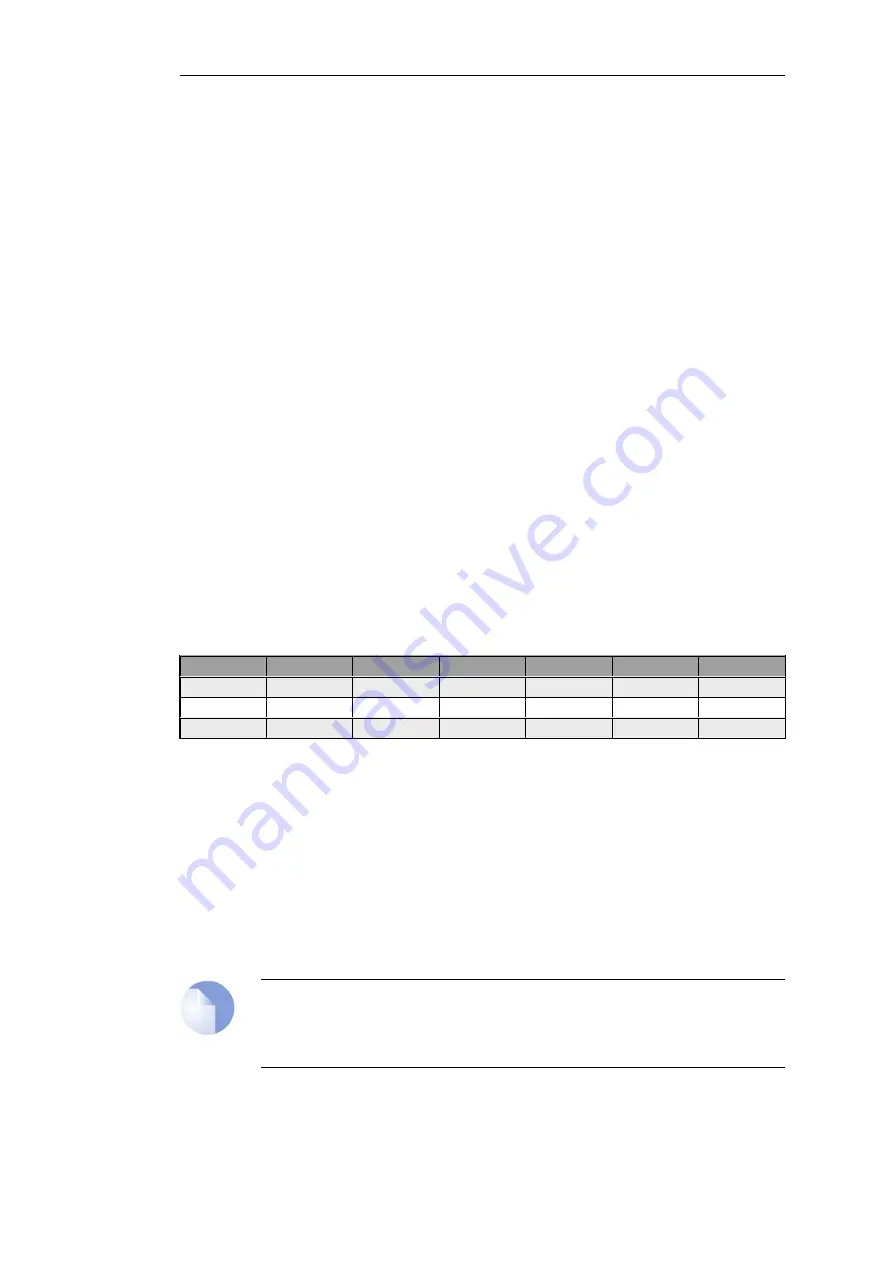
#
Action
Src Interface
Src Network
Dest Interface
Dest Network
Service
1
Allow
lan
lannet
core
lan_ip
http-all
2
NAT
lan
trusted_users
wan
all-nets
http-all
3
NAT
lan
lannet
wan
all-nets
dns-all
The first rule allows the authentication process to take place and assumes the client is trying to
access the
lan_ip
IP address, which is the IP address of the interface on the NetDefend Firewall
where the local network connects.
The second rule allows normal surfing activity but we cannot just use
lannet
as the source
network since the rule would trigger for any unauthenticated client from that network. Instead,
the source network is an administrator defined IP object called
trusted_users
which is the same
network as
lannet
but has additionally either the Authentication option No Defined Credentials
enabled
or
has an Authentication Group assigned to it (which is the same group as that assigned
to the users).
The third rule allows DNS lookup of URLs.
Note
Do not modify the default http-all service in the IP rules above. This can cause
authentication to fail.
Forcing Users to a Login Page
Chapter 8: User Authentication
628
Summary of Contents for NetDefendOS
Page 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Page 32: ...Chapter 1 NetDefendOS Overview 32 ...
Page 144: ...Chapter 2 Management and Maintenance 144 ...
Page 284: ...Chapter 3 Fundamentals 284 ...
Page 392: ...Chapter 4 Routing 392 ...
Page 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Page 420: ...Chapter 5 DHCP Services 420 ...
Page 573: ...Chapter 6 Security Mechanisms 573 ...
Page 607: ...Chapter 7 Address Translation 607 ...
Page 666: ...Chapter 8 User Authentication 666 ...
Page 775: ...Chapter 9 VPN 775 ...
Page 819: ...Chapter 10 Traffic Management 819 ...
Page 842: ...Chapter 11 High Availability 842 ...
Page 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Page 879: ...Chapter 13 Advanced Settings 879 ...









































