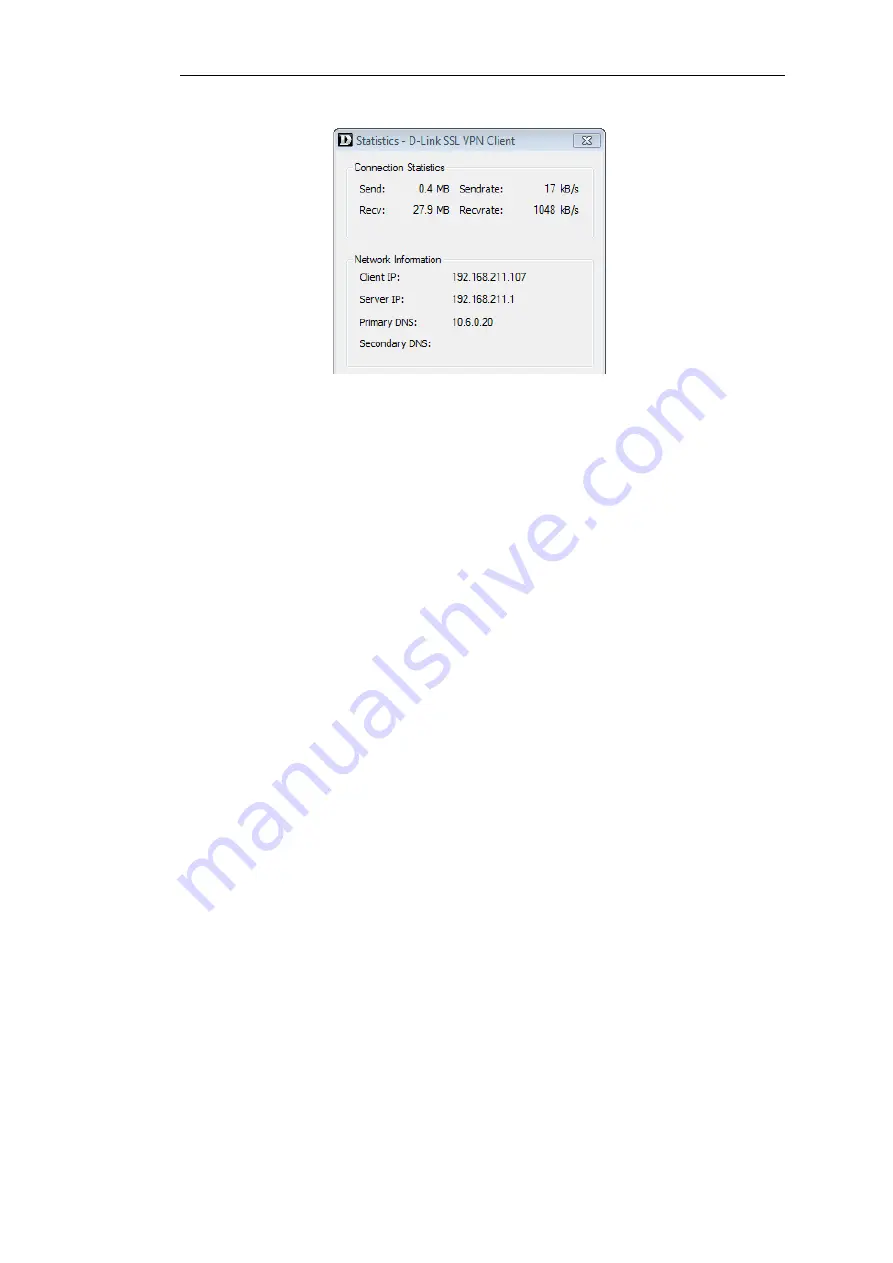
Figure 9.7. The SSL VPN Client Statistics
SSL VPN Client Operation
Whenever the SSL VPN client application runs, the following happens:
•
A route is added to the Windows routing table. This route is equivalent to a NetDefendOS
default
all-nets
route.
•
The added default route directs all traffic from the Windows client through the SSL tunnel.
When the Windows SSL VPN client application ends, the SSL tunnel is closed and the default
route in the Windows routing table is removed, returning the routing table to its original
state.
•
An SSL connection is made to the configured Ethernet interface on a NetDefend Firewall and
the next available IP address is handed out to the client from the associated SSL VPN object's
IP pool.
In addition, a single route for the client is added to the NetDefendOS routing table. This route
maps the handed out client IP address to the associated SSL VPN interface.
•
Traffic can now flow between the client and the firewall, subject to NetDefendOS IP rules.
Specifying IP Rules for Traffic Flow
No IP rules need to be specified for the setup of an SSL VPN tunnel itself, provided that the
advanced setting SSLVPNBeforeRules is enabled. However, appropriate IP rules need to be
specified by the administrator to allow traffic to flow through the tunnel.
Since SSL VPN connections originate from the client side, the SSL VPN interface object should be
the source interface of the IP rule and the source network should be the range of possible IP
addresses that the clients can be given. Specifying the source network as
all-nets
would of course
work but it always more secure to use the narrowest possible IP address range.
For more information about specifying IP rules see
Section 3.6, “IP Rules and IP Policies”
Client Cleanup
Should the SSL VPN client application terminate prematurely for some reason, the Windows
Chapter 9: VPN
758
Summary of Contents for NetDefendOS
Page 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Page 32: ...Chapter 1 NetDefendOS Overview 32 ...
Page 144: ...Chapter 2 Management and Maintenance 144 ...
Page 284: ...Chapter 3 Fundamentals 284 ...
Page 392: ...Chapter 4 Routing 392 ...
Page 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Page 420: ...Chapter 5 DHCP Services 420 ...
Page 573: ...Chapter 6 Security Mechanisms 573 ...
Page 607: ...Chapter 7 Address Translation 607 ...
Page 666: ...Chapter 8 User Authentication 666 ...
Page 775: ...Chapter 9 VPN 775 ...
Page 819: ...Chapter 10 Traffic Management 819 ...
Page 842: ...Chapter 11 High Availability 842 ...
Page 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Page 879: ...Chapter 13 Advanced Settings 879 ...




































