through the NetDefend Firewall.
Grouping IP Addresses
It can be quicker when dealing with many IP addresses to group all the addresses into a single
group IP object and then use that object in a single defined route. In the above example,
85.12.184.39
and
194.142.215.15
could be grouped into a single object in this way.
Using NAT
NAT should not be enabled for NetDefendOS in Transparent Mode since, as explained previously,
the NetDefend Firewall is acting like a level 2 switch and address translation is done at the higher
IP OSI layer.
The other consequence of not using NAT is that IP addresses of users accessing the Internet
usually need to be public IPv4 addresses.
If NATing needs to be performed in the example above to hide individual addresses from the
Internet, it would have to be done by a device (possibly another NetDefend Firewall) between
the
192.168.10.0/24
network and the public Internet. In this case, internal, private IPv4 addresses
could be used by the users on Ethernet network
pn2
.
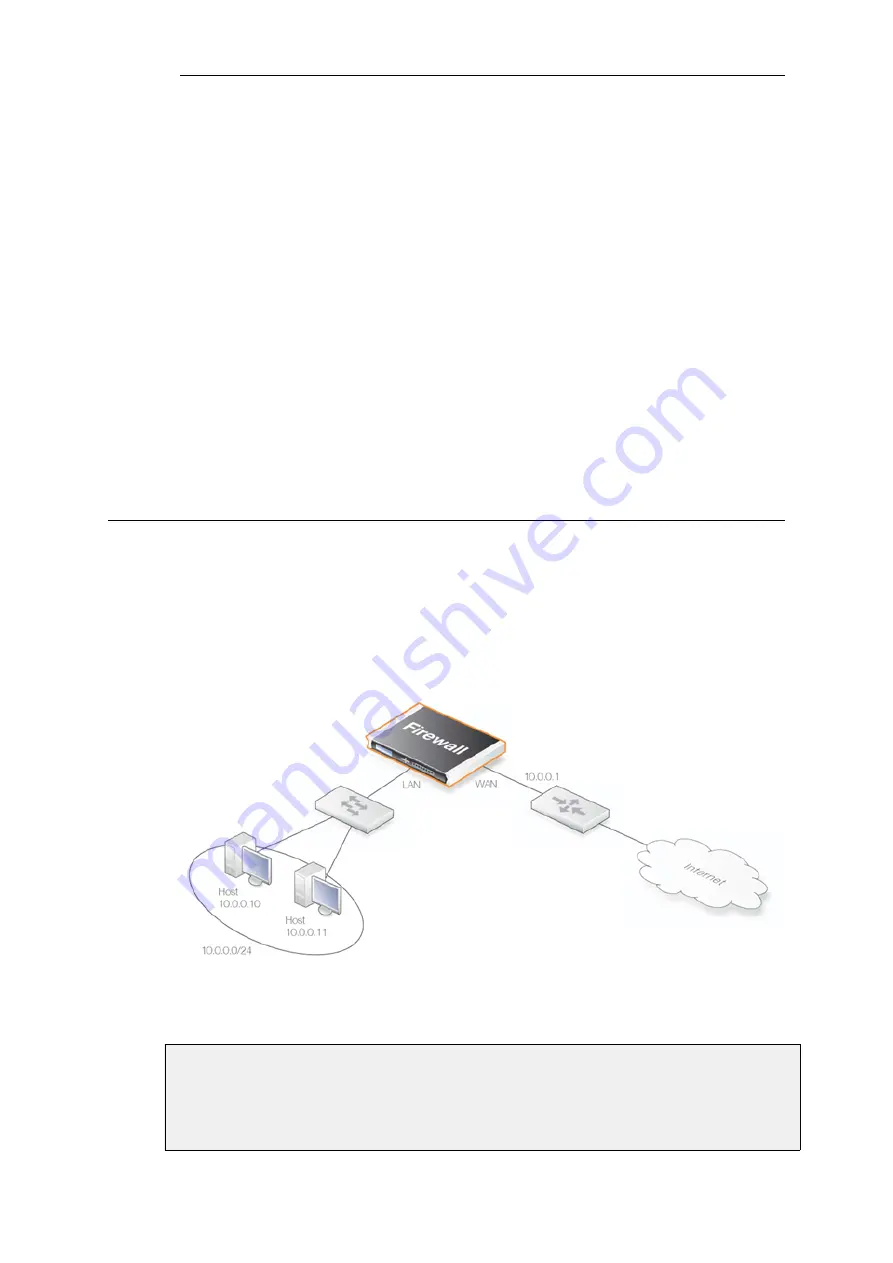
4.8.3. A Transparent Mode Use Case
In the use case illustrated below, a NetDefend Firewall in transparent mode is placed between an
Internet access router and the internal network. The router is used to share the Internet
connection with a single public IPv4 address. The internal NATed network behind the firewall is
in the 10.0.0.0/24 address space. Clients on the internal network are allowed to access the
Internet via the HTTP protocol. The actual setup steps are listed in the example below.
Figure 4.25. Transparent Mode Use Case
Example 4.22. A Transparent Mode Use Case
Command-Line Interface
Chapter 4: Routing
386
Summary of Contents for NetDefendOS
Page 30: ...Figure 1 3 Packet Flow Schematic Part III Chapter 1 NetDefendOS Overview 30 ...
Page 32: ...Chapter 1 NetDefendOS Overview 32 ...
Page 144: ...Chapter 2 Management and Maintenance 144 ...
Page 284: ...Chapter 3 Fundamentals 284 ...
Page 392: ...Chapter 4 Routing 392 ...
Page 419: ... Host 2001 DB8 1 MAC 00 90 12 13 14 15 5 Click OK Chapter 5 DHCP Services 419 ...
Page 420: ...Chapter 5 DHCP Services 420 ...
Page 573: ...Chapter 6 Security Mechanisms 573 ...
Page 607: ...Chapter 7 Address Translation 607 ...
Page 666: ...Chapter 8 User Authentication 666 ...
Page 775: ...Chapter 9 VPN 775 ...
Page 819: ...Chapter 10 Traffic Management 819 ...
Page 842: ...Chapter 11 High Availability 842 ...
Page 866: ...Default Enabled Chapter 13 Advanced Settings 866 ...
Page 879: ...Chapter 13 Advanced Settings 879 ...
















































