13
Parameter Description
Key Length
You may select the 64-bit or 128-bit to encrypt transmitted data.
Larger key length will provide higher level of security, but the
throughput will be lower.
Key1 ~ Key4
The keys are used to encrypt data transmitted in the wireless
network. Fill the text box by following the rules below.
•
64-bit
– Input 10 digit Hex values (in the “A-F”, “a-f” and “0-9”
range) as the encryption keys. For example: “0123456aef“.
•
128-bit
– Input 26 digit Hex values (in the “A-F”, “a-f” and “0-
9” range) as the encryption keys. For example:
“01234567890123456789abcdef“.
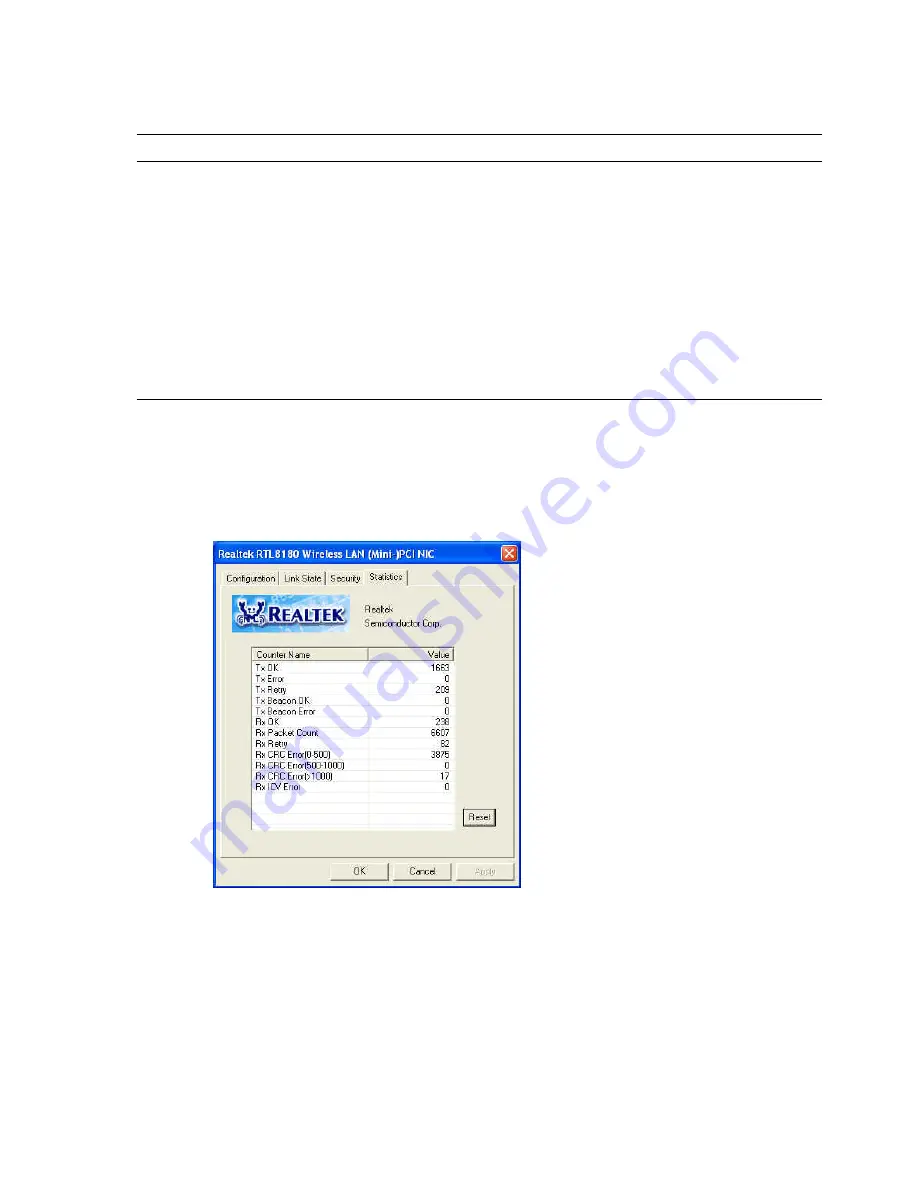
3.4 Statistics
In the
“Statistics”
, you can get the real time information about the packet transmission and
receiving status.



































