EUB9706 –300Mbps Wireless N USB Adapter Version 1.0
35
Click on the Apply button to save the changes.
Show Password check box. If you want to make sure the accuracy of
password you type, click the Show Password box to check it.
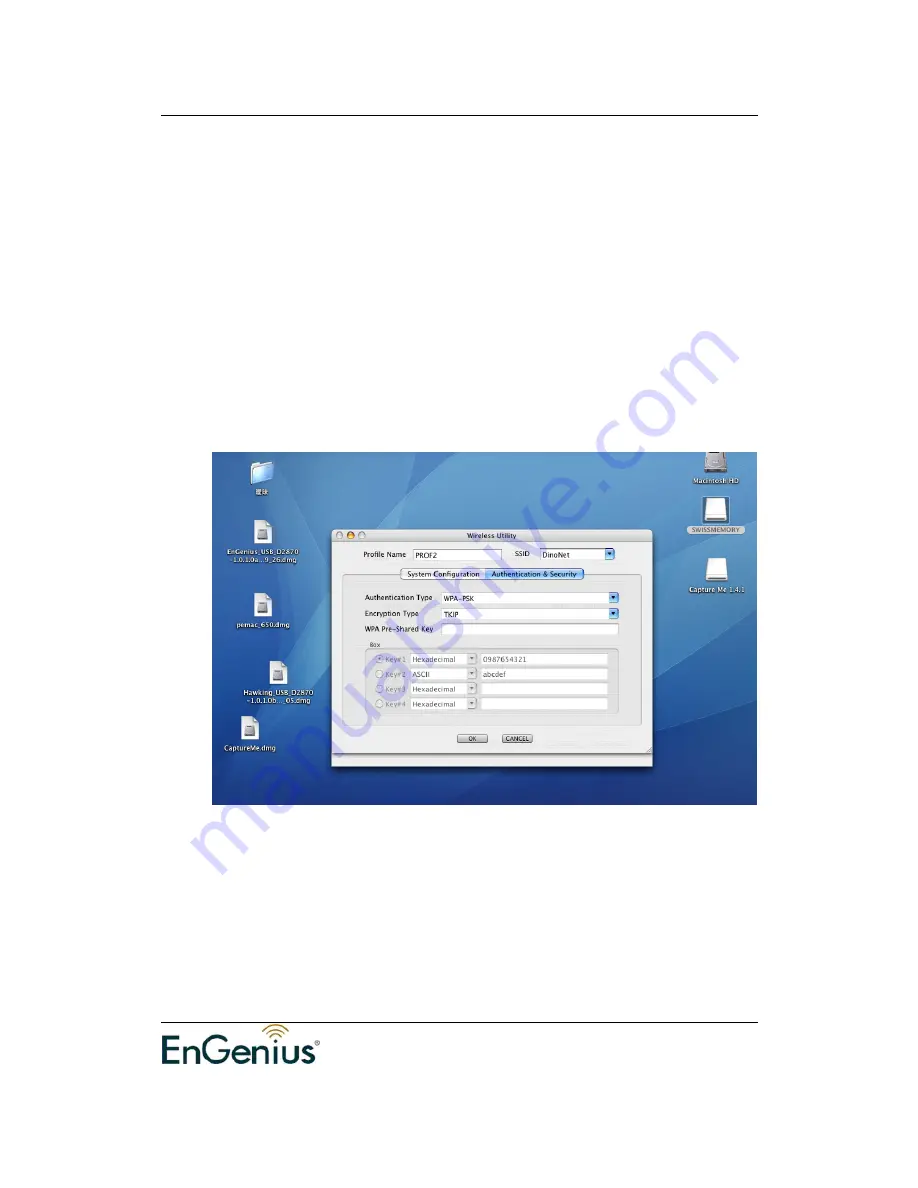
WPA-PSK Authentication & TKIP, AES Encryption
WPA – PSK (Pre-shared Key) is used in a Pre Shared Key mode that does not
require an authentication server. Access to the Internet and the rest of the
wireless network services is allowed only if the pre-shared key of the computer
matches that of the Access Point. This approach offers the simplicity of the WEP
key, but uses stronger TKIP encryption. EAP (Extensible Authentication Protocol)
is an extension to the PPP protocol that enables a variety of authentication
protocols to be used. It passes through the exchange of authentication messages,
allowing the authentication software stored in a server to interact with its
counterpart in the client.
Authentication Type: Select WPA or WPA2 from the drop-down list.
Encryption: Select TKIP or AES from the drop-down list.
WPA Preshared key: Enter a pass phrase which is between 8 and 32
characters long.
Click on the Apply button to save the changes.
Show Password check box. If you want to make sure the accuracy of
password you type, click the Show Password box to check it.
















































