114
01-28006-0100-20041105
Fortinet Inc.
Access profiles
System administration
Access profiles
Go to
System > Admin > Access Profile
to add access profiles for FortiGate
administrators. Each administrator account belongs to an access profile. You can
create access profiles that deny access to or allow read only, write only, or both read
and write access to FortiGate features.
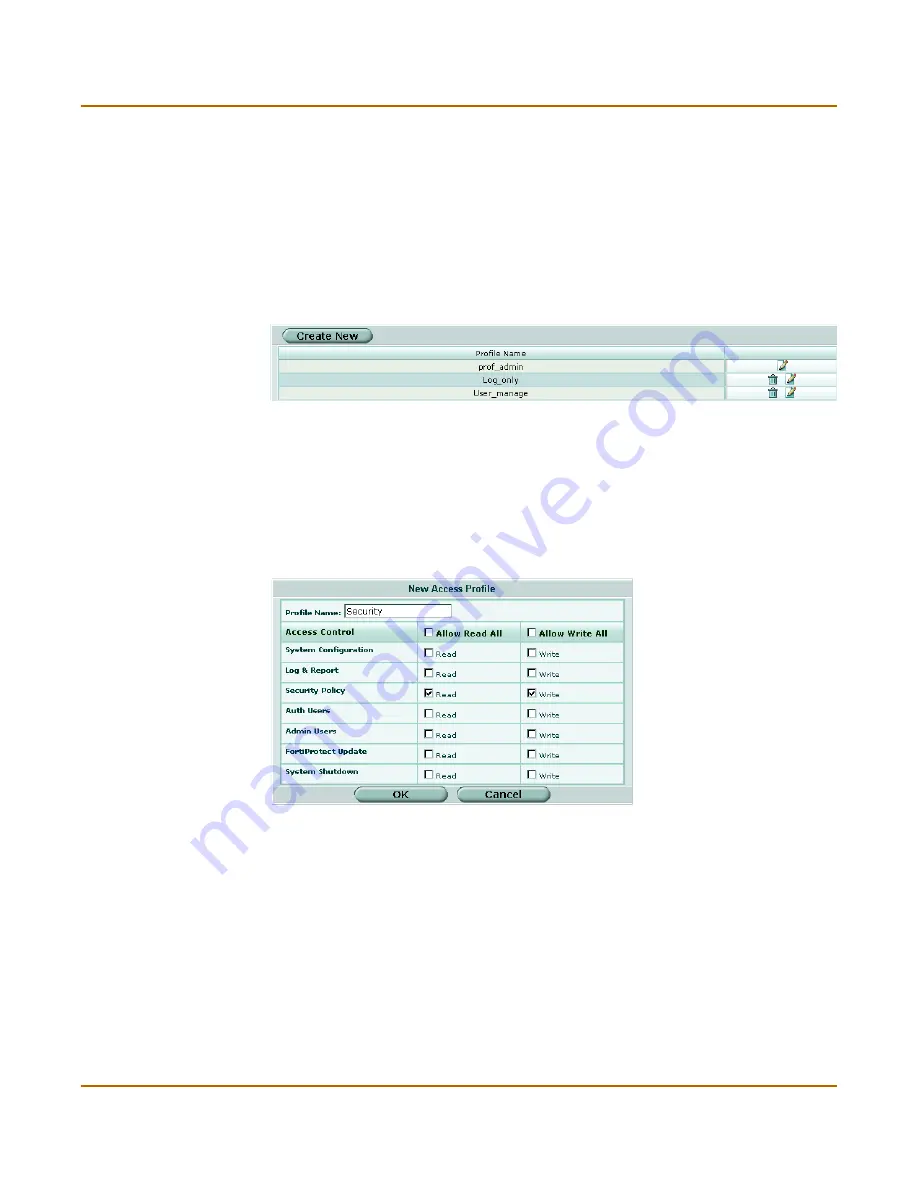
Access profile list
Figure 42: Access profile list
Access profile options
Figure 43: Access profile option
Create New
Add a new access profile.
Profile Name
The name of the access profile.
The Delete, and Edit icons.
You cannot delete the prof_admin access profile.
Profile Name
Enter the name of the access profile.
Access Control
Access Control lists the items that can be controlled by the access profile.
Allow Read All
Select Allow Read All to give an administrator read privilege on all the items
under Access Control.
Allow Write All
Select Allow Write All to give an administrator write privilege on all the items
under Access Control.
System
Configuration
Allow or deny access to the system status, interface, virtual domain, HA,
routing, option, SNMP, time, and replacement message features.
Log & Report
Allow or deny access to the log setting, log access, and alert email features.
Security Policy
Allow or deny access to the firewall, VPN, IPS, and antivirus features.
Auth Users
Allow or deny access to the authorized users feature.
Summary of Contents for FortiGate FortiGate-500A
Page 24: ...24 01 28006 0100 20041105 Fortinet Inc Customer service and technical support Introduction...
Page 46: ...46 01 28006 0100 20041105 Fortinet Inc Changing the FortiGate firmware System status...
Page 72: ...72 01 28006 0100 20041105 Fortinet Inc FortiGate IPv6 support System network...
Page 80: ...80 01 28006 0100 20041105 Fortinet Inc Dynamic IP System DHCP...
Page 110: ...110 01 28006 0100 20041105 Fortinet Inc FortiManager System config...
Page 116: ...116 01 28006 0100 20041105 Fortinet Inc Access profiles System administration...
Page 134: ...134 01 28006 0100 20041105 Fortinet Inc Shutdown System maintenance...
Page 248: ...248 01 28006 0100 20041105 Fortinet Inc CLI configuration Users and authentication...
Page 324: ...324 01 28006 0100 20041105 Fortinet Inc CLI configuration Antivirus...
Page 386: ...386 01 28006 0100 20041105 Fortinet Inc Glossary...
Page 394: ...394 01 28006 0100 20041105 Fortinet Inc Index...








































