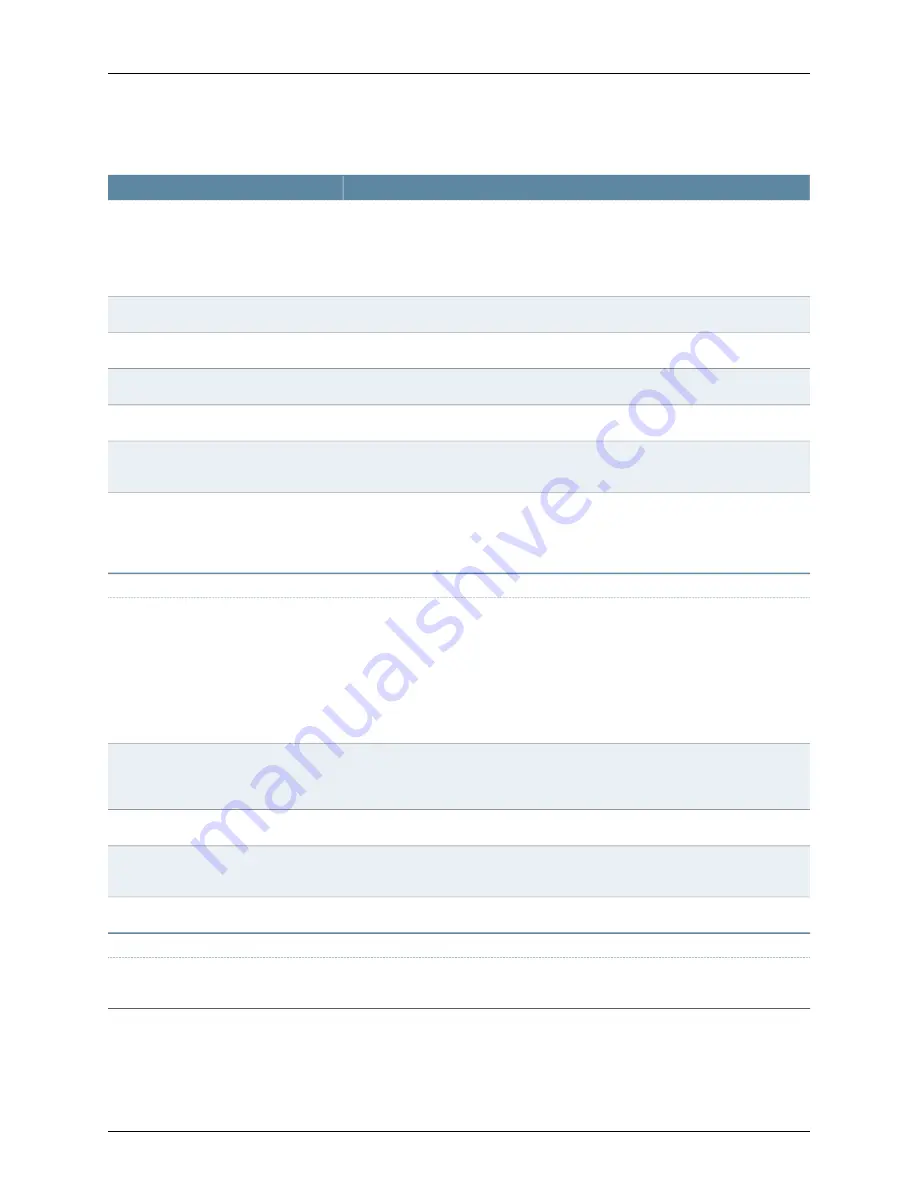
Table 38: Configuring Network Connect Connection Profile Details
(continued)
Your Action
Options
Select of the following options from the drop-down list:
•
Custom DNS Settings
—This option sends the custom device DNS settings.
•
DHCP DNS Settings
—This option sends the values the DHCP server sends to the
device.
DNS Settings
Enter the IP address for the primary DNS.
Primary DNS
Enter the IP address for the secondary DNS.
Secondary DNS
Enter the DNS domain(s), such as “yourcompany.com”, “yourcompany.net”.
DNS Domain(s)
Enter the WINS resolution name or IP address.
WINS
Select this check box if you want to create an allow rule for the DNS server.
Auto-allow IP's in DNS/WINS settings
(only for split-tunnel enabled mode)
Select one of the following options from the drop-down list:
•
Search client DNS first, then the device.
•
Search the device’s DNS servers first, then the client.
DNS search order
Proxy tab
Select one of the following options from the drop-down list:
•
No proxy server
—Specifies that the new profile requires no proxy server.
•
Automatic (URL for PAC file on another server)
—Specifies the URL of the server
on which the PAC file resides, and the frequency (in minutes) with which Network
Connect polls the server for an updated version of the PAC file.
•
Manual configuration
—Specifies the IP address or the hostname of the server
and provides the port assignment.
Network Connect proxy server
configuration
Enter the PAC server address. This option is enabled only when you select
Automatic
(URL for PAC file on another server)
from the Network Connect proxy server
configuration option.
PAC Server Address
Enter the PAC update frequency. The default value is 10.
PAC Update Frequency (minutes)
Enter the static proxy server address. This option is enabled only when you select
Manual configuration
from the Network Connect proxy server configuration option.
Static Proxy Server
Enter the static proxy port value. The default value is 0.
Static Proxy Port
Roles Selection tab
Select the members from the Members list. You can add or remove the non-members
to members by using the Add/Remove options.
Roles Selections
Related
Documentation
Configuring Web Rewriting Resource Policies (NSM Procedure) on page 151
•
•
Defining Network Connect Split Tunneling Policies (NSM Procedure) on page 159
Copyright © 2010, Juniper Networks, Inc.
158
Configuring Secure Access Devices Guide
Summary of Contents for NETWORK AND SECURITY MANAGER
Page 6: ...Copyright 2010 Juniper Networks Inc vi...
Page 12: ...Copyright 2010 Juniper Networks Inc xii Configuring Secure Access Devices Guide...
Page 18: ...Copyright 2010 Juniper Networks Inc xviii Configuring Secure Access Devices Guide...
Page 20: ...Copyright 2010 Juniper Networks Inc 2 Configuring Secure Access Devices Guide...
Page 28: ...Copyright 2010 Juniper Networks Inc 10 Configuring Secure Access Devices Guide...
Page 40: ...Copyright 2010 Juniper Networks Inc 22 Configuring Secure Access Devices Guide...
Page 46: ...Copyright 2010 Juniper Networks Inc 28 Configuring Secure Access Devices Guide...
Page 50: ...Copyright 2010 Juniper Networks Inc 32 Configuring Secure Access Devices Guide...
Page 52: ...Copyright 2010 Juniper Networks Inc 34 Configuring Secure Access Devices Guide...
Page 82: ...Copyright 2010 Juniper Networks Inc 64 Configuring Secure Access Devices Guide...
Page 110: ...Copyright 2010 Juniper Networks Inc 92 Configuring Secure Access Devices Guide...
Page 154: ...Copyright 2010 Juniper Networks Inc 136 Configuring Secure Access Devices Guide...
Page 224: ...Copyright 2010 Juniper Networks Inc 206 Configuring Secure Access Devices Guide...
Page 234: ...Copyright 2010 Juniper Networks Inc 216 Configuring Secure Access Devices Guide...
Page 288: ...Copyright 2010 Juniper Networks Inc 270 Configuring Secure Access Devices Guide...
Page 300: ...Copyright 2010 Juniper Networks Inc 282 Configuring Secure Access Devices Guide...
Page 310: ...Copyright 2010 Juniper Networks Inc 292 Configuring Secure Access Devices Guide...
Page 312: ...Copyright 2010 Juniper Networks Inc 294 Configuring Secure Access Devices Guide...
Page 320: ...Copyright 2010 Juniper Networks Inc 302 Configuring Secure Access Devices Guide...
Page 322: ...Copyright 2010 Juniper Networks Inc 304 Configuring Secure Access Devices Guide...
Page 337: ...PART 6 Index Index on page 321 319 Copyright 2010 Juniper Networks Inc...
Page 338: ...Copyright 2010 Juniper Networks Inc 320 Configuring Secure Access Devices Guide...
Page 340: ...Copyright 2010 Juniper Networks Inc 322 Configuring Secure Access Devices Guide...
















































