Device Configuration 5 - 331
6. Click the
Add Peer
button to add the Tunnel peer information into the
Peer(s)
table. This table lists all the peers configured
for the VPN Tunnel.
7. Click the
Next
button to go to the next configuration screen. Use the
Back
button to go to the previous step.
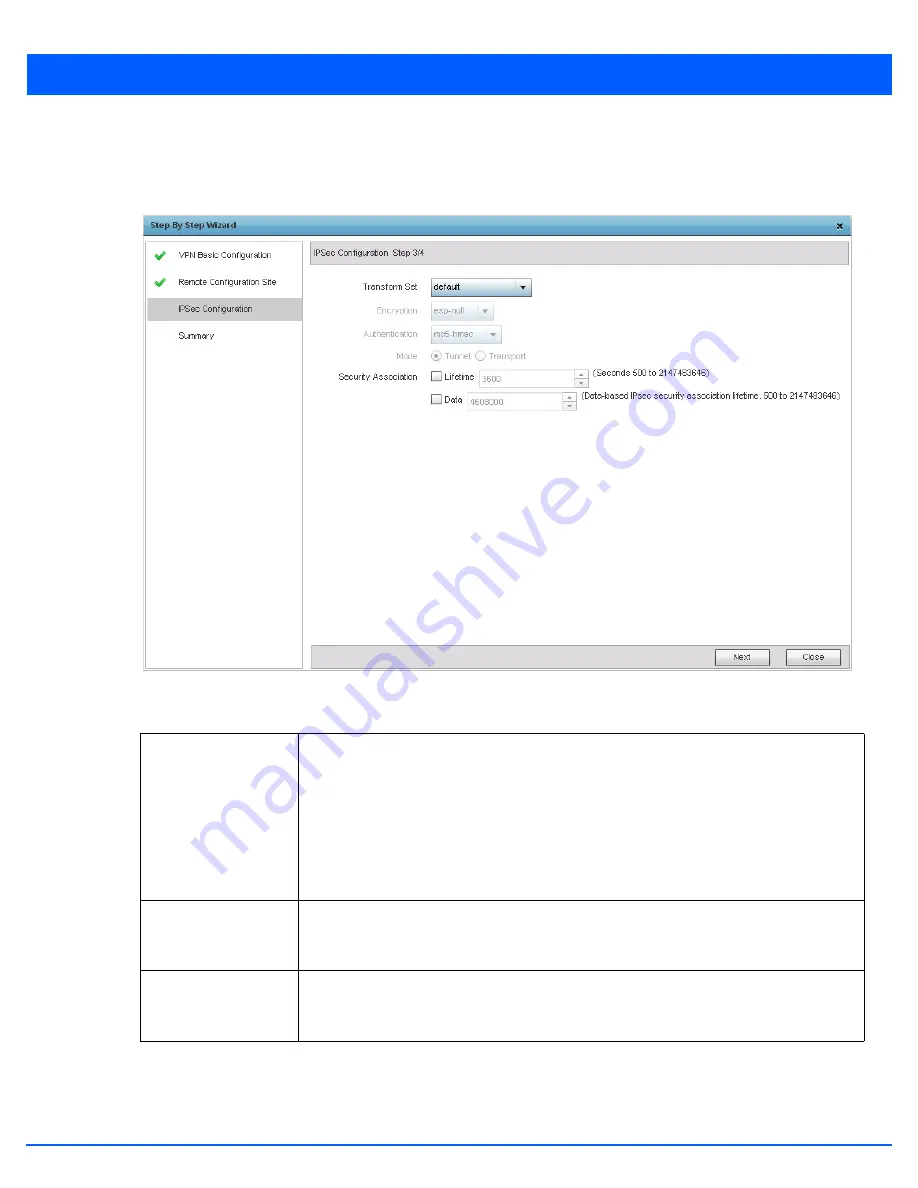
Figure 5-218
VPN Step-By-Step Wizard - Step 3
8. Configure the following IPSec parameters:
Transform Set
Transform set is a set of configurations exchanged for creating the VPN tunnel and impose a
security policy.The transform set is comprised of the following:
•
Encryption
– The encryption to use for creating the tunnel.
•
Authentication
– The authentication used to identify tunnel peers
•
Mode
– The mode of the tunnel. This is how the tunnel will operate.
From the drop-down, select any pre-configured Transform Set or click the
Create New Policy
to create a new transform set.
Encryption
This field is enabled when
Create New Policy
is selected in
Transform Set
field. This is the
encryption that is used on data traversing through the tunnel. Select from
esp-null
,
des, 3des,
aes, aes-192
and
aes-256
algorithms.
Authentication
This field is enabled when
Create New Policy
is selected in
Transform Set
field. This is the
method peers authenticate as the source of the packet to other peers after a VPN Tunnel has
been created. Select from
MD5
or
SHA.
Summary of Contents for WiNG 5.6
Page 1: ...Motorola Solutions WiNG 5 6 ACCESS POINT SYSTEM REFERENCE GUIDE ...
Page 2: ......
Page 22: ...8 WiNG 5 6 Access Point System Reference Guide ...
Page 26: ...1 4 WiNG 5 6 Access Point System Reference Guide ...
Page 38: ...2 12 WiNG 5 6 Access Point System Reference Guide ...
Page 74: ...3 36 WiNG 5 6 Access Point System Reference Guide ...
Page 468: ...6 2 WiNG 5 6 Access Point System Reference Guide Figure 6 1 Configuration Wireless menu ...
Page 568: ...6 102 WiNG 5 6 Access Point System Reference Guide ...
Page 614: ...7 46 WiNG 5 6 Access Point System Reference Guide ...
Page 660: ...8 46 WiNG 5 6 Access Point System Reference Guide ...
Page 716: ...9 56 WiNG 5 6 Access Point System Reference Guide ...
Page 730: ...10 14 WiNG 5 6 Access Point System Reference Guide ...
Page 982: ...14 20 WiNG 5 6 Access Point System Reference Guide ...
Page 984: ...A 2 WiNG 5 6 Access Point System Reference Guide ...
Page 1046: ...B 62 WiNG 5 6 Access Point System Reference Guide ...
Page 1047: ......
















































