ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
6-6
Monitoring System Access and Performance
v1.0, September 2009
3.
4.
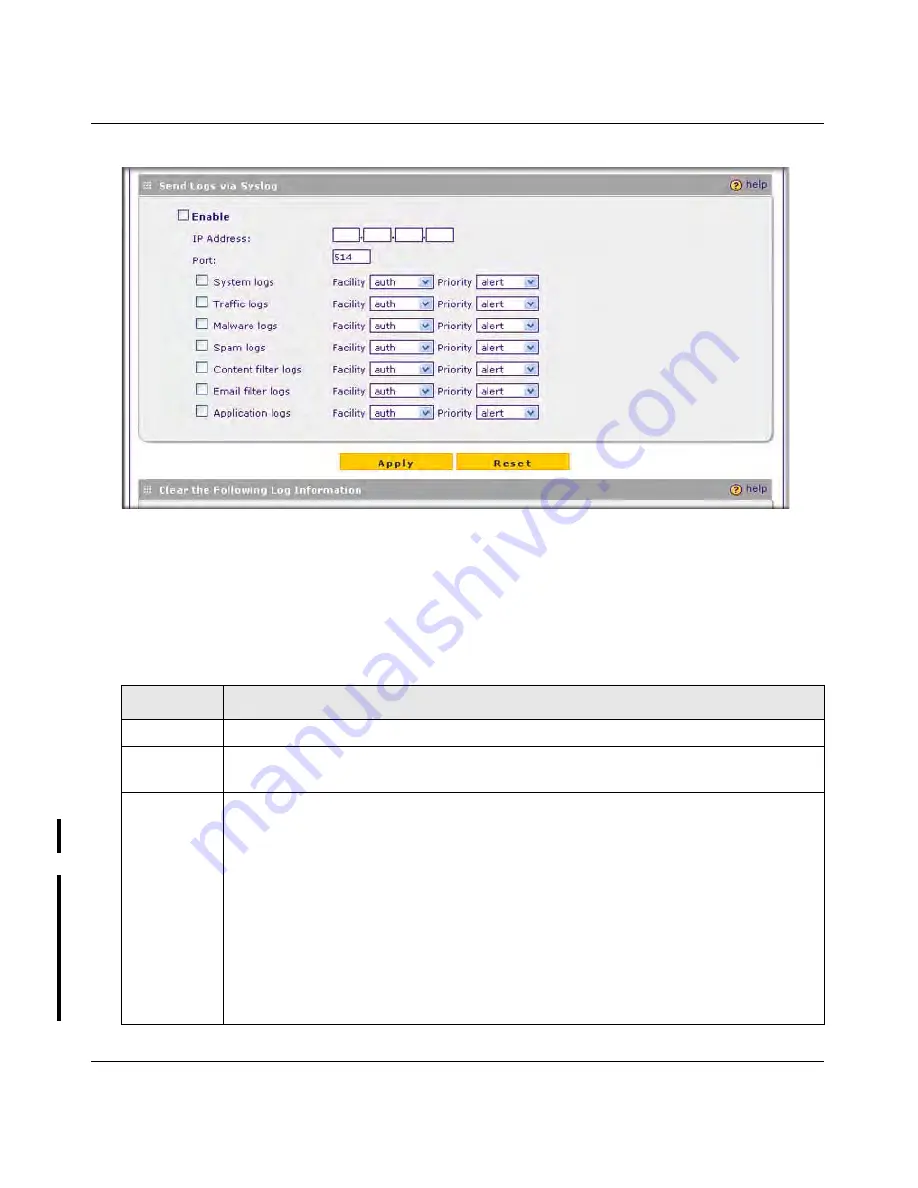
Select the
Enable
checkbox to enable the STM to send logs to a syslog server.
5.
Complete the fields, select the checkboxes, and make your selections from the pull-down
menus as explained in
Table 6-3
.
Figure 6-3
Table 6-3.
Syslog
Settings
Setting
Description (or Subfield and Description)
IP Address
The IP address of the syslog server.
Port
The port number that the syslog server uses to receive logs. The default port number is
514.
Logs
Select the checkboxes to specify which logs will be sent to the syslog server:
•
System logs
. he system event logs that include all system errors, informational
messages, configuration changes, and system software updates.
•
Traffic logs
. All scanned incoming and outgoing traffic.
•
Malware logs
. All intercepted viruses and spyware.
•
Spam logs
. All intercepted spam, including spam that was detected through the
blacklist, real-time blacklist, and Distributed Spam Analysis.
•
Content filter logs
. All Web sites, URLs, and FTP sites that are intercepted because
of Web category, blacklist, file type, or size limit violations.
•
Email filter logs
. All e-mails that are intercepted because of keyword, file type, file
name, password, or size limit violations.
•
Application logs
. All intercepted application access violations.
DRAFT




































