ProSecure Web/Email Security Threat Management (STM) Appliance Reference Manual
6-38
Monitoring System Access and Performance
v1.0, September 2009
•
Send as Ham
. The selected spam e-mail files are not tagged as spam for Distributed Spam
Analysis, are deleted from the quarantine file, and are sent to the intended recipients.
•
Delete
. The selected spam e-mail files are deleted from the quarantine file.
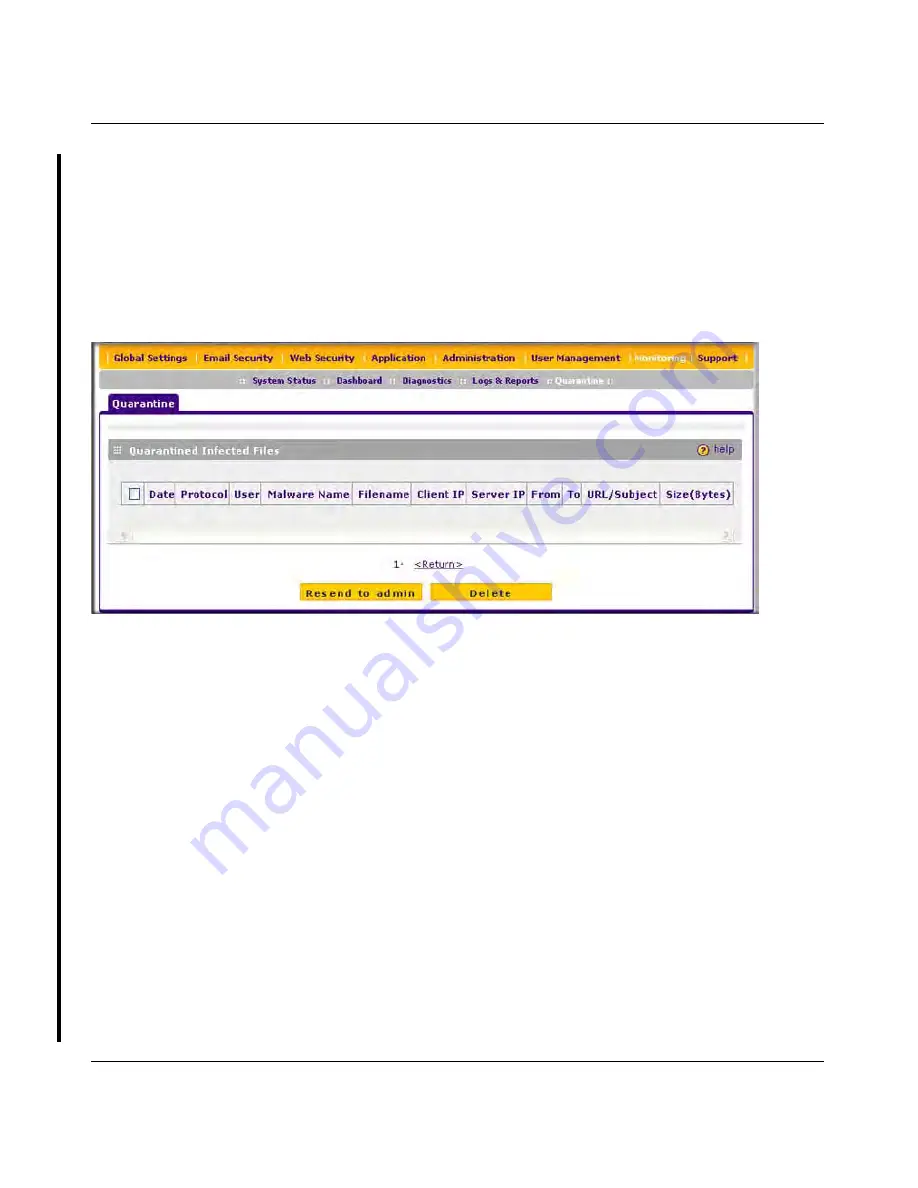
Viewing and Managing the Quarantined Infected Files Table
When you query the malware quarantine file, the Quarantine screen with the Quarantined Infected
Files table displays (see
Figure 6-17
).
The Quarantined Infected Files table shows the following columns:
•
Checkbox
. Lets you select the table entry.
•
Date
. The date that the file was received.
•
Protocol
. The protocol (SMTP, POP3, IMAP, HTTP, FTP, HTTPS) in which the spyware or
virus was found.
•
User
. The user name that was used to log on the STM.
•
Malware name
. The name of the spyware or virus.
•
File name
. The name of the file in which the spyware or virus was found.
•
Client IP
. The client IP address from which the spyware or virus originated.
•
Server IP
. The server IP address from which the spyware or virus originated.
•
From
. The e-mail address of the sender.
•
To
. The e-mail address of the recipient.
•
URL/Subject
. The URL or subject that is associated with the spyware or virus.
•
Size (Bytes)
. The size of the virus or spyware file in bytes.
Figure 6-17
DRAFT






































