Chapter 11 Firewall screens
173
Nortel Business Secure Router 252 Configuration — Basics
the LAN interface is an example of traffic destined for the Business Secure Router
LAN interface itself. You can also use LAN to LAN/Business Secure Router rules
with IP alias to control routing between two subnets on the LAN.
WAN to WAN/Business Secure Router rules apply to packets coming in through
the WAN interface that are destined for either the Business Secure Router WAN
interface itself or a different subnet on the WAN. A management session through
the WAN interface is an example of traffic destined for the Business Secure
Router WAN interface itself. By default, the Business Secure Router stops WAN
computers from using the Business Secure Router as a gateway to communicate
with other computers on the WAN. You can configure one of these rules to allow
a WAN computer to manage the Business Secure Router.
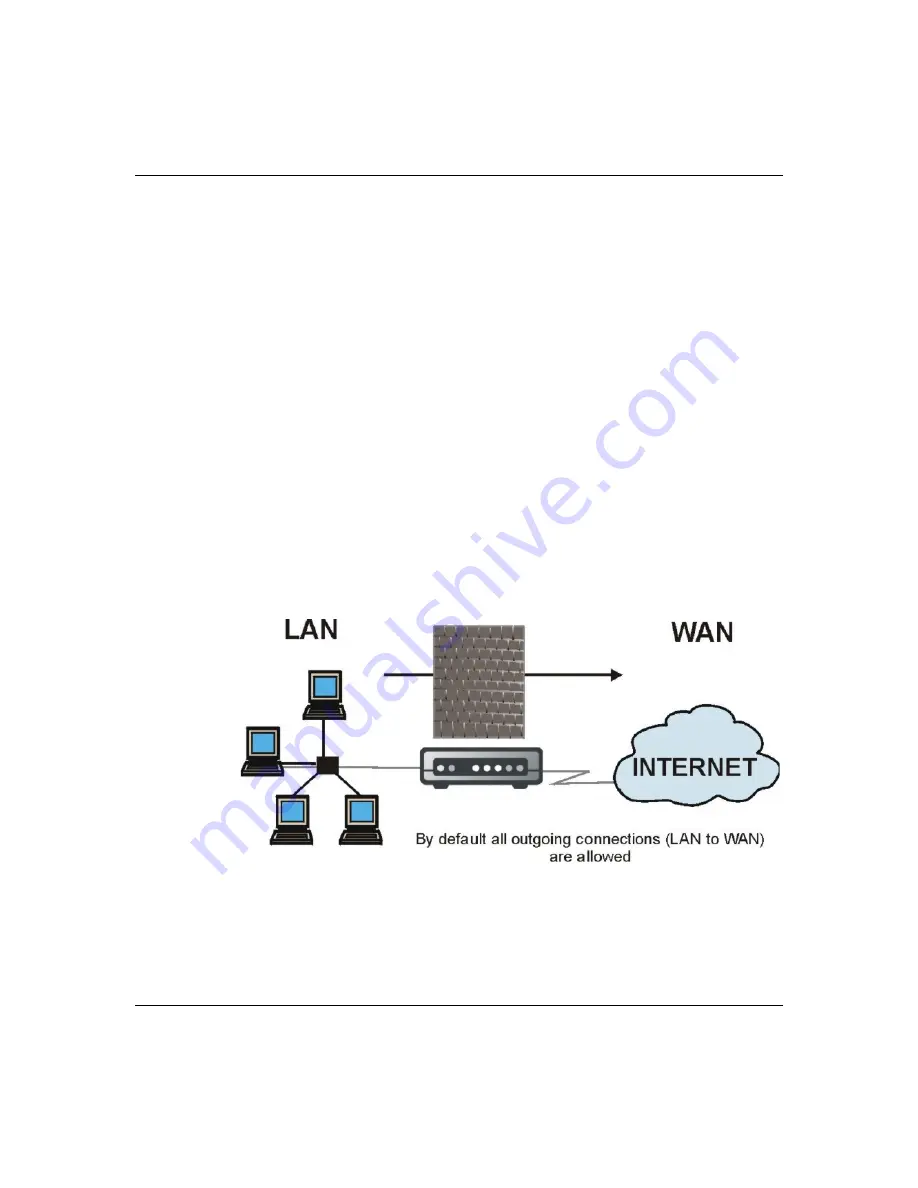
LAN to WAN rules
The default rule for LAN to WAN traffic is that all users on the LAN are allowed
unrestricted access to the WAN. When you configure a LAN to WAN rule, you in
essence want to limit some or all users from accessing certain services on the
WAN.
Figure 50
LAN to WAN traffic
WAN to LAN rules
The default rule for WAN to LAN traffic blocks all incoming connections (WAN
to LAN). If you want to allow certain WAN users to have access to your LAN,
you need to create custom rules to allow it.
Business Secure Router
Summary of Contents for BSR252
Page 28: ...28 Tables NN47923 500 ...
Page 44: ...44 Chapter 1 Getting to know your Business Secure Router NN47923 500 ...
Page 52: ...52 Chapter 2 Introducing the WebGUI NN47923 500 ...
Page 70: ...70 Chapter 3 Wizard setup NN47923 500 ...
Page 96: ...96 Chapter 5 System screens NN47923 500 ...
Page 114: ...114 Chapter 7 WAN screens NN47923 500 Figure 27 WAN IP ...
Page 120: ...120 Chapter 7 WAN screens NN47923 500 Figure 31 Dial Backup Setup ...
Page 128: ...128 Chapter 7 WAN screens NN47923 500 ...
Page 152: ...152 Chapter 9 Static Route screens NN47923 500 ...
Page 194: ...194 Chapter 11 Firewall screens NN47923 500 ...
Page 210: ...210 Chapter 13 VPN NN47923 500 Figure 67 Summary IP Policies ...
Page 222: ...222 Chapter 13 VPN NN47923 500 Figure 71 VPN Branch Office rule setup ...
Page 256: ...256 Chapter 13 VPN NN47923 500 Figure 81 VPN Client Termination advanced ...
Page 260: ...260 Chapter 13 VPN NN47923 500 ...
Page 264: ...264 Chapter 14 Certificates NN47923 500 Figure 83 My Certificates ...
Page 270: ...270 Chapter 14 Certificates NN47923 500 Figure 85 My Certificate create ...
Page 274: ...274 Chapter 14 Certificates NN47923 500 Figure 86 My Certificate details ...
Page 282: ...282 Chapter 14 Certificates NN47923 500 Figure 89 Trusted CA details ...
Page 298: ...298 Chapter 14 Certificates NN47923 500 ...
Page 316: ...316 Chapter 16 IEEE 802 1x NN47923 500 ...
Page 320: ...320 Chapter 17 Authentication server NN47923 500 Figure 106 Local User database edit ...
Page 328: ...328 Chapter 17 Authentication server NN47923 500 ...
Page 376: ...376 Chapter 20 Logs Screens NN47923 500 Figure 150 Log settings ...
Page 386: ...386 Chapter 20 Logs Screens NN47923 500 ...
Page 393: ...Chapter 21 Call scheduling screens 393 Nortel Business Secure Router 252 Configuration Basics ...
Page 394: ...394 Chapter 21 Call scheduling screens NN47923 500 ...
Page 410: ...410 Chapter 22 Maintenance NN47923 500 ...
















































