284
Chapter 14 Certificates
NN47923-500
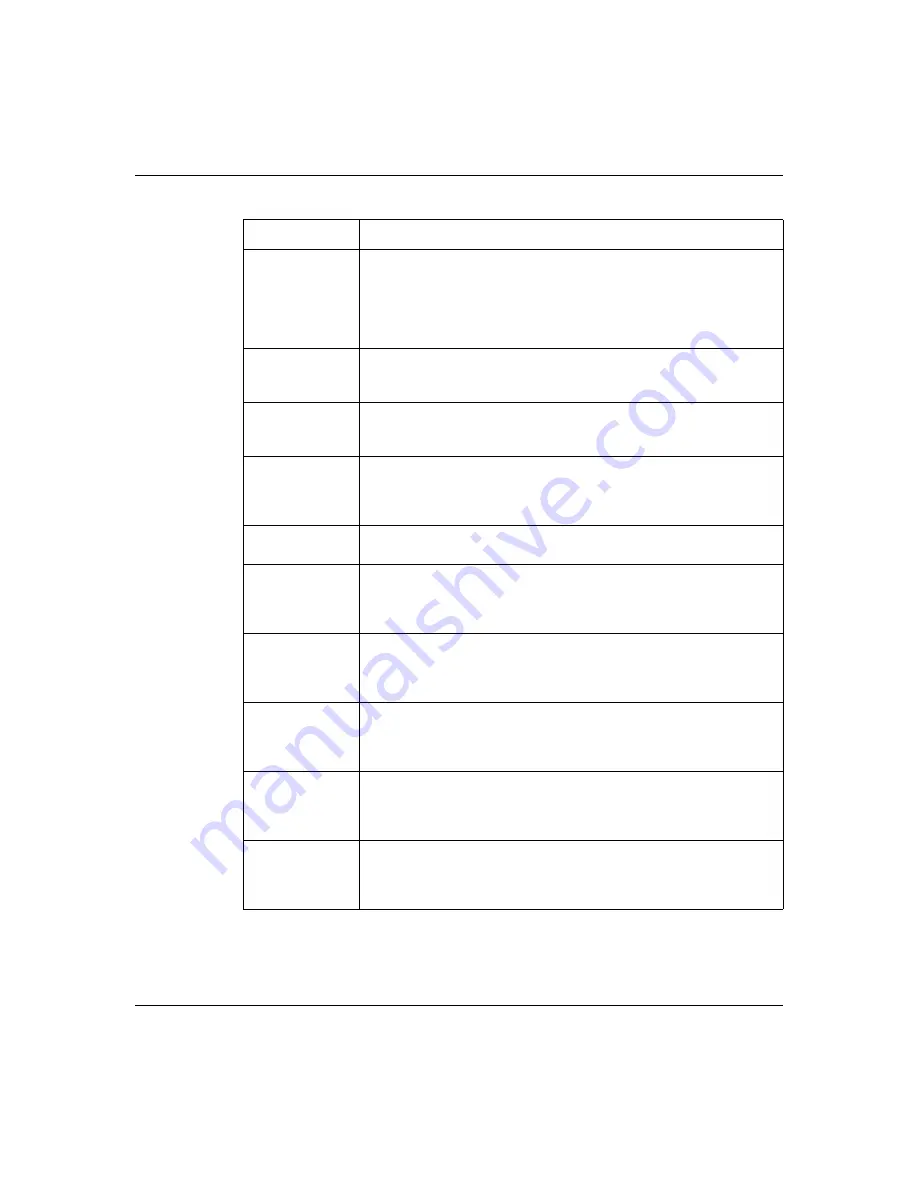
Signature
Algorithm
This field displays the type of algorithm that was used to sign the
certificate. Some certification authorities use rsa-pkcs1-sha1 (RSA
public-private key encryption algorithm and the SHA1 hash
algorithm). Other certification authorities can use rsa-pkcs1-md5
(RSA public-private key encryption algorithm and the MD5 hash
algorithm).
Valid From
This field displays the date that the certificate becomes applicable.
The text displays in red and includes a Not Yet Valid! message if the
certificate has not yet become applicable.
Valid To
This field displays the date that the certificate expires. The text
displays in red and includes an Expiring! or Expired! message if the
certificate is about to expire or has already expired.
Key Algorithm
This field displays the type of algorithm that was used to generate the
certificate key pair (the Business Secure Router uses RSA
encryption) and the length of the key set in bits (1 024-bits, for
example).
Subject
Alternative Name
This (optional) field displays the IP address (IP), domain name (DNS),
or e-mail address (EMAIL) of the owner of the certificate.
Key Usage
This field displays for what functions the certificate key can be used.
For example, “DigitalSignature” means that the key can be used to
sign certificates and “KeyEncipherment” means that the key can be
used to encrypt text.
Basic Constraint
This field displays general information about the certificate. For
example, Subject Type=CA means that this is a certification authority
certificate and “Path Length Constraint=1” means that there can only
be one certification authority in the certification path.
CRL Distribution
Points
This field displays how many directory servers with Lists of revoked
certificates the issuing certification authority of this certificate makes
available. This field also displays the domain names or IP addresses
of the servers.
MD5 Fingerprint
This is the message digest of the certificate that the Business Secure
Router calculated using the MD5 algorithm. You can use this value to
verify with the certification authority (over the phone, for example) that
this is actually a valid certificate.
SHA1 Fingerprint This is the message digest of the certificate that the Business Secure
Router calculated using the SHA1 algorithm. You can use this value
to verify with the certification authority (over the phone, for example)
that this is actually a valid certificate.
Table 70
Trusted CA details
Label
Description
Summary of Contents for BSR252
Page 28: ...28 Tables NN47923 500 ...
Page 44: ...44 Chapter 1 Getting to know your Business Secure Router NN47923 500 ...
Page 52: ...52 Chapter 2 Introducing the WebGUI NN47923 500 ...
Page 70: ...70 Chapter 3 Wizard setup NN47923 500 ...
Page 96: ...96 Chapter 5 System screens NN47923 500 ...
Page 114: ...114 Chapter 7 WAN screens NN47923 500 Figure 27 WAN IP ...
Page 120: ...120 Chapter 7 WAN screens NN47923 500 Figure 31 Dial Backup Setup ...
Page 128: ...128 Chapter 7 WAN screens NN47923 500 ...
Page 152: ...152 Chapter 9 Static Route screens NN47923 500 ...
Page 194: ...194 Chapter 11 Firewall screens NN47923 500 ...
Page 210: ...210 Chapter 13 VPN NN47923 500 Figure 67 Summary IP Policies ...
Page 222: ...222 Chapter 13 VPN NN47923 500 Figure 71 VPN Branch Office rule setup ...
Page 256: ...256 Chapter 13 VPN NN47923 500 Figure 81 VPN Client Termination advanced ...
Page 260: ...260 Chapter 13 VPN NN47923 500 ...
Page 264: ...264 Chapter 14 Certificates NN47923 500 Figure 83 My Certificates ...
Page 270: ...270 Chapter 14 Certificates NN47923 500 Figure 85 My Certificate create ...
Page 274: ...274 Chapter 14 Certificates NN47923 500 Figure 86 My Certificate details ...
Page 282: ...282 Chapter 14 Certificates NN47923 500 Figure 89 Trusted CA details ...
Page 298: ...298 Chapter 14 Certificates NN47923 500 ...
Page 316: ...316 Chapter 16 IEEE 802 1x NN47923 500 ...
Page 320: ...320 Chapter 17 Authentication server NN47923 500 Figure 106 Local User database edit ...
Page 328: ...328 Chapter 17 Authentication server NN47923 500 ...
Page 376: ...376 Chapter 20 Logs Screens NN47923 500 Figure 150 Log settings ...
Page 386: ...386 Chapter 20 Logs Screens NN47923 500 ...
Page 393: ...Chapter 21 Call scheduling screens 393 Nortel Business Secure Router 252 Configuration Basics ...
Page 394: ...394 Chapter 21 Call scheduling screens NN47923 500 ...
Page 410: ...410 Chapter 22 Maintenance NN47923 500 ...
















































