434
Appendix B Log Descriptions
NN47923-500
For type and code details, see
teardrop ICMP
(type:%d, code:%d)
The firewall detected an ICMP teardrop attack.
illegal command TCP
The firewall detected a TCP illegal command attack.
NetBIOS TCP
The firewall detected a TCP NetBIOS attack.
ip spoofing - no
routing entry TCP
The firewall detected a TCP IP spoofing attack while the
Business Secure Router did not have a default route.
ip spoofing - no
routing entry UDP
The firewall detected an UDP IP spoofing attack while the
Business Secure Router did not have a default route.
ip spoofing - no
routing entry IGMP
The firewall detected an IGMP IP spoofing attack while the
Business Secure Router did not have a default route.
ip spoofing - no
routing entry ESP
The firewall detected an ESP IP spoofing attack while the
Business Secure Router did not have a default route.
ip spoofing - no
routing entry GRE
The firewall detected a GRE IP spoofing attack while the
Business Secure Router did not have a default route.
ip spoofing - no
routing entry OSPF
The firewall detected an OSPF IP spoofing attack while the
Business Secure Router did not have a default route.
ip spoofing - no
routing entry ICMP
(type:%d, code:%d)
The firewall detected an ICMP IP spoofing attack while the
Business Secure Router did not have a default route.
vulnerability ICMP
(type:%d, code:%d)
The firewall detected an ICMP vulnerability attack.
traceroute ICMP
(type:%d, code:%d)
The firewall detected an ICMP traceroute attack.
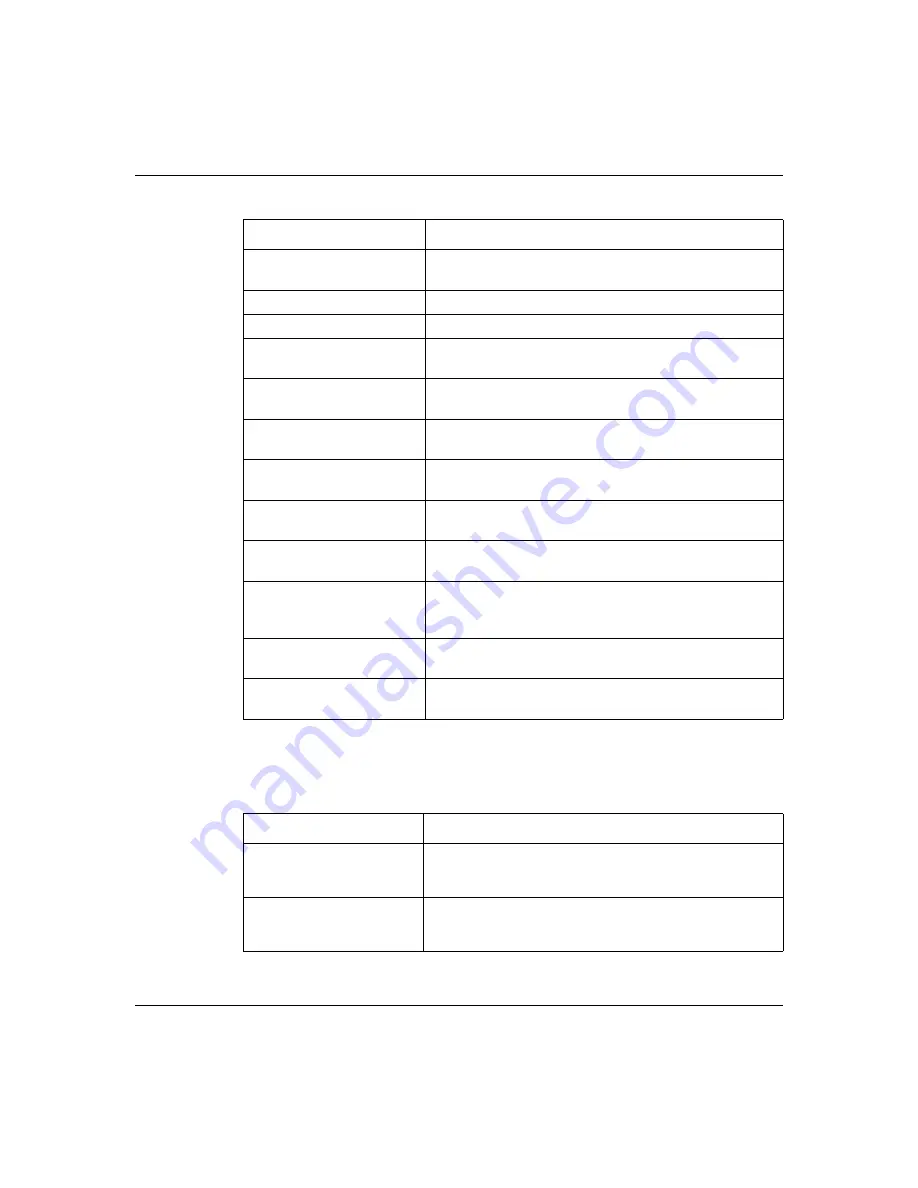
Table 128
Access Logs
Log Message
Description
Firewall default
policy: TCP (set:%d)
TCP access matched the default policy of the listed ACL
set and the Business Secure Router blocked or forwarded
it according to the configuration of the ACL set.
Firewall default
policy: UDP (set:%d)
UDP access matched the default policy of the listed ACL
set and the Business Secure Router blocked or forwarded
it according to the configuration of the ACL set.
Table 127
Attack Logs
Log Message
Description
Summary of Contents for BSR252
Page 28: ...28 Tables NN47923 500 ...
Page 44: ...44 Chapter 1 Getting to know your Business Secure Router NN47923 500 ...
Page 52: ...52 Chapter 2 Introducing the WebGUI NN47923 500 ...
Page 70: ...70 Chapter 3 Wizard setup NN47923 500 ...
Page 96: ...96 Chapter 5 System screens NN47923 500 ...
Page 114: ...114 Chapter 7 WAN screens NN47923 500 Figure 27 WAN IP ...
Page 120: ...120 Chapter 7 WAN screens NN47923 500 Figure 31 Dial Backup Setup ...
Page 128: ...128 Chapter 7 WAN screens NN47923 500 ...
Page 152: ...152 Chapter 9 Static Route screens NN47923 500 ...
Page 194: ...194 Chapter 11 Firewall screens NN47923 500 ...
Page 210: ...210 Chapter 13 VPN NN47923 500 Figure 67 Summary IP Policies ...
Page 222: ...222 Chapter 13 VPN NN47923 500 Figure 71 VPN Branch Office rule setup ...
Page 256: ...256 Chapter 13 VPN NN47923 500 Figure 81 VPN Client Termination advanced ...
Page 260: ...260 Chapter 13 VPN NN47923 500 ...
Page 264: ...264 Chapter 14 Certificates NN47923 500 Figure 83 My Certificates ...
Page 270: ...270 Chapter 14 Certificates NN47923 500 Figure 85 My Certificate create ...
Page 274: ...274 Chapter 14 Certificates NN47923 500 Figure 86 My Certificate details ...
Page 282: ...282 Chapter 14 Certificates NN47923 500 Figure 89 Trusted CA details ...
Page 298: ...298 Chapter 14 Certificates NN47923 500 ...
Page 316: ...316 Chapter 16 IEEE 802 1x NN47923 500 ...
Page 320: ...320 Chapter 17 Authentication server NN47923 500 Figure 106 Local User database edit ...
Page 328: ...328 Chapter 17 Authentication server NN47923 500 ...
Page 376: ...376 Chapter 20 Logs Screens NN47923 500 Figure 150 Log settings ...
Page 386: ...386 Chapter 20 Logs Screens NN47923 500 ...
Page 393: ...Chapter 21 Call scheduling screens 393 Nortel Business Secure Router 252 Configuration Basics ...
Page 394: ...394 Chapter 21 Call scheduling screens NN47923 500 ...
Page 410: ...410 Chapter 22 Maintenance NN47923 500 ...
















































