4
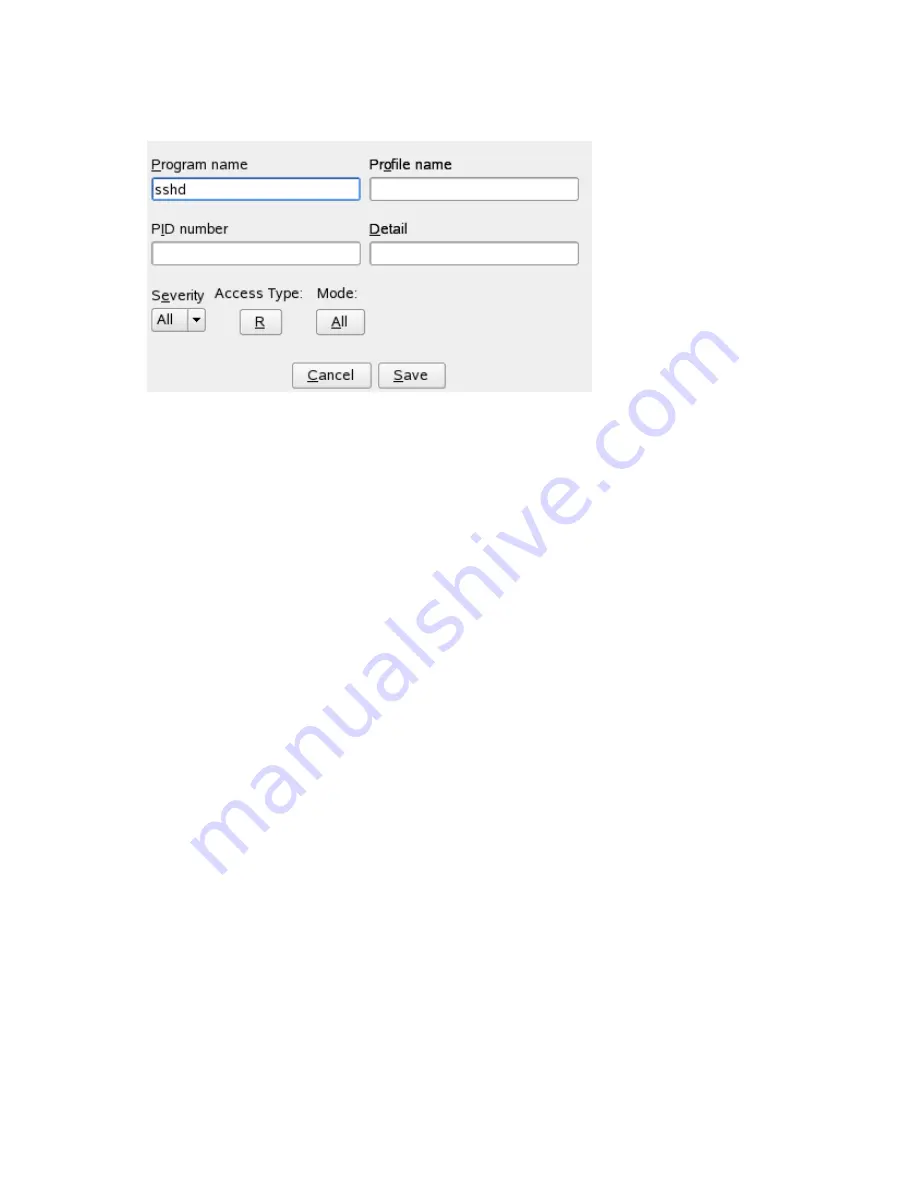
Fill in the fields with the following filtering information, as necessary:
Program Name
You can specify a program name or pattern that matches the name of the
binary executable for the program of interest. The report displays security
events that have occurred for the specified program only.
Profile Name
You can specify the name of the profile for which the report should display
security events. You can use this to see what is being confined by a specific
profile.
PID Number
A number that uniquely identifies one specific process or running program
(this number is valid only during the lifetime of that process).
Detail
A source to which the profile has denied access. This includes capabilities
and files. You can use this field to create a report of resources to which
profiles prevent access.
Severity
Select the lowest severity level of security events to include in the report.
The selected severity level and above are included in the reports.
Managing Profiled Applications
107
















































