Configuring with Web Based Management
5.5 "System" menu
SCALANCE W760/W720 to IEEE 802.11n Web Based Management
126
Configuration Manual, 11/2014, C79000-G8976-C350-03
Description
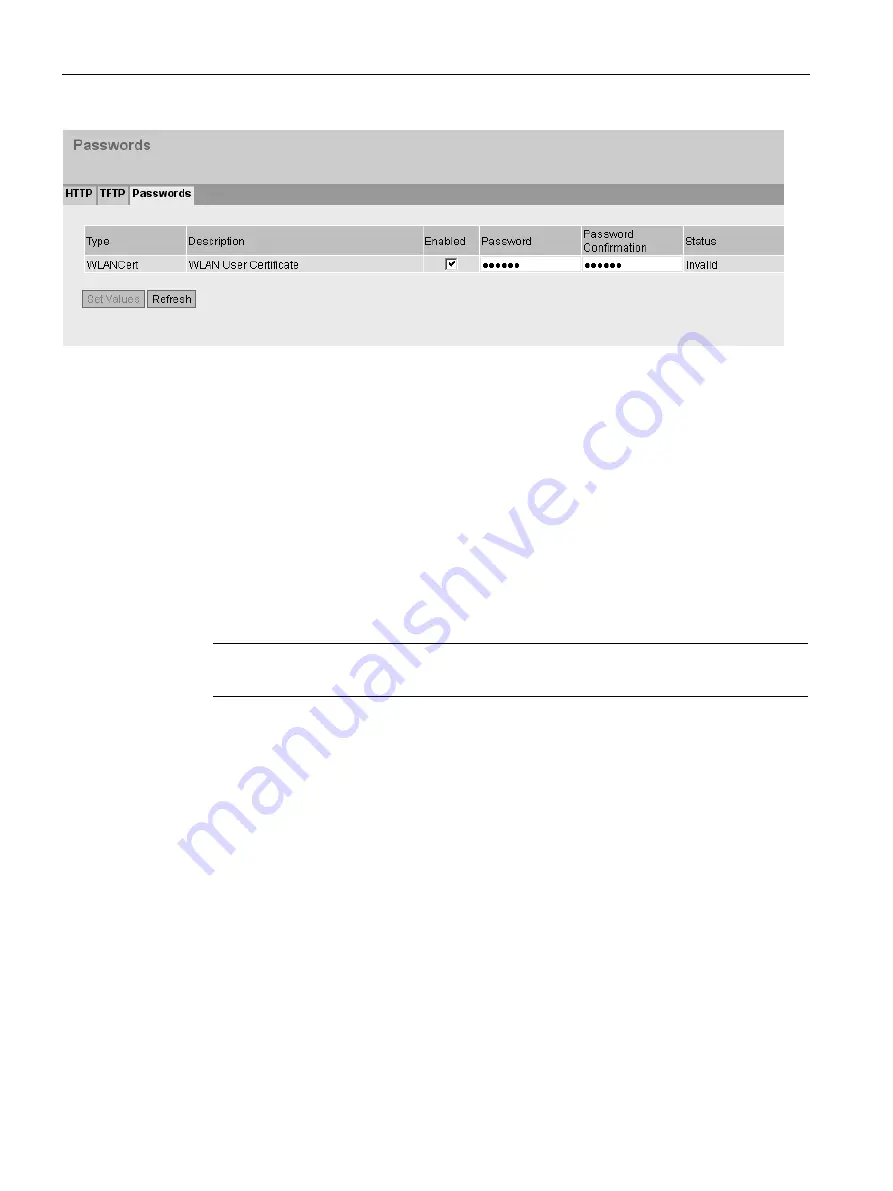
The table has the following columns:
●
Type
Shows the user certificate
●
Description
Shows the short description of the user certificate.
●
Enabled
Specifies whether the user certificate needs a password. If you enable the settings,
specify the password in "Password".
●
Password
Enter the password for the user certificate.
Note
When assigning the password, ASCII code 0x20 to 0x7e is used.
●
Password Confirmation
Confirm the password.
●
Status
Shows whether the current settings for the certificate match the device.
–
Valid
The settings are valid.
–
Invalid
The settings are invalid.
Procedure
1.
Select the "Enabled" option.
2.
Enter the password in "Password".
3.
To confirm the password, enter the password again in "Password Confirmation".
4.
Click the "Set Values" button.
















































