-66-
Figure 3-45 RIP
The following items are displayed on this screen:
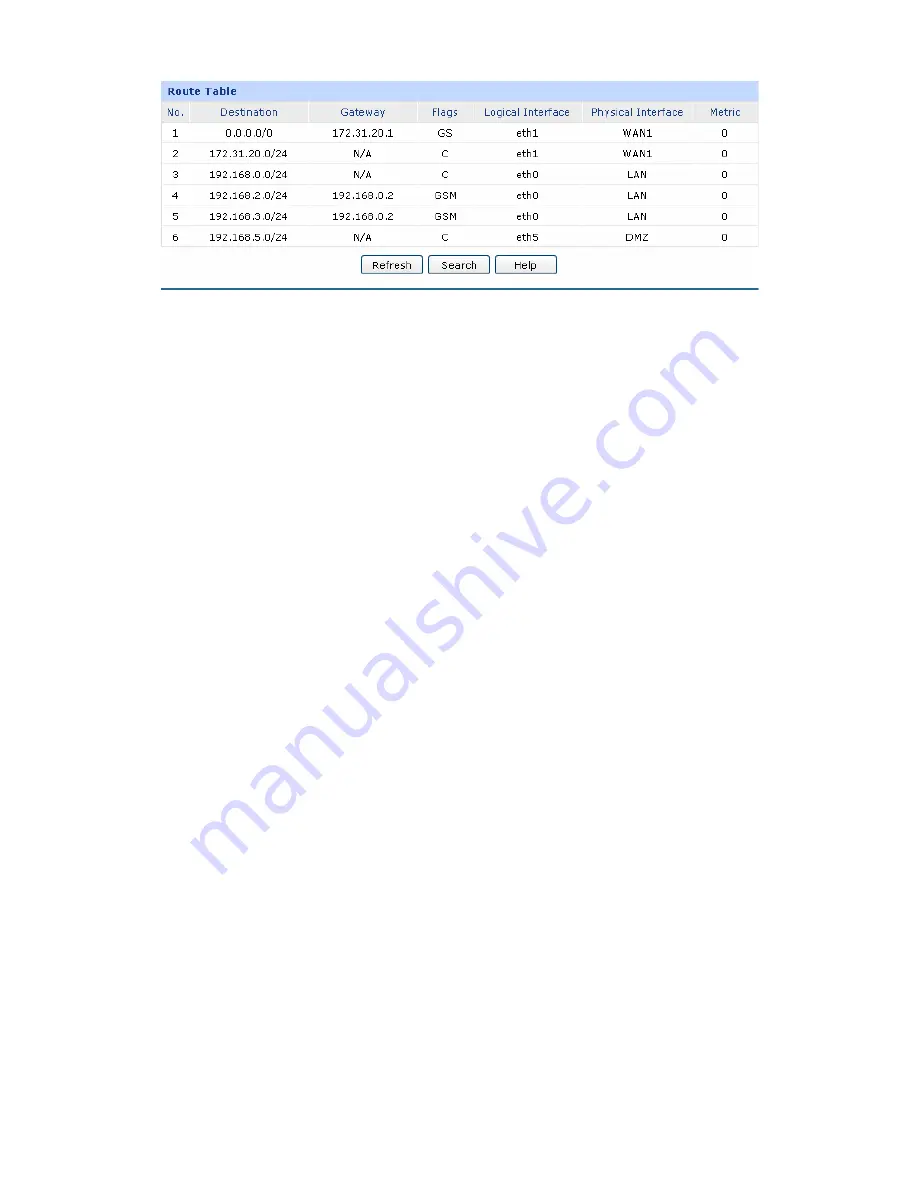
Route Table
Destination:
The Destination of route entry.
Gateway:
The Gateway of route entry.
Flags:
The Flags of route entry. The Flags describe certain characteristics of
the route.
Logical Interface:
The logical interface of route entry.
Physical Interface:
The
y.
The Metric of route entry.
3.4
3.4
ARP
corresponding MAC addresses so that packets can be delivered to their destinations correctly.
ARP
ddress and maintain an ARP
Table in which the latest used IP address-to-MAC address mapping entries are stored. ARP protocol
etwork segment to communicate with one another or access to
external network via Gateway. However, since ARP protocol is implemented with the premise that all
the H
eways are
sks during ARP Implementation
Procedure in the actual complex network.
The attacker may send the ARP spoofing packets with false IP address-to-MAC address mapping
entries, and then the device will automatically update the ARP table after receiving wrong ARP
physical interface of route entr
Metric
Firewall
.1 Anti ARP Spoofing
(Address Resolution Protocol) is used for analyzing and mapping IP addresses to the
functions to translate the IP address into the corresponding MAC a
can facilitate the Hosts in the same n
osts and Gat
trusted, there are high security ri
















































