Xerox D110/D125 Copier/Printer
セキュリティターゲット
- 116 –
Copyright
2012 by Fuji Xerox Co., Ltd
い、すべての
TOE
利用者に対して、いつ、誰が、どのような作業を行ったかという事象や重要なイベント
(
例え
ば障害や構成変更、ユーザー操作など
)
を、追跡記録するためのセキュリティ監査ログ機能を提供する。
(1)
FAU_GEN.1 Audit data generation(
監査データ生成
)
監査データの生成は、定義された監査対象イベントが、監査ログに記録されることを保証する。
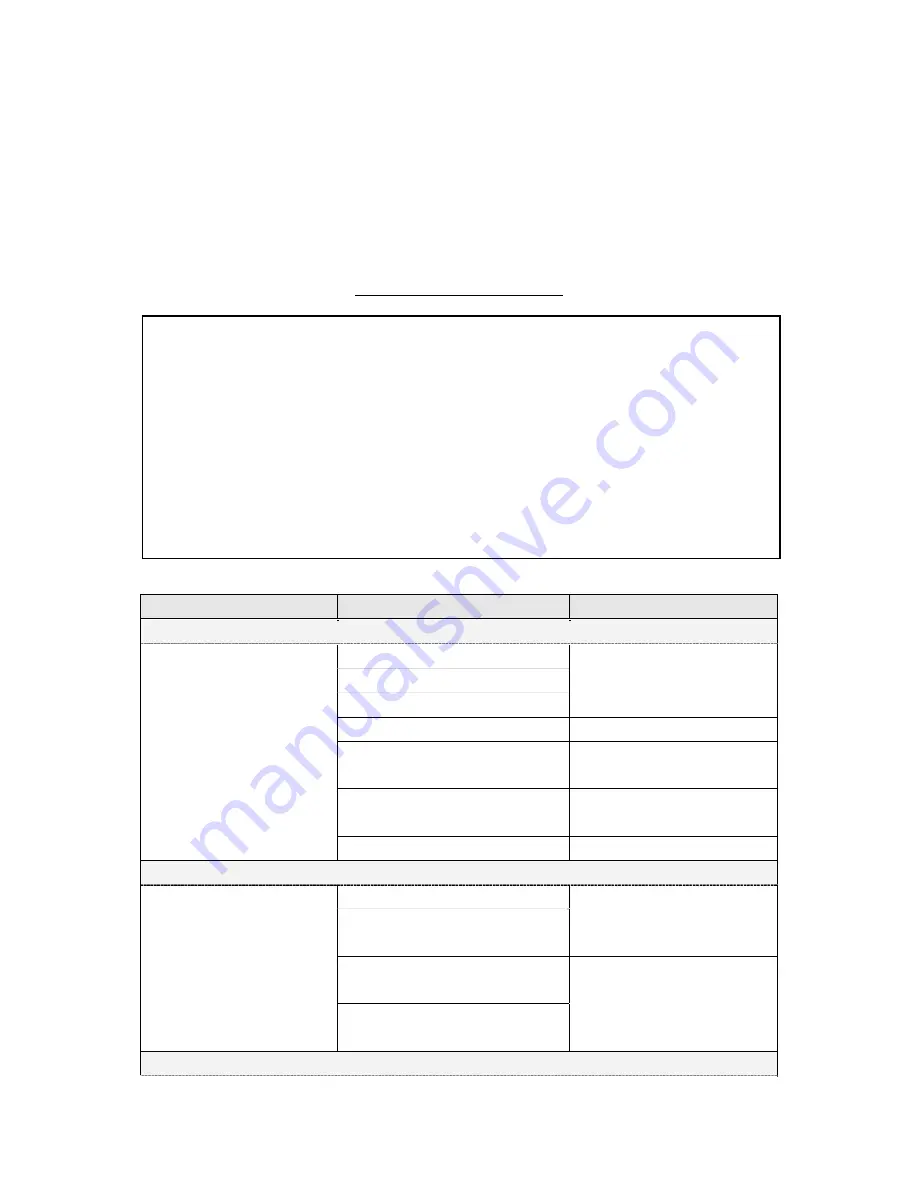
Table 45
に監査ログデータの詳細を示す
Table 45
監査ログのデータ詳細
Logged Events
Description
Status
デバイスの状態変化
System Status
Started normally(cold boot)
-
Started normally(warm boot)
Shutdown requested
User operation(Local)
Start/End
Scheduled Image
Overwriting started
Successful/Failed
Scheduled Image
Overwriting finished
Successful/Failed
Self Test
Successful/Failed
ユーザー認証
Login/Logout
Login Successful,
Failed(Invalid
UserID), Failed(Invalid
Password), Failed
Logout
Locked System Administrator
Authentication
-
(
失敗回数も保存
)
Detected continuous
Authentication Fail
監査ポリシー変更
監査ログ対象イベントは、以下の固定長データと共に記録される。:
Log ID
:監査ログ識別子としての通し番号(
1
~
60000
)
Date
:日付データ(
yyyy/mm/dd, mm/dd/yyyy, dd/mm/yyyy
のいずれか)
Time
:時刻データ(
hh:mm:ss
)
Logged Events
:イベント名称(最大
32
桁の任意文字列)
User Name
:利用者名(最大
32
桁の任意文字列)
Description
:イベントに関する内容の説明(最大
32
桁の任意文字列で詳細は下記参照のこと)
Status
:イベントの処理結果もしくは状態(最大
32
桁の任意文字列で詳細は下記参照のこと)
Optionally Logged Items
:共通保存項目以外に監査ログへ保存される追加情報(サブジェクト識別情
報等)











































