Appendix D Wireless LANs
AMG1302/AMG1202-TSeries User’s Guide
289
If this feature is enabled, it is not necessary to configure a default encryption key in the wireless
security configuration screen. You may still configure and store keys, but they will not be used while
dynamic WEP is enabled.
Note: EAP-MD5 cannot be used with Dynamic WEP Key Exchange
For added security, certificate-based authentications (EAP-TLS, EAP-TTLS and PEAP) use dynamic
keys for data encryption. They are often deployed in corporate environments, but for public
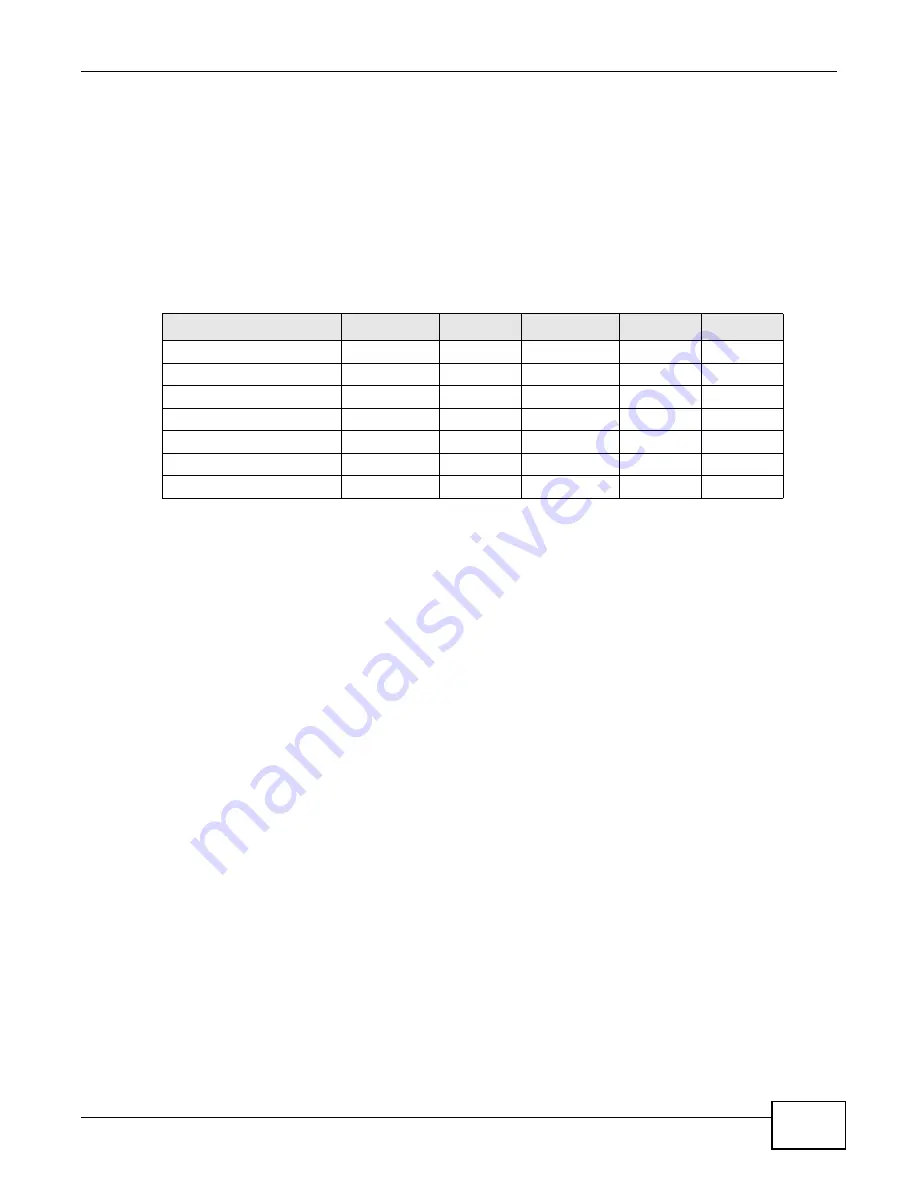
deployment, a simple user name and password pair is more practical. The following table is a
comparison of the features of authentication types.
WPA and WPA2
Wi-Fi Protected Access (WPA) is a subset of the IEEE 802.11i standard. WPA2 (IEEE 802.11i) is a
wireless security standard that defines stronger encryption, authentication and key management
than WPA.
Key differences between WPA or WPA2 and WEP are improved data encryption and user
authentication.
If both an AP and the wireless clients support WPA2 and you have an external RADIUS server, use
WPA2 for stronger data encryption. If you don't have an external RADIUS server, you should use
WPA2-PSK (WPA2-Pre-Shared Key) that only requires a single (identical) password entered into
each access point, wireless gateway and wireless client. As long as the passwords match, a wireless
client will be granted access to a WLAN.
If the AP or the wireless clients do not support WPA2, just use WPA or WPA-PSK depending on
whether you have an external RADIUS server or not.
Select WEP only when the AP and/or wireless clients do not support WPA or WPA2. WEP is less
secure than WPA or WPA2.
Encryption
WPA improves data encryption by using Temporal Key Integrity Protocol (TKIP), Message Integrity
Check (MIC) and IEEE 802.1x. WPA2 also uses TKIP when required for compatibility reasons, but
offers stronger encryption than TKIP with Advanced Encryption Standard (AES) in the Counter
mode with Cipher block chaining Message authentication code Protocol (CCMP).
TKIP uses 128-bit keys that are dynamically generated and distributed by the authentication server.
AES (Advanced Encryption Standard) is a block cipher that uses a 256-bit mathematical algorithm
Table 107
Comparison of EAP Authentication Types
EAP-MD5
EAP-TLS
EAP-TTLS
PEAP
LEAP
Mutual Authentication
No
Yes
Yes
Yes
Yes
Certificate – Client
No
Yes
Optional
Optional
No
Certificate – Server
No
Yes
Yes
Yes
No
Dynamic Key Exchange
No
Yes
Yes
Yes
Yes
Credential Integrity
None
Strong
Strong
Strong
Moderate
Deployment Difficulty
Easy
Hard
Moderate
Moderate
Moderate
Client Identity Protection
No
No
Yes
Yes
No
Summary of Contents for AMG1202-T series
Page 4: ...Contents Overview AMG1302 AMG1202 TSeries User s Guide 4 ...
Page 13: ...13 PART I User s Guide ...
Page 14: ...14 ...
Page 20: ...Chapter 1 Introduction AMG1302 AMG1202 TSeries User s Guide 20 ...
Page 28: ...Chapter 2 Introducing the Web Configurator AMG1302 AMG1202 TSeries User s Guide 28 ...
Page 61: ...Chapter 4 Tutorials AMG1302 AMG1202 TSeries User s Guide 61 Tutorial Advanced QoS Class Setup ...
Page 64: ...Chapter 4 Tutorials AMG1302 AMG1202 TSeries User s Guide 64 ...
Page 65: ...65 PART II Technical Reference ...
Page 66: ...66 ...
Page 72: ...Chapter 5 Connection Status and System Info Screens AMG1302 AMG1202 TSeries User s Guide 72 ...
Page 120: ...Chapter 7 Wireless LAN AMG1302 AMG1202 TSeries User s Guide 120 ...
Page 150: ...Chapter 10 Quality of Service QoS AMG1302 AMG1202 TSeries User s Guide 150 ...
Page 160: ...Chapter 11 Network Address Translation NAT AMG1302 AMG1202 TSeries User s Guide 160 ...
Page 172: ...Chapter 14 Filters AMG1302 AMG1202 TSeries User s Guide 172 ...
Page 194: ...Chapter 16 Parental Control AMG1302 AMG1202 TSeries User s Guide 194 ...
Page 200: ...Chapter 17 Certificate AMG1302 AMG1202 TSeries User s Guide 200 ...
Page 206: ...Chapter 19 Traffic Status AMG1302 AMG1202 TSeries User s Guide 206 ...
Page 208: ...Chapter 20 User Account AMG1302 AMG1202 TSeries User s Guide 208 ...
Page 212: ...Chapter 21 TR 069 Client AMG1302 AMG1202 TSeries User s Guide 212 ...
Page 216: ...Chapter 22 System Settings AMG1302 AMG1202 TSeries User s Guide 216 ...
Page 222: ...Chapter 24 Backup Restore AMG1302 AMG1202 TSeries User s Guide 222 ...
Page 234: ...Chapter 25 Remote Management AMG1302 AMG1202 TSeries User s Guide 234 ...
Page 238: ...Chapter 26 Diagnostic AMG1302 AMG1202 TSeries User s Guide 238 ...
Page 244: ...Chapter 27 Troubleshooting AMG1302 AMG1202 TSeries User s Guide 244 ...
Page 294: ...Appendix D Wireless LANs AMG1302 AMG1202 TSeries User s Guide 294 ...
Page 304: ...Appendix E IPv6 AMG1302 AMG1202 TSeries User s Guide 304 ...
Page 320: ...Index AMG1302 AMG1202 TSeries User s Guide 320 ...
















































