Chapter 7 Wireless
EX5501-B0 / AX7501-B0 / PX7501-B0 User’s Guide
119
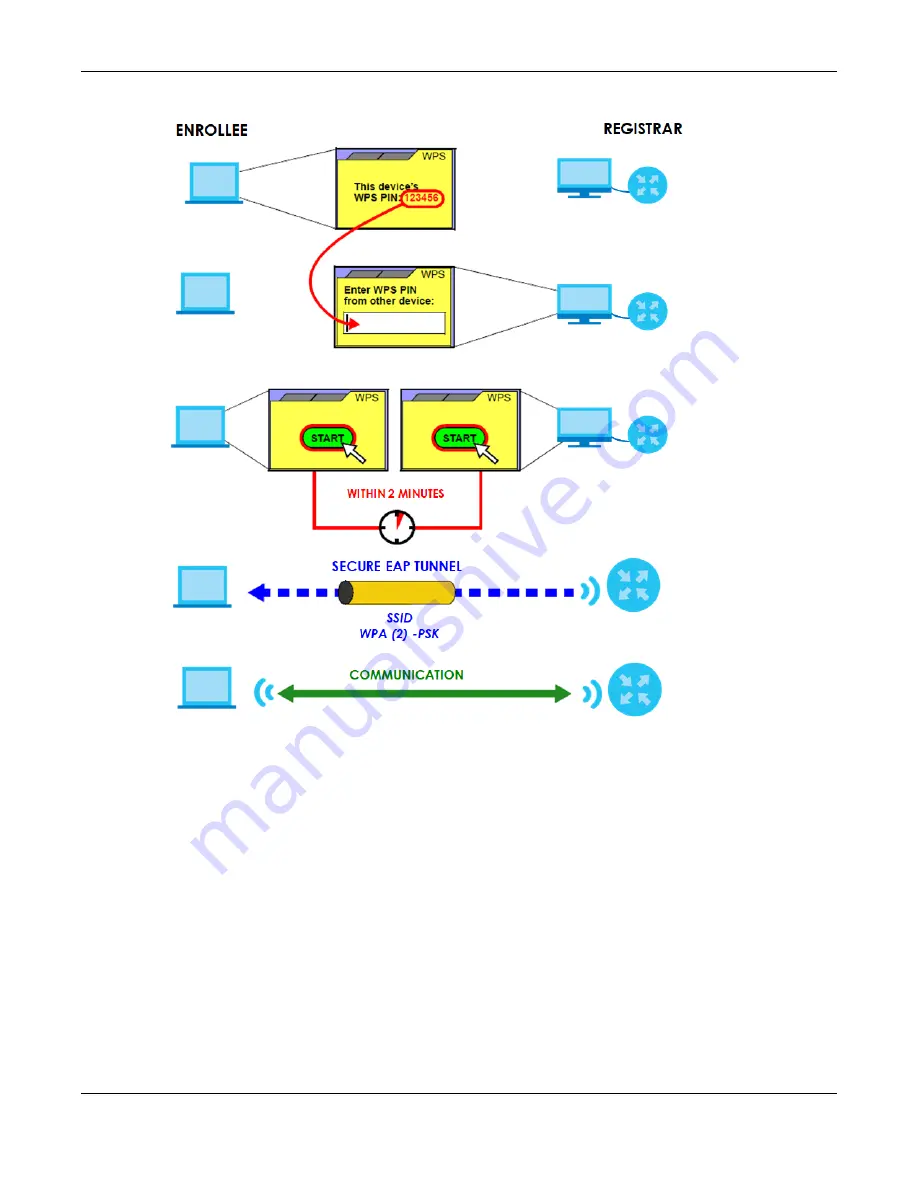
Figure 67
Example WPS Process: PIN Method
7.9.8.3 How WPS Works
When two WPS-enabled devices connect, each device must assume a specific role. One device acts
as the registrar (the device that supplies network and security settings) and the other device acts as the
enrollee (the device that receives network and security settings. The registrar creates a secure EAP
(Extensible Authentication Protocol) tunnel and sends the network name (SSID) and the WPA-PSK or
WPA2-PSK pre-shared key to the enrollee. Whether WPA-PSK or WPA2-PSK is used depends on the
standards supported by the devices. If the registrar is already part of a network, it sends the existing
information. If not, it generates the SSID and WPA2-PSK randomly.
The following figure shows a WPS-enabled client (installed in a notebook computer) connecting to a
WPS-enabled access point.
















































