Chapter 11 IPSec VPN
P-793H User’s Guide
175
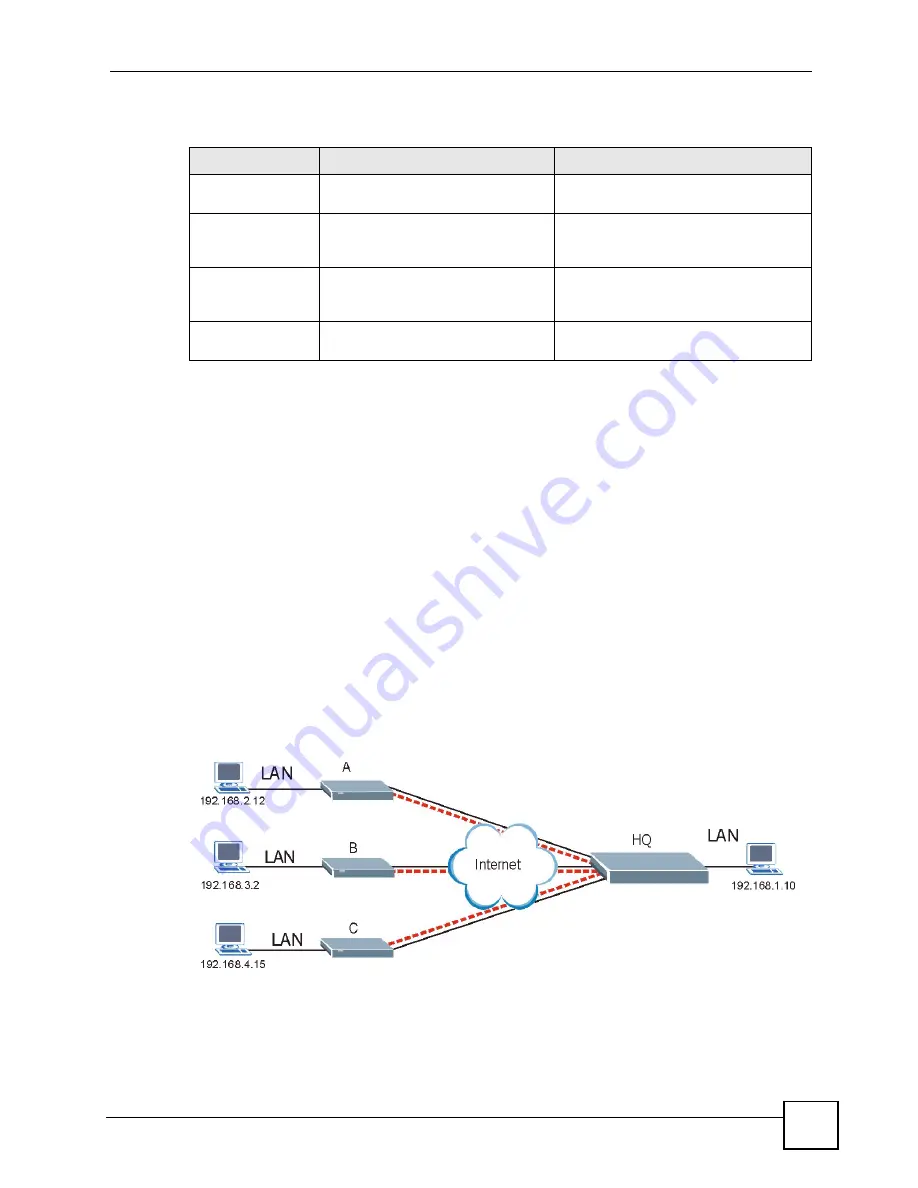
11.8.2 Telecommuters Using Unique VPN Rules Example
In this example the telecommuters (A, B and C in the figure) use IPSec routers with domain
names that are mapped to their dynamic WAN IP addresses (use Dynamic DNS to do this).
With aggressive negotiation mode (see
), the ZyXEL Device can
use the ID types and contents to distinguish between VPN rules. Telecommuters can each use
a separate VPN rule to simultaneously access a ZyXEL Device at headquarters. They can use
different IPSec parameters. The local IP addresses (or ranges of addresses) of the rules
configured on the ZyXEL Device at headquarters can overlap. The local IP addresses of the
rules configured on the telecommuters’ IPSec routers should not overlap.
See the following table and figure for an example where three telecommuters each use a
different VPN rule for a VPN connection with a ZyXEL Device located at headquarters. The
ZyXEL Device at headquarters (HQ in the figure) identifies each incoming SA by its ID type
and content and uses the appropriate VPN rule to establish the VPN connection.
The ZyXEL Device at headquarters can also initiate VPN connections to the telecommuters
since it can find the telecommuters by resolving their domain names.
Figure 89
Telecommuters Using Unique VPN Rules Example
Table 57
Telecommuters Sharing One VPN Rule Example
FIELDS
TELECOMMUTERS
HEADQUARTERS
My IP Address:
0.0.0.0 (dynamic IP address
assigned by the ISP)
Public static IP address
Secure Gateway IP
Address:
Public static IP address
0.0.0.0 With this IP address only the
telecommuter can initiate the IPSec
tunnel.
Local IP Address:
Telecommuter A: 192.168.2.12
Telecommuter B: 192.168.3.2
Telecommuter C: 192.168.4.15
192.168.1.10
Remote IP
Address:
192.168.1.10
0.0.0.0 (N/A)
Summary of Contents for G.SHDSL.bis 4-port Security Gateway P-793H
Page 2: ......
Page 7: ...Safety Warnings P 793H User s Guide 7 This product is recyclable Dispose of it properly ...
Page 8: ...Safety Warnings P 793H User s Guide 8 ...
Page 30: ...List of Figures P 793H User s Guide 30 ...
Page 36: ...List of Tables P 793H User s Guide 36 ...
Page 38: ...38 ...
Page 68: ...Chapter 4 Point to 2 point Configuration P 793H User s Guide 68 ...
Page 70: ...70 ...
Page 114: ...Chapter 7 Network Address Translation NAT Screens P 793H User s Guide 114 ...
Page 116: ...116 ...
Page 152: ...Chapter 10 Content Filtering P 793H User s Guide 152 ...
Page 180: ...Chapter 12 Static Route P 793H User s Guide 180 ...
Page 194: ...Chapter 14 Dynamic DNS Setup P 793H User s Guide 194 ...
Page 216: ...Chapter 16 Universal Plug and Play UPnP P 793H User s Guide 216 ...
Page 217: ...217 PART IV Maintenance System 219 Logs 225 Tools 229 Diagnostic 235 ...
Page 218: ...218 ...
Page 224: ...Chapter 17 System P 793H User s Guide 224 ...
Page 234: ...Chapter 19 Tools P 793H User s Guide 234 ...
Page 238: ...238 ...
Page 244: ...Chapter 21 Introducing the SMT P 793H User s Guide 244 ...
Page 248: ...Chapter 22 General Setup P 793H User s Guide 248 ...
Page 256: ...Chapter 23 WAN Setup P 793H User s Guide 256 ...
Page 262: ...Chapter 24 LAN Setup P 793H User s Guide 262 ...
Page 278: ...Chapter 27 Static Route Setup P 793H User s Guide 278 ...
Page 308: ...Chapter 30 Filter Configuration P 793H User s Guide 308 ...
Page 310: ...Chapter 31 SNMP Configuration P 793H User s Guide 310 ...
Page 312: ...Chapter 32 System Password P 793H User s Guide 312 ...
Page 322: ...Chapter 33 System Information Diagnosis P 793H User s Guide 322 ...
Page 352: ...Chapter 37 Schedule Setup P 793H User s Guide 352 ...
Page 360: ...360 ...
Page 366: ...Appendix B Wall mounting Instructions P 793H User s Guide 366 ...
Page 400: ...Appendix F IP Address Assignment Conflicts P 793H User s Guide 400 ...
Page 404: ...Appendix G Common Services P 793H User s Guide 404 ...
Page 432: ...Appendix K Legal Information P 793H User s Guide 432 ...
Page 443: ...Index P 793H User s Guide 443 ...
Page 444: ...Index P 793H User s Guide 444 ...
















































