Chapter 8 Firewalls
P-793H User’s Guide
119
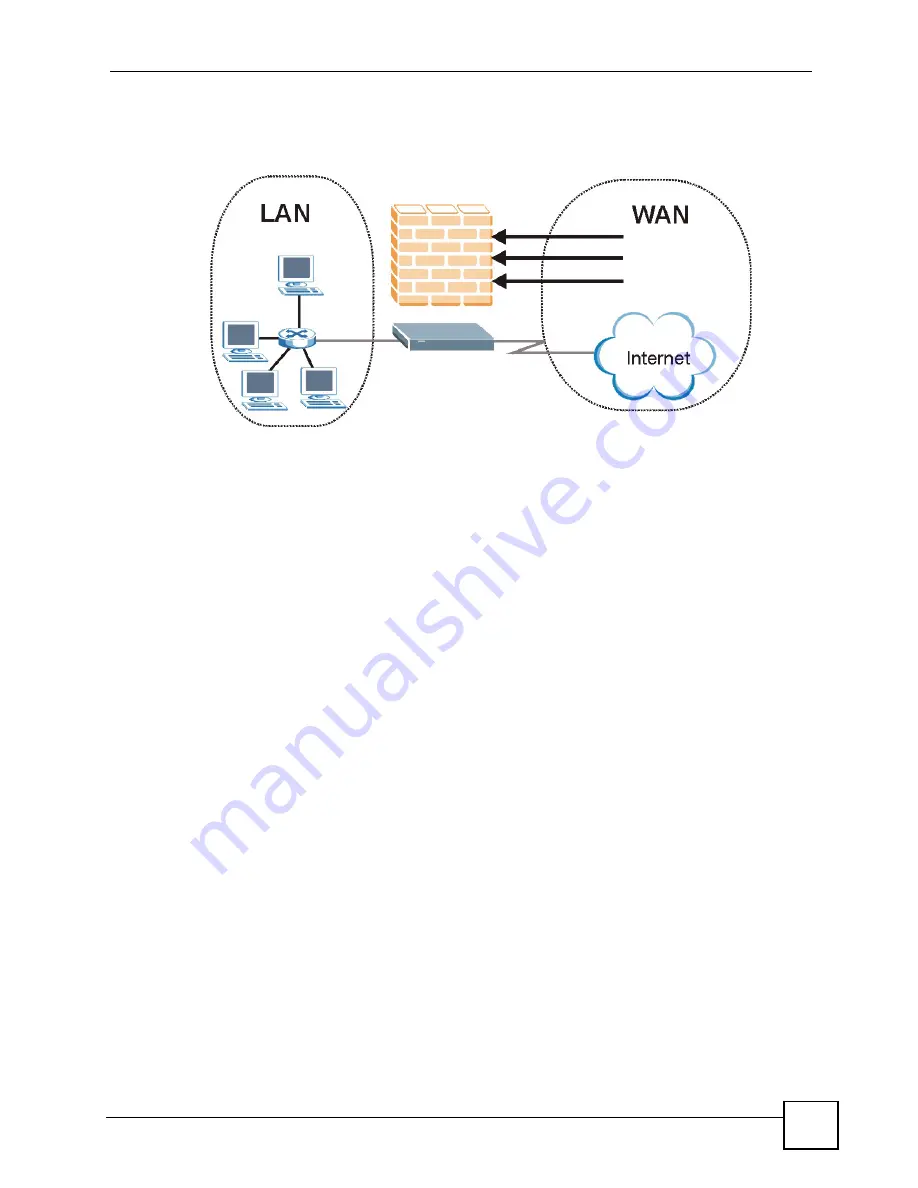
8.3.1 Denial of Service Attacks
Figure 52
ZyXEL Device Firewall Application
8.4 Denial of Service
Denials of Service (DoS) attacks are aimed at devices and networks with a connection to the
Internet. Their goal is not to steal information, but to disable a device or network so users no
longer have access to network resources. The ZyXEL Device is pre-configured to
automatically detect and thwart all known DoS attacks.
8.4.1 Basics
Computers share information over the Internet using a common language called TCP/IP. TCP/
IP, in turn, is a set of application protocols that perform specific functions. An “extension
number”, called the "TCP port" or "UDP port" identifies these protocols, such as HTTP
(Web), FTP (File Transfer Protocol), POP3 (E-mail), etc. For example, Web traffic by default
uses TCP port 80.
When computers communicate on the Internet, they are using the client/server model, where
the server "listens" on a specific TCP/UDP port for information requests from remote client
computers on the network. For example, a Web server typically listens on port 80. Please note
that while a computer may be intended for use over a single port, such as Web on port 80,
other ports are also active. If the person configuring or managing the computer is not careful, a
hacker could attack it over an unprotected port.
Some of the most common IP ports are shown in
8.4.2 Types of DoS Attacks
There are four types of DoS attacks:
1
Those that exploit bugs in a TCP/IP implementation.
2
Those that exploit weaknesses in the TCP/IP specification.
3
Brute-force attacks that flood a network with useless data.
Summary of Contents for G.SHDSL.bis 4-port Security Gateway P-793H
Page 2: ......
Page 7: ...Safety Warnings P 793H User s Guide 7 This product is recyclable Dispose of it properly ...
Page 8: ...Safety Warnings P 793H User s Guide 8 ...
Page 30: ...List of Figures P 793H User s Guide 30 ...
Page 36: ...List of Tables P 793H User s Guide 36 ...
Page 38: ...38 ...
Page 68: ...Chapter 4 Point to 2 point Configuration P 793H User s Guide 68 ...
Page 70: ...70 ...
Page 114: ...Chapter 7 Network Address Translation NAT Screens P 793H User s Guide 114 ...
Page 116: ...116 ...
Page 152: ...Chapter 10 Content Filtering P 793H User s Guide 152 ...
Page 180: ...Chapter 12 Static Route P 793H User s Guide 180 ...
Page 194: ...Chapter 14 Dynamic DNS Setup P 793H User s Guide 194 ...
Page 216: ...Chapter 16 Universal Plug and Play UPnP P 793H User s Guide 216 ...
Page 217: ...217 PART IV Maintenance System 219 Logs 225 Tools 229 Diagnostic 235 ...
Page 218: ...218 ...
Page 224: ...Chapter 17 System P 793H User s Guide 224 ...
Page 234: ...Chapter 19 Tools P 793H User s Guide 234 ...
Page 238: ...238 ...
Page 244: ...Chapter 21 Introducing the SMT P 793H User s Guide 244 ...
Page 248: ...Chapter 22 General Setup P 793H User s Guide 248 ...
Page 256: ...Chapter 23 WAN Setup P 793H User s Guide 256 ...
Page 262: ...Chapter 24 LAN Setup P 793H User s Guide 262 ...
Page 278: ...Chapter 27 Static Route Setup P 793H User s Guide 278 ...
Page 308: ...Chapter 30 Filter Configuration P 793H User s Guide 308 ...
Page 310: ...Chapter 31 SNMP Configuration P 793H User s Guide 310 ...
Page 312: ...Chapter 32 System Password P 793H User s Guide 312 ...
Page 322: ...Chapter 33 System Information Diagnosis P 793H User s Guide 322 ...
Page 352: ...Chapter 37 Schedule Setup P 793H User s Guide 352 ...
Page 360: ...360 ...
Page 366: ...Appendix B Wall mounting Instructions P 793H User s Guide 366 ...
Page 400: ...Appendix F IP Address Assignment Conflicts P 793H User s Guide 400 ...
Page 404: ...Appendix G Common Services P 793H User s Guide 404 ...
Page 432: ...Appendix K Legal Information P 793H User s Guide 432 ...
Page 443: ...Index P 793H User s Guide 443 ...
Page 444: ...Index P 793H User s Guide 444 ...
















































