Chapter 11 IPSec VPN
P-793H User’s Guide
168
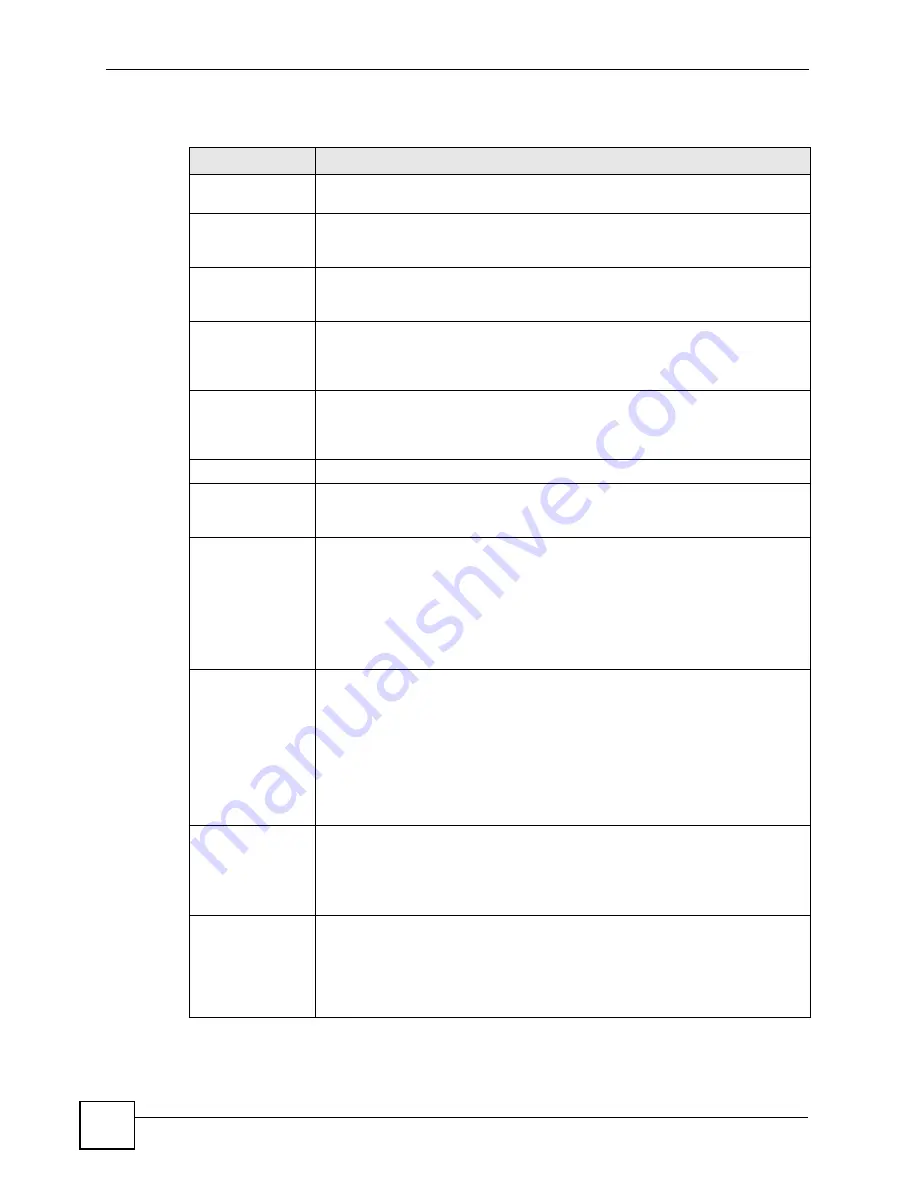
The following table describes the fields in this screen.
Table 53
VPN > Setup > Edit > Advanced
LABEL
DESCRIPTION
VPN - IKE -
Advanced Setup
Protocol
Enter the IP protocol number whose traffic is allowed to use the VPN tunnel.
Enter 0 to allow all IP protocols to use the VPN tunnel. See
for some common IP protocols.
Enable Replay
Detection
Select this to enable replay detection. As a VPN setup is processing intensive,
the system is vulnerable to Denial of Service (DoS) attacks. The IPSec receiver
can detect and reject old or duplicate packets to protect against replay attacks.
Local Start Port
End
Enter the port number or range of port numbers in the local network whose traffic
is allowed to use the VPN tunnel. Enter 0 in both fields to allow all port numbers in
the local network to use the VPN tunnel. See
common port numbers.
Remote Start Port
End
Enter the port number or range of port numbers in the remote network whose
traffic is allowed to use the VPN tunnel. Enter 0 in both fields to allow all port
numbers in the remote network to use the VPN tunnel. See
for some common port numbers.
Phase 1
Negotiation Mode
Select the negotiation mode for the IKE SA.
Main
is more secure than
Aggressive
. The ZyXEL Device and remote IPSec router must use the same
negotiation mode.
Pre-Shared Key
Type the pre-shared key the IKE SA uses. The ZyXEL Device and remote IPSec
router must use the same pre-shared key. If the keys are different, the ZyXEL
Device receives a “PYLD_MALFORMED” (payload malformed) packet.
You can use 8-31 ASCII characters or 16-62 hexadecimal ("0-9", "A-F")
characters. You must precede a hexadecimal key with a "0x” (zero x), which is
not counted as part of the 16-62 characters. For example, in
"0x0123456789ABCDEF", “0x” denotes that the key is hexadecimal and
“0123456789ABCDEF” is the key itself.
Encryption
Algorithm
Select one of the following encryption algorithms for the IKE SA. The algorithms
are listed in order from weakest to strongest.
Data Encryption Standard (
DES
) is a widely used (but breakable) method of data
encryption. It applies a 56-bit key to each 64-bit block of data.
Triple DES (
3DES
) is a variant of DES. It iterates three times with three separate
keys, effectively tripling the strength of DES.
Advanced Encryption Standard (
AES
) is a newer method of data encryption that
also uses a secret key. AES applies a 128-bit key to 128-bit blocks of data.
Select
NULL
to set up a VPN tunnel without encryption.
Authentication
Algorithm
Select one of the following authentication algorithms for the IKE SA. The
algorithms are listed in order from weakest to strongest.
Message Digest 5 (
MD5
) produces a 128-bit digest to authenticate packets.
Secure Hash Algorithm (
SHA1
) produces a 160-bit digest to authenticate
packets.
SA Life Time
(Seconds)
Enter the length of time before the ZyXEL Device automatically renegotiates the
IKE SA. It may range from 60 to 3,000,000 seconds (almost 35 days).
A low value increases security by forcing the two VPN gateways to update the
encryption and authentication keys. However, if every time the IKE SA is
renegotiated, any users trying to establish IPSec SA experience delays. (Existing
IPSec SA are not affected.)
Summary of Contents for G.SHDSL.bis 4-port Security Gateway P-793H
Page 2: ......
Page 7: ...Safety Warnings P 793H User s Guide 7 This product is recyclable Dispose of it properly ...
Page 8: ...Safety Warnings P 793H User s Guide 8 ...
Page 30: ...List of Figures P 793H User s Guide 30 ...
Page 36: ...List of Tables P 793H User s Guide 36 ...
Page 38: ...38 ...
Page 68: ...Chapter 4 Point to 2 point Configuration P 793H User s Guide 68 ...
Page 70: ...70 ...
Page 114: ...Chapter 7 Network Address Translation NAT Screens P 793H User s Guide 114 ...
Page 116: ...116 ...
Page 152: ...Chapter 10 Content Filtering P 793H User s Guide 152 ...
Page 180: ...Chapter 12 Static Route P 793H User s Guide 180 ...
Page 194: ...Chapter 14 Dynamic DNS Setup P 793H User s Guide 194 ...
Page 216: ...Chapter 16 Universal Plug and Play UPnP P 793H User s Guide 216 ...
Page 217: ...217 PART IV Maintenance System 219 Logs 225 Tools 229 Diagnostic 235 ...
Page 218: ...218 ...
Page 224: ...Chapter 17 System P 793H User s Guide 224 ...
Page 234: ...Chapter 19 Tools P 793H User s Guide 234 ...
Page 238: ...238 ...
Page 244: ...Chapter 21 Introducing the SMT P 793H User s Guide 244 ...
Page 248: ...Chapter 22 General Setup P 793H User s Guide 248 ...
Page 256: ...Chapter 23 WAN Setup P 793H User s Guide 256 ...
Page 262: ...Chapter 24 LAN Setup P 793H User s Guide 262 ...
Page 278: ...Chapter 27 Static Route Setup P 793H User s Guide 278 ...
Page 308: ...Chapter 30 Filter Configuration P 793H User s Guide 308 ...
Page 310: ...Chapter 31 SNMP Configuration P 793H User s Guide 310 ...
Page 312: ...Chapter 32 System Password P 793H User s Guide 312 ...
Page 322: ...Chapter 33 System Information Diagnosis P 793H User s Guide 322 ...
Page 352: ...Chapter 37 Schedule Setup P 793H User s Guide 352 ...
Page 360: ...360 ...
Page 366: ...Appendix B Wall mounting Instructions P 793H User s Guide 366 ...
Page 400: ...Appendix F IP Address Assignment Conflicts P 793H User s Guide 400 ...
Page 404: ...Appendix G Common Services P 793H User s Guide 404 ...
Page 432: ...Appendix K Legal Information P 793H User s Guide 432 ...
Page 443: ...Index P 793H User s Guide 443 ...
Page 444: ...Index P 793H User s Guide 444 ...
















































