Chapter 25 Firewall
UAG5100 User’s Guide
246
Default Firewall Behavior
Firewall rules are grouped based on the direction of travel of packets to which they apply. Here is
the default firewall behavior for traffic going through the UAG in various directions.
To-Device Rules
Rules with Device as the To Zone apply to traffic going to the UAG itself. By default:
• The firewall allows only LAN, or WAN computers to access or manage the UAG.
• The UAG allows DHCP traffic from any interface to the UAG.
• The UAG drops most packets from the DMZ zone to the UAG itself and generates a log except for
DNS and NetBIOS traffic.
• The UAG drops most packets from the WAN zone to the UAG itself and generates a log except for
AH, ESP, GRE, HTTPS, IKE, NATT.
When you configure a firewall rule for packets destined for the UAG itself, make sure it does not
conflict with your service control rule. See
for more information about
service control (remote management). The UAG checks the firewall rules before the service control
rules for traffic destined for the UAG.
A From Any To Device direction rule applies to traffic from an interface which is not in a zone.
Global Firewall Rules
Firewall rules with from any and/or to any as the packet direction are called global firewall rules.
The global firewall rules are the only firewall rules that apply to an interface or VPN tunnel that is
not included in a zone. The from any rules apply to traffic coming from the interface and the to
any rules apply to traffic going to the interface.
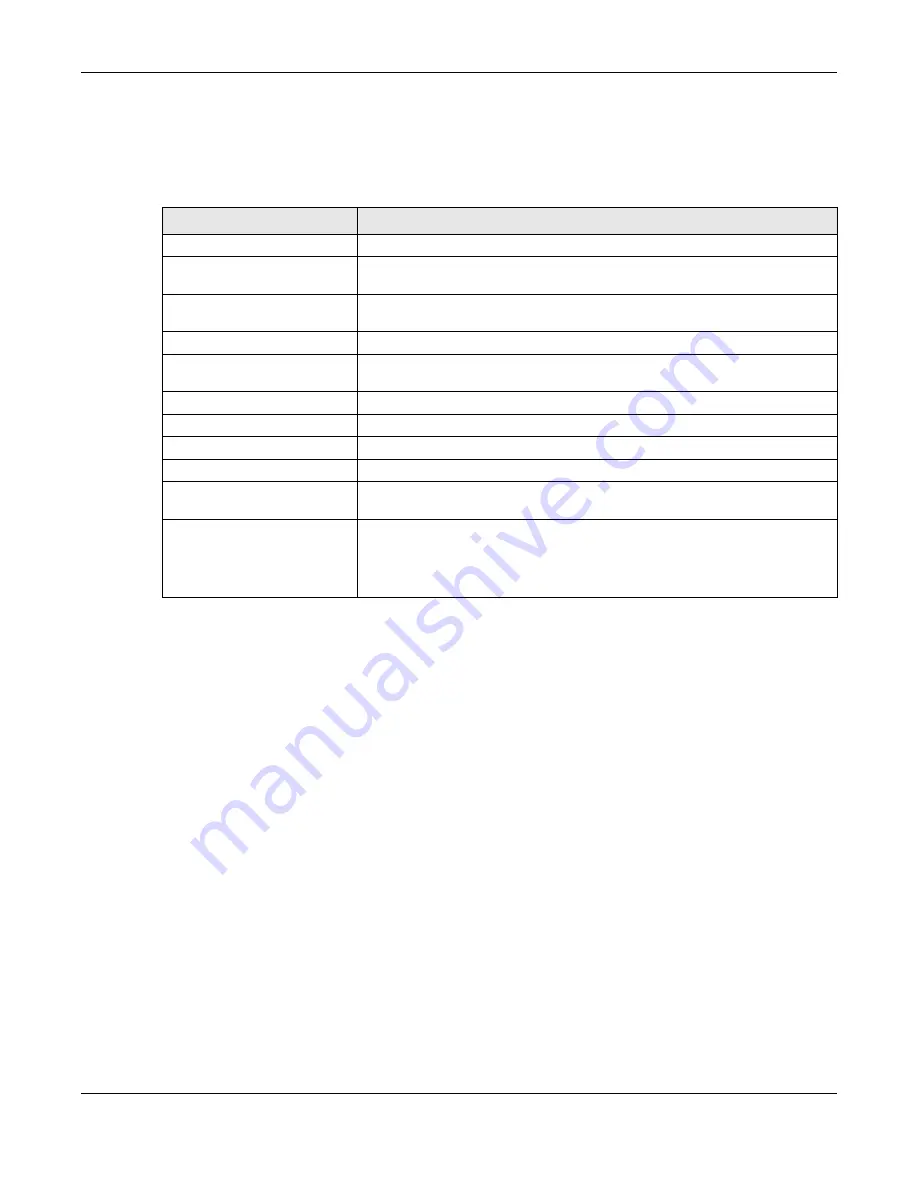
Table 108
Default Firewall Behavior
FROM ZONE TO ZONE
BEHAVIOR
From any to Device
DHCP traffic from any interface to the UAG is allowed.
From LAN1 to any (other than
the UAG)
Traffic from the LAN1 to any of the networks connected to the UAG is allowed.
From LAN2 to any (other than
the UAG)
Traffic from the LAN2 to any of the networks connected to the UAG is allowed.
From DMZ to WAN
Traffic from the DMZ to the WAN is allowed.
From IPSec VPN to any (other
than the UAG)
Traffic from the IPSec VPN zone to any of the networks connected to the UAG
is allowed.
From LAN1 to Device
Traffic from the LAN1 to the UAG itself is allowed.
From LAN2 to Device
Traffic from the LAN2 to the UAG itself is allowed.
From DMZ to Device
DNS and NetBIOS traffic from the DMZ to the UAG itself is allowed.
From IPSec VPN to Device
Traffic from the IPSec VPN zone to the UAG itself is allowed.
From WAN to Device
The default services listed in
the WAN to the UAG itself. All other WAN to UAG traffic is dropped.
From any to any
Traffic that does not match any firewall rule is dropped. This includes traffic
from the WAN to any of the networks behind the UAG.
This also includes traffic to or from interfaces that are not assigned to a zone
(extra-zone traffic).
















































