G-3000H User’s Guide
126
Chapter 11 Certificates
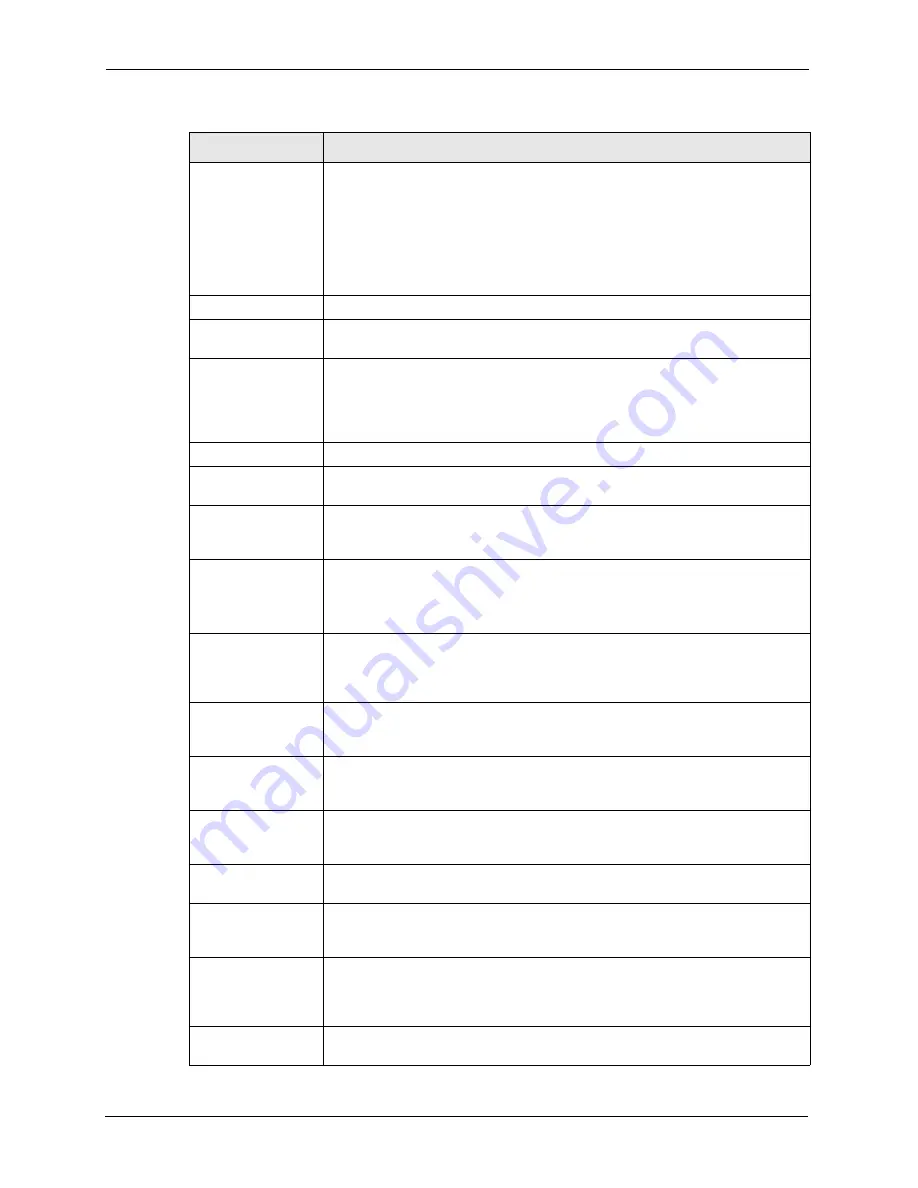
Certificate Path
Click the
Refresh
button to have this read-only text box display the hierarchy of
certification authorities that validate the certificate (and the certificate itself).
If the issuing certification authority is one that you have imported as a trusted
certification authority, it may be the only certification authority in the list (along
with the certificate itself). If the certificate is a self-signed certificate, the
certificate itself is the only one in the list. The ZyAIR does not trust the certificate
and displays “Not trusted” in this field if any certificate on the path has expired or
been revoked.
Refresh
Click
Refresh
to display the certification path.
Certificate
Information
These read-only fields display detailed information about the certificate.
Type
This field displays general information about the certificate. CA-signed means
that a Certification Authority signed the certificate. Self-signed means that the
certificate’s owner signed the certificate (not a certification authority). “X.509”
means that this certificate was created and signed according to the ITU-T X.509
recommendation that defines the formats for public-key certificates.
Version
This field displays the X.509 version number.
Serial Number
This field displays the certificate’s identification number given by the certification
authority or generated by the ZyAIR.
Subject
This field displays information that identifies the owner of the certificate, such as
Common Name (CN), Organizational Unit (OU), Organization (O) and Country
(C).
Issuer
This field displays identifying information about the certificate’s issuing
certification authority, such as Common Name, Organizational Unit,
Organization and Country.
With self-signed certificates, this is the same as the
Subject Name
field.
Signature Algorithm
This field displays the type of algorithm that was used to sign the certificate. The
ZyAIR uses rsa-pkcs1-sha1 (RSA public-private key encryption algorithm and
the SHA1 hash algorithm). Some certification authorities may use ras-pkcs1-
md5 (RSA public-private key encryption algorithm and the MD5 hash algorithm).
Valid From
This field displays the date that the certificate becomes applicable. The text
displays in red and includes a Not Yet Valid! message if the certificate has not
yet become applicable.
Valid To
This field displays the date that the certificate expires. The text displays in red
and includes an Expiring! or Expired! message if the certificate is about to expire
or has already expired.
Key Algorithm
This field displays the type of algorithm that was used to generate the
certificate’s key pair (the ZyAIR uses RSA encryption) and the length of the key
set in bits (1024 bits for example).
Subject Alternative
Name
This field displays the certificate owner‘s IP address (IP), domain name (DNS) or
e-mail address (EMAIL).
Key Usage
This field displays for what functions the certificate’s key can be used. For
example, “DigitalSignature” means that the key can be used to sign certificates
and “KeyEncipherment” means that the key can be used to encrypt text.
Basic Constraint
This field displays general information about the certificate. For example,
Subject Type=CA means that this is a certification authority’s certificate and
“Path Length Constraint=1” means that there can only be one certification
authority in the certificate’s path.
MD5 Fingerprint
This is the certificate’s message digest that the ZyAIR calculated using the MD5
algorithm.
Table 41
My Certificate Details (continued)
LABEL
DESCRIPTION
Summary of Contents for ZyAIR G-3000H
Page 1: ...G 3000H 802 11g Wireless Access Point User s Guide Version 3 50 1 2006 ...
Page 22: ...G 3000H User s Guide 22 List of Figures ...
Page 26: ...G 3000H User s Guide 26 List of Tables ...
Page 114: ...G 3000H User s Guide 114 Chapter 9 VLAN ...
Page 134: ...G 3000H User s Guide 134 Chapter 11 Certificates ...
Page 164: ...G 3000H User s Guide 164 Chapter 15 Introducing the SMT ...
Page 180: ...G 3000H User s Guide 180 Chapter 17 LAN Setup ...
Page 218: ...G 3000H User s Guide 218 Chapter 24 System Maintenance and Information ...
Page 224: ...G 3000H User s Guide 224 Appendix C Power over Ethernet PoE Specifications ...
Page 226: ...G 3000H User s Guide 226 Appendix D Brute Force Password Guessing Protection ...
Page 238: ...G 3000H User s Guide 238 Appendix E Setting up Your Computer s IP Address ...
Page 242: ...G 3000H User s Guide 242 Appendix F IP Address Assignment Conflicts ...
Page 254: ...G 3000H User s Guide 254 Appendix G Wireless LANs ...
Page 262: ...G 3000H User s Guide 262 Appendix H IP Subnetting ...
Page 264: ...G 3000H User s Guide 264 Appendix I Command Interpreter ...
Page 268: ...G 3000H User s Guide 268 Appendix J Log Descriptions ...
Page 272: ...G 3000H User s Guide 272 Appendix L Power Adaptor Specifications ...
Page 280: ...G 3000H User s Guide 280 Appendix M Text File Based Auto Configuration ...
Page 294: ...G 3000H User s Guide 294 Appendix N Wireless LAN Manager ...
Page 299: ...G 3000H User s Guide Index 299 ZyNOS F W Version 196 zyxel prowireless mib 287 ...
















































