ZyWALL 70 User’s Guide
Chapter 15 Certificates
277
15.9 Trusted CAs
Click
CERTIFICATES
,
Trusted CAs
to open the
Trusted CAs
screen. This screen displays
a summary list of certificates of the certification authorities that you have set the ZyWALL to
accept as trusted. The ZyWALL accepts any valid certificate signed by a certification
authority on this list as being trustworthy; thus you do not need to import any certificate that is
signed by one of these certification authorities. See the following figure.
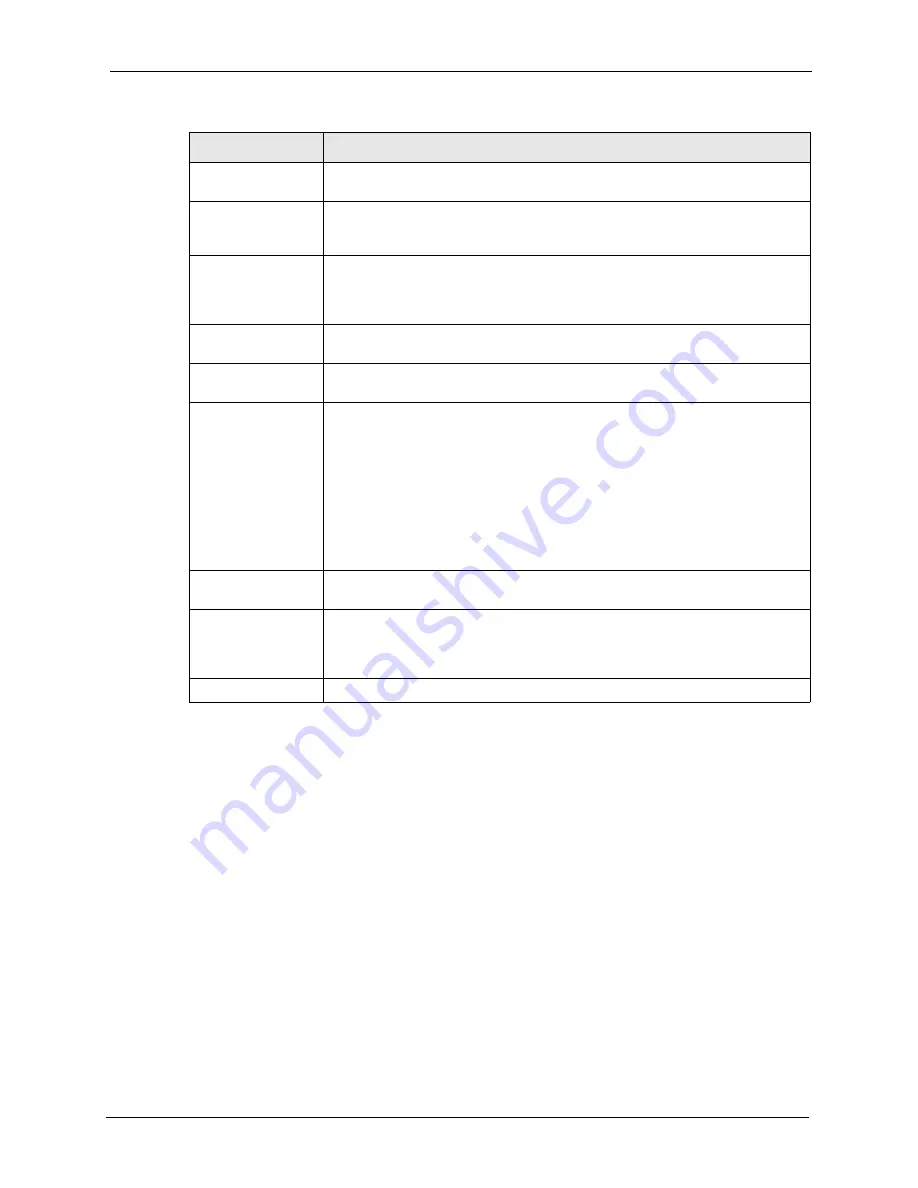
Subject Alternative
Name
This field displays the certificate owner‘s IP address (IP), domain name (DNS) or
e-mail address (EMAIL).
Key Usage
This field displays for what functions the certificate’s key can be used. For
example, “DigitalSignature” means that the key can be used to sign certificates
and “KeyEncipherment” means that the key can be used to encrypt text.
Basic Constraint
This field displays general information about the certificate. For example,
Subject Type=CA means that this is a certification authority’s certificate and
“Path Length Constraint=1” means that there can only be one certification
authority in the certificate’s path.
MD5 Fingerprint
This is the certificate’s message digest that the ZyWALL calculated using the
MD5 algorithm.
SHA1 Fingerprint
This is the certificate’s message digest that the ZyWALL calculated using the
SHA1 algorithm.
Certificate in PEM
(Base-64) Encoded
Format
This read-only text box displays the certificate or certification request in Privacy
Enhanced Mail (PEM) format. PEM uses 64 ASCII characters to convert the
binary certificate into a printable form.
You can copy and paste a certification request into a certification authority’s web
page, an e-mail that you send to the certification authority or a text editor and
save the file on a management computer for later manual enrollment.
You can copy and paste a certificate into an e-mail to send to friends or
colleagues or you can copy and paste a certificate into a text editor and save the
file on a management computer for later distribution (via floppy disk for
example).
Export
Click this button and then
Save
in the
File Download
screen. The
Save As
screen opens, browse to the location that you want to use and click
Save
.
Apply
Click
Apply
to save your changes back to the ZyWALL. You can only change
the name, except in the case of a self-signed certificate, which you can also set
to be the default self-signed certificate that signs the imported trusted remote
host certificates.
Cancel
Click
Cancel
to quit and return to the
My Certificates
screen.
Table 86
My Certificate Details (continued)
LABEL
DESCRIPTION
Summary of Contents for ZyWALL 70
Page 1: ...ZyWALL 70 Internet Security Appliance User s Guide Version 3 64 3 2005 ...
Page 2: ......
Page 38: ...ZyWALL 70 User s Guide 38 List of Figures ...
Page 46: ...ZyWALL 70 User s Guide 46 List of Tables ...
Page 74: ...ZyWALL 70 User s Guide 74 Chapter 2 Introducing the Web Configurator ...
Page 92: ...ZyWALL 70 User s Guide 92 Chapter 3 Wizard Setup ...
Page 102: ...ZyWALL 70 User s Guide 102 Chapter 4 LAN Screens ...
Page 108: ...ZyWALL 70 User s Guide 108 Chapter 5 Bridge Screens ...
Page 130: ...ZyWALL 70 User s Guide 130 Chapter 6 Wireless LAN ...
Page 136: ...ZyWALL 70 User s Guide 136 Chapter 7 WAN Screens Figure 45 WAN General ...
Page 155: ...ZyWALL 70 User s Guide Chapter 7 WAN Screens 155 Figure 55 Dial Backup Setup ...
Page 234: ...ZyWALL 70 User s Guide 234 Chapter 13 Introduction to IPSec ...
Page 275: ...ZyWALL 70 User s Guide Chapter 15 Certificates 275 Figure 125 My Certificate Details ...
Page 294: ...ZyWALL 70 User s Guide 294 Chapter 16 Authentication Server Figure 136 Local User Database ...
Page 314: ...ZyWALL 70 User s Guide 314 Chapter 17 Network Address Translation NAT ...
Page 318: ...ZyWALL 70 User s Guide 318 Chapter 18 Static Route ...
Page 324: ...ZyWALL 70 User s Guide 324 Chapter 19 Policy Route ...
Page 340: ...ZyWALL 70 User s Guide 340 Chapter 20 Bandwidth Management ...
Page 376: ...ZyWALL 70 User s Guide 376 Chapter 22 Remote Management ...
Page 390: ...ZyWALL 70 User s Guide 390 Chapter 24 Logs Screens Figure 194 Log Settings ...
Page 413: ...ZyWALL 70 User s Guide Chapter 25 Maintenance 413 Figure 216 Restart Screen ...
Page 414: ...ZyWALL 70 User s Guide 414 Chapter 25 Maintenance ...
Page 440: ...ZyWALL 70 User s Guide 440 Chapter 28 WAN and Dial Backup Setup ...
Page 456: ...ZyWALL 70 User s Guide 456 Chapter 31 DMZ Setup ...
Page 460: ...ZyWALL 70 User s Guide 460 Chapter 32 Route Setup ...
Page 470: ...ZyWALL 70 User s Guide 470 Chapter 33 Remote Node Setup ...
Page 522: ...ZyWALL 70 User s Guide 522 Chapter 39 System Information Diagnosis ...
Page 538: ...ZyWALL 70 User s Guide 538 Chapter 40 Firmware and Configuration File Maintenance ...
Page 550: ...ZyWALL 70 User s Guide 550 Chapter 42 Remote Management ...
Page 558: ...ZyWALL 70 User s Guide 558 Chapter 43 IP Policy Routing ...
Page 573: ...ZyWALL 70 User s Guide Chapter 45 Troubleshooting 573 Figure 360 Java Sun ...
Page 574: ...ZyWALL 70 User s Guide 574 Chapter 45 Troubleshooting ...
Page 582: ...ZyWALL 70 User s Guide 582 Appendix B Removing and Installing a Fuse ...
Page 602: ...ZyWALL 70 User s Guide 602 Appendix D IP Subnetting ...
Page 608: ...ZyWALL 70 User s Guide 608 Appendix F PPTP ...
Page 626: ...ZyWALL 70 User s Guide 626 Appendix H Triangle Route ...
Page 656: ...ZyWALL 70 User s Guide 656 Appendix K Importing Certificates ...
Page 658: ...ZyWALL 70 User s Guide 658 Appendix L Command Interpreter ...
Page 664: ...ZyWALL 70 User s Guide 664 Appendix M Firewall Commands ...
Page 668: ...ZyWALL 70 User s Guide 668 Appendix N NetBIOS Filter Commands ...
Page 674: ...ZyWALL 70 User s Guide 674 Appendix P Brute Force Password Guessing Protection ...
Page 696: ...ZyWALL 70 User s Guide 696 Appendix R Log Descriptions ...




































