ZyWALL 35 User’s Guide
252
Chapter 14 VPN Screens
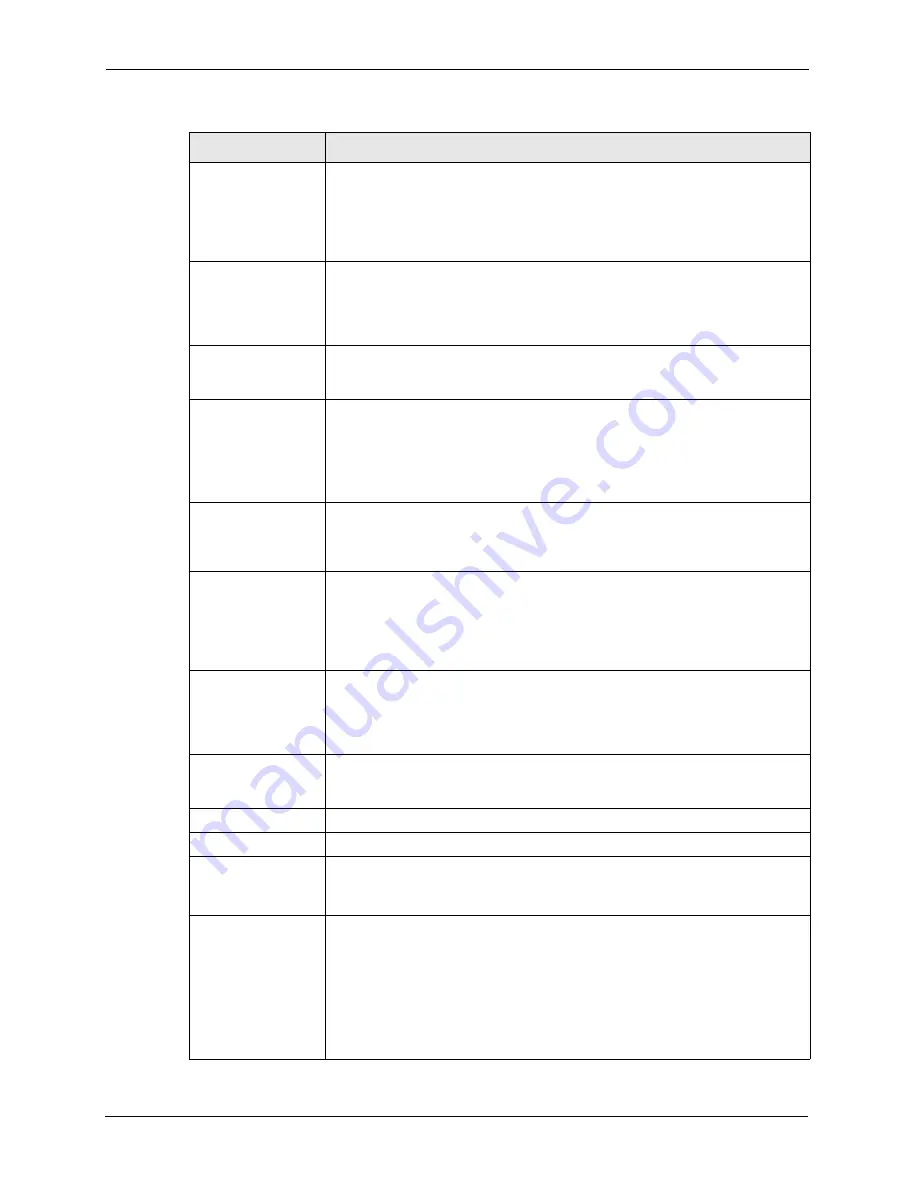
Starting IP Address
When the
Address Type
field is configured to
Single Address
, enter a (static)
IP address on the LAN behind your ZyWALL. When the
Address Type
field is
configured to
Range Address
, enter the beginning (static) IP address, in a
range of computers on the LAN behind your ZyWALL. When the
Address Type
field is configured to
Subnet Address
, this is a (static) IP address on the LAN
behind your ZyWALL.
Ending IP Address/
Subnet Mask
When the
Address Type
field is configured to
Single Address
, this field is N/A.
When the
Address Type
field is configured to
Range Address
, enter the end
(static) IP address, in a range of computers on the LAN behind your ZyWALL.
When the
Address Type
field is configured to
Subnet Address
, this is a subnet
mask on the LAN behind your ZyWALL.
Local Port
0 is the default and signifies any port. Type a port number from 0 to 65535 in the
Start
and
End
fields. Some of the most common IP ports are: 21, FTP; 53, DNS;
23, Telnet; 80, HTTP; 25, SMTP; 110, POP3.
Remote Network
Remote IP addresses must be static and correspond to the remote IPSec
router's configured local IP addresses.
Two active SAs cannot have the local and remote IP address(es) both the same.
Two active SAs can have the same local or remote IP address, but not both.
You can configure multiple SAs between the same local and remote IP
addresses, as long as only one is active at any time.
Address Type
Use the drop-down list box to choose
Single Address
,
Range Address
, or
Subnet Address
. Select
Single Address
with a single IP address. Select
Range Address
for a specific range of IP addresses. Select
Subnet Address
to specify IP addresses on a network by their subnet mask.
Starting IP Address
When the
Address Type
field is configured to
Single Address
, enter a (static)
IP address on the network behind the remote IPSec router. When the Addr Type
field is configured to
Range Address
, enter the beginning (static) IP address, in
a range of computers on the network behind the remote IPSec router. When the
Address Type
field is configured to
Subnet Address
, enter a (static) IP
address on the network behind the remote IPSec router.
Ending IP Address/
Subnet Mask
When the
Address Type
field is configured to
Single Address
, this field is N/A.
When the
Address Type
field is configured to
Range Address
, enter the end
(static) IP address, in a range of computers on the network behind the remote
IPSec router. When the
Address Type
field is configured to
Subnet Address
,
enter a subnet mask on the network behind the remote IPSec router.
Remote Port
0 is the default and signifies any port. Type a port number from 0 to 65535 in the
Start
and
End
fields. Some of the most common IP ports are: 21, FTP; 53, DNS;
23, Telnet; 80, HTTP; 25, SMTP; 110, POP3.
IPSec Proposal
Encapsulation Mode Select
Tunnel
mode or
Transport
mode.
Active Protocol
Select the security protocols used for an SA.
Both
AH
and
ESP
increase ZyWALL processing requirements and
communications latency (delay).
Encryption Algorithm When
DES
is used for data communications, both sender and receiver must
know the same secret key, which can be used to encrypt and decrypt the
message or to generate and verify a message authentication code. The DES
encryption algorithm uses a 56-bit key. Triple DES (
3DES
) is a variation on DES
that uses a 168-bit key. As a result,
3DES
is more secure than
DES
. It also
requires more processing power, resulting in increased latency and decreased
throughput. This implementation of
AES
uses a 128-bit key.
AES
is faster than
3DES
. Select
NULL
to set up a tunnel without encryption. When you select
NULL
, you do not enter an encryption key.
Table 75
VPN Rules (IKE): Network Policy Edit (continued)
LABEL
DESCRIPTION
Summary of Contents for ZyXEL ZyWALL 35
Page 1: ...ZyWALL 35 Internet Security Appliance User s Guide Version 3 64 3 2005 ...
Page 2: ......
Page 38: ...ZyWALL 35 User s Guide 36 ...
Page 46: ...ZyWALL 35 User s Guide 44 ...
Page 74: ...ZyWALL 35 User s Guide 72 Chapter 2 Introducing the Web Configurator ...
Page 90: ...ZyWALL 35 User s Guide 88 Chapter 3 Wizard Setup ...
Page 100: ...ZyWALL 35 User s Guide 98 Chapter 4 LAN Screens ...
Page 106: ...ZyWALL 35 User s Guide 104 Chapter 5 Bridge Screens ...
Page 128: ...ZyWALL 35 User s Guide 126 Chapter 6 Wireless LAN ...
Page 135: ...ZyWALL 35 User s Guide Chapter 7 WAN Screens 133 Figure 47 General ...
Page 152: ...ZyWALL 35 User s Guide 150 Chapter 7 WAN Screens Figure 57 Dial Backup Setup ...
Page 158: ...ZyWALL 35 User s Guide 156 Chapter 7 WAN Screens ...
Page 166: ...ZyWALL 35 User s Guide 164 Chapter 8 DMZ Screens ...
Page 234: ...ZyWALL 35 User s Guide 232 Chapter 13 Introduction to IPSec ...
Page 275: ...ZyWALL 35 User s Guide Chapter 15 Certificates 273 Figure 129 My Certificate Details ...
Page 294: ...ZyWALL 35 User s Guide 292 Chapter 16 Authentication Server Figure 140 Local User Database ...
Page 314: ...ZyWALL 35 User s Guide 312 Chapter 17 Network Address Translation NAT ...
Page 318: ...ZyWALL 35 User s Guide 316 Chapter 18 Static Route ...
Page 324: ...ZyWALL 35 User s Guide 322 Chapter 19 Policy Route ...
Page 340: ...ZyWALL 35 User s Guide 338 Chapter 20 Bandwidth Management ...
Page 376: ...ZyWALL 35 User s Guide 374 Chapter 22 Remote Management ...
Page 390: ...ZyWALL 35 User s Guide 388 Chapter 24 Logs Screens Figure 198 Log Settings ...
Page 413: ...ZyWALL 35 User s Guide Chapter 25 Maintenance 411 Figure 220 Restart Screen ...
Page 414: ...ZyWALL 35 User s Guide 412 Chapter 25 Maintenance ...
Page 440: ...ZyWALL 35 User s Guide 438 Chapter 28 WAN and Dial Backup Setup ...
Page 456: ...ZyWALL 35 User s Guide 454 Chapter 31 DMZ Setup ...
Page 460: ...ZyWALL 35 User s Guide 458 Chapter 32 Route Setup ...
Page 470: ...ZyWALL 35 User s Guide 468 Chapter 33 Remote Node Setup ...
Page 522: ...ZyWALL 35 User s Guide 520 Chapter 39 System Information Diagnosis ...
Page 538: ...ZyWALL 35 User s Guide 536 Chapter 40 Firmware and Configuration File Maintenance ...
Page 550: ...ZyWALL 35 User s Guide 548 Chapter 42 Remote Management ...
Page 558: ...ZyWALL 35 User s Guide 556 Chapter 43 IP Policy Routing ...
Page 574: ...ZyWALL 35 User s Guide 572 Chapter 45 Troubleshooting Figure 364 Java Sun ...
Page 602: ...ZyWALL 35 User s Guide 600 Appendix C IP Subnetting ...
Page 608: ...ZyWALL 35 User s Guide 606 Appendix E PPTP ...
Page 626: ...ZyWALL 35 User s Guide 624 Appendix G Triangle Route ...
Page 656: ...ZyWALL 35 User s Guide 654 Appendix J Importing Certificates ...
Page 658: ...ZyWALL 35 User s Guide 656 Appendix K Command Interpreter ...
Page 664: ...ZyWALL 35 User s Guide 662 Appendix L Firewall Commands ...
Page 668: ...ZyWALL 35 User s Guide 666 Appendix M NetBIOS Filter Commands ...
Page 674: ...ZyWALL 35 User s Guide 672 Appendix O Brute Force Password Guessing Protection ...
Page 696: ...ZyWALL 35 User s Guide 694 Appendix Q Log Descriptions ...
















































