ZyWALL 35 User’s Guide
168
Chapter 9 Firewalls
9.4.2 Types of DoS Attacks
There are four types of DoS attacks:
1
Those that exploit bugs in a TCP/IP implementation.
2
Those that exploit weaknesses in the TCP/IP specification.
3
Brute-force attacks that flood a network with useless data.
4
IP Spoofing.
• "
Ping of Death
" and "
Teardrop
" attacks exploit bugs in the TCP/IP implementations of
various computer and host systems.
a
Ping of Death uses a "ping" utility to create an IP packet that exceeds
the maximum 65,536 bytes of data allowed by the IP specification.
The oversize packet is then sent to an unsuspecting system. Systems
may crash, hang or reboot.
b
Teardrop attack exploits weaknesses in the reassembly of IP packet
fragments. As data is transmitted through a network, IP packets are
often broken up into smaller chunks. Each fragment looks like the
original IP packet except that it contains an offset field that says, for
instance, "This fragment is carrying bytes 200 through 400 of the
original (non fragmented) IP packet." The Teardrop program creates a
series of IP fragments with overlapping offset fields. When these
fragments are reassembled at the destination, some systems will
crash, hang, or reboot.
• Weaknesses in the TCP/IP specification leave it open to "
SYN Flood
" and "
LAND
"
attacks. These attacks are executed during the handshake that initiates a communication
session between two applications.
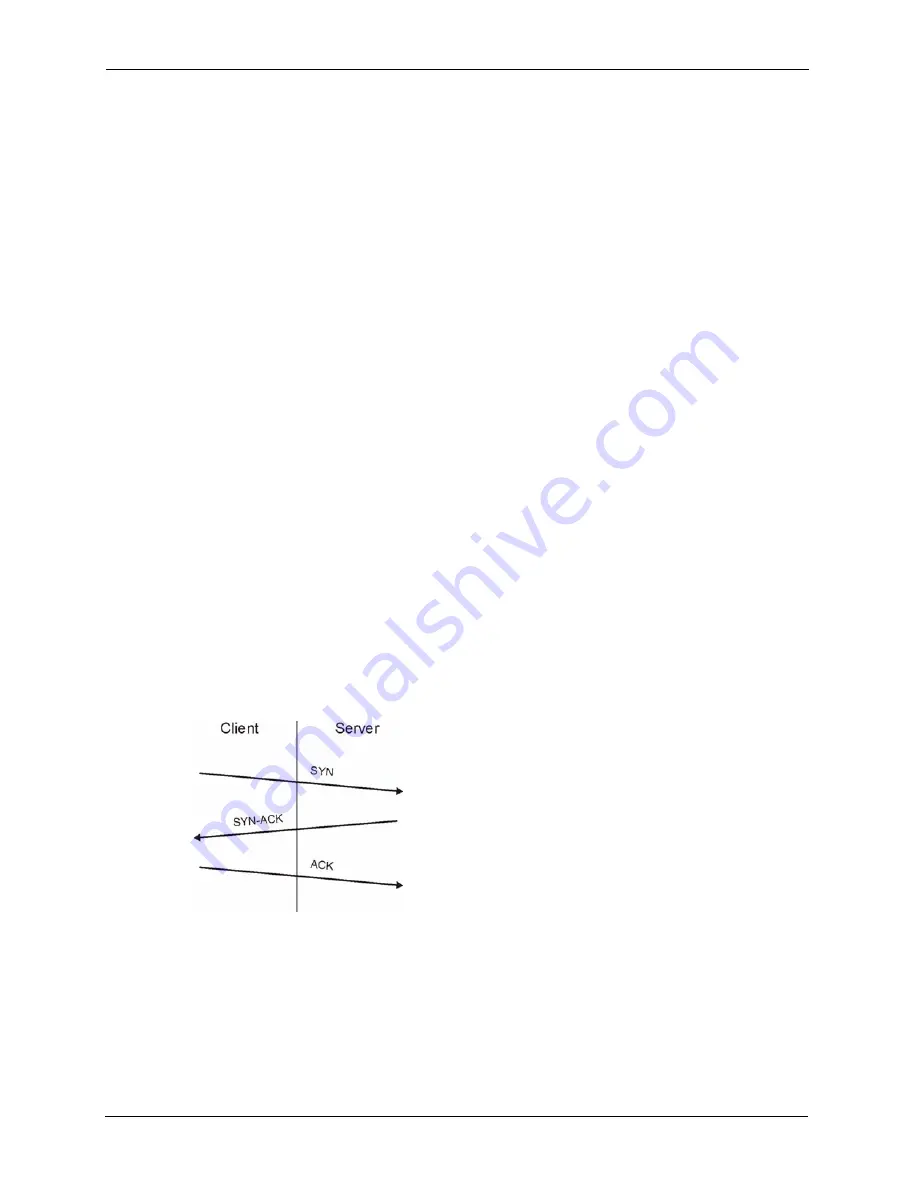
Figure 66
Three-Way Handshake
Under normal circumstances, the application that initiates a session sends a SYN
(synchronize) packet to the receiving server. The receiver sends back an ACK
(acknowledgment) packet and its own SYN, and then the initiator responds with an ACK
(acknowledgment). After this handshake, a connection is established.
a
SYN Attack
floods a targeted system with a series of SYN packets.
Each packet causes the targeted system to issue a SYN-ACK
Summary of Contents for ZyXEL ZyWALL 35
Page 1: ...ZyWALL 35 Internet Security Appliance User s Guide Version 3 64 3 2005 ...
Page 2: ......
Page 38: ...ZyWALL 35 User s Guide 36 ...
Page 46: ...ZyWALL 35 User s Guide 44 ...
Page 74: ...ZyWALL 35 User s Guide 72 Chapter 2 Introducing the Web Configurator ...
Page 90: ...ZyWALL 35 User s Guide 88 Chapter 3 Wizard Setup ...
Page 100: ...ZyWALL 35 User s Guide 98 Chapter 4 LAN Screens ...
Page 106: ...ZyWALL 35 User s Guide 104 Chapter 5 Bridge Screens ...
Page 128: ...ZyWALL 35 User s Guide 126 Chapter 6 Wireless LAN ...
Page 135: ...ZyWALL 35 User s Guide Chapter 7 WAN Screens 133 Figure 47 General ...
Page 152: ...ZyWALL 35 User s Guide 150 Chapter 7 WAN Screens Figure 57 Dial Backup Setup ...
Page 158: ...ZyWALL 35 User s Guide 156 Chapter 7 WAN Screens ...
Page 166: ...ZyWALL 35 User s Guide 164 Chapter 8 DMZ Screens ...
Page 234: ...ZyWALL 35 User s Guide 232 Chapter 13 Introduction to IPSec ...
Page 275: ...ZyWALL 35 User s Guide Chapter 15 Certificates 273 Figure 129 My Certificate Details ...
Page 294: ...ZyWALL 35 User s Guide 292 Chapter 16 Authentication Server Figure 140 Local User Database ...
Page 314: ...ZyWALL 35 User s Guide 312 Chapter 17 Network Address Translation NAT ...
Page 318: ...ZyWALL 35 User s Guide 316 Chapter 18 Static Route ...
Page 324: ...ZyWALL 35 User s Guide 322 Chapter 19 Policy Route ...
Page 340: ...ZyWALL 35 User s Guide 338 Chapter 20 Bandwidth Management ...
Page 376: ...ZyWALL 35 User s Guide 374 Chapter 22 Remote Management ...
Page 390: ...ZyWALL 35 User s Guide 388 Chapter 24 Logs Screens Figure 198 Log Settings ...
Page 413: ...ZyWALL 35 User s Guide Chapter 25 Maintenance 411 Figure 220 Restart Screen ...
Page 414: ...ZyWALL 35 User s Guide 412 Chapter 25 Maintenance ...
Page 440: ...ZyWALL 35 User s Guide 438 Chapter 28 WAN and Dial Backup Setup ...
Page 456: ...ZyWALL 35 User s Guide 454 Chapter 31 DMZ Setup ...
Page 460: ...ZyWALL 35 User s Guide 458 Chapter 32 Route Setup ...
Page 470: ...ZyWALL 35 User s Guide 468 Chapter 33 Remote Node Setup ...
Page 522: ...ZyWALL 35 User s Guide 520 Chapter 39 System Information Diagnosis ...
Page 538: ...ZyWALL 35 User s Guide 536 Chapter 40 Firmware and Configuration File Maintenance ...
Page 550: ...ZyWALL 35 User s Guide 548 Chapter 42 Remote Management ...
Page 558: ...ZyWALL 35 User s Guide 556 Chapter 43 IP Policy Routing ...
Page 574: ...ZyWALL 35 User s Guide 572 Chapter 45 Troubleshooting Figure 364 Java Sun ...
Page 602: ...ZyWALL 35 User s Guide 600 Appendix C IP Subnetting ...
Page 608: ...ZyWALL 35 User s Guide 606 Appendix E PPTP ...
Page 626: ...ZyWALL 35 User s Guide 624 Appendix G Triangle Route ...
Page 656: ...ZyWALL 35 User s Guide 654 Appendix J Importing Certificates ...
Page 658: ...ZyWALL 35 User s Guide 656 Appendix K Command Interpreter ...
Page 664: ...ZyWALL 35 User s Guide 662 Appendix L Firewall Commands ...
Page 668: ...ZyWALL 35 User s Guide 666 Appendix M NetBIOS Filter Commands ...
Page 674: ...ZyWALL 35 User s Guide 672 Appendix O Brute Force Password Guessing Protection ...
Page 696: ...ZyWALL 35 User s Guide 694 Appendix Q Log Descriptions ...










































