ZyWALL 5 User’s Guide
Chapter 35 Filter Configuration
469
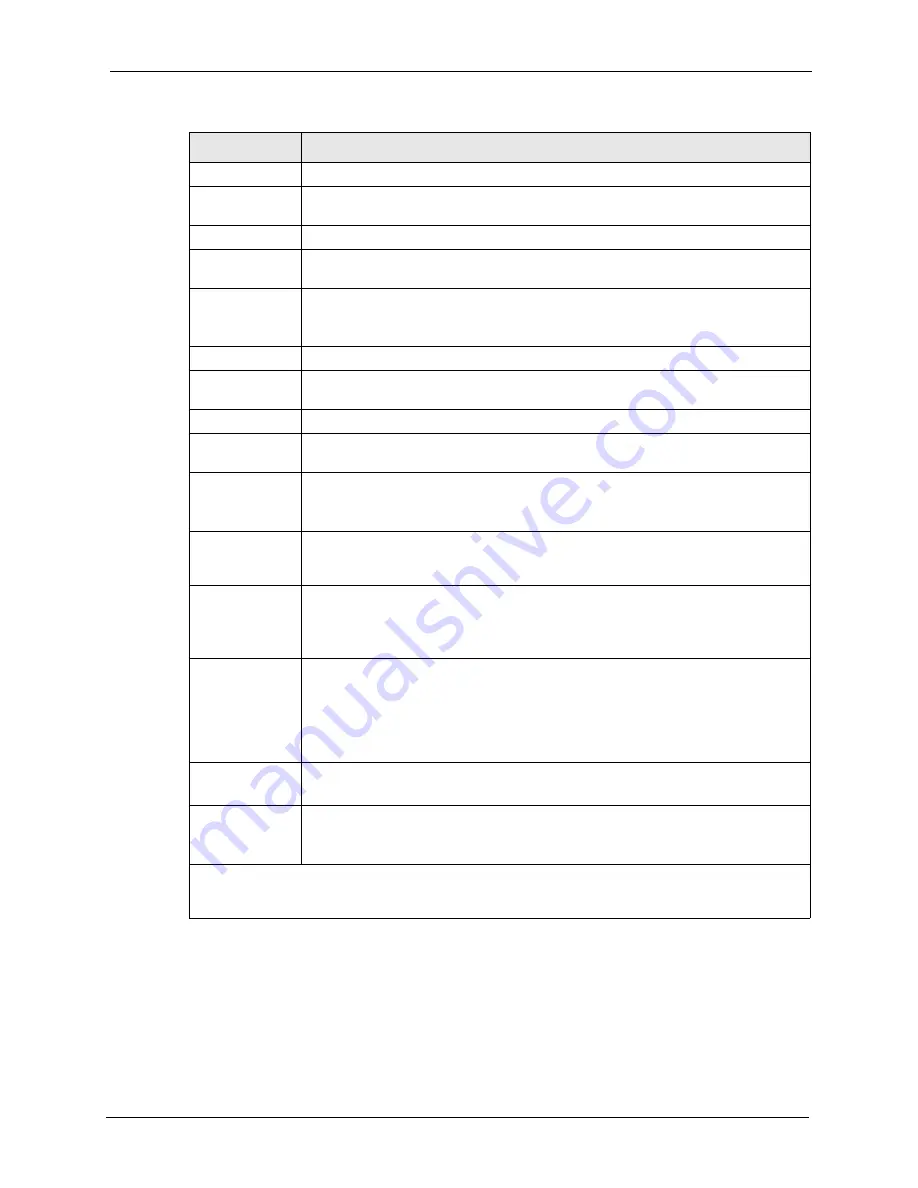
The following figure illustrates the logic flow of an IP filter.
Destination
IP Addr
Enter the destination IP Address of the packet you wish to filter. This field is ignored
if it is 0.0.0.0.
IP Mask
Enter the IP mask to apply to the
Destination: IP Addr
.
Port #
Enter the destination port of the packets that you wish to filter. The range of this field
is 0 to 65535. This field is ignored if it is 0.
Port # Comp
Press [SPACE BAR] and then [ENTER] to select the comparison to apply to the
destination port in the packet against the value given
in Destination: Port #
.
Options are
None
,
Equal
,
Not Equal
,
Less
and
Greater
.
Source
IP Addr
Enter the source IP Address of the packet you wish to filter. This field is ignored if it
is 0.0.0.0.
IP Mask
Enter the IP mask to apply to the
Source: IP Addr
.
Port #
Enter the source port of the packets that you wish to filter. The range of this field is 0
to 65535. This field is ignored if it is 0.
Port # Comp
Press [SPACE BAR] and then [ENTER] to select the comparison to apply to the
source port in the packet against the value given in
Source: Port #
.
Options are
None
,
Equal
,
Not Equal
,
Less
and
Greater
.
TCP Estab
This field is applicable only when the IP Protocol field is 6, TCP. Press [SPACE
BAR] and then [ENTER] to select
Yes
, to have the rule match packets that want to
establish a TCP connection (SYN=1 and ACK=0); if
No
, it is ignored.
More
Press [SPACE BAR] and then [ENTER] to select
Yes
or
No
. If
Yes
, a matching
packet is passed to the next filter rule before an action is taken; if
No
, the packet is
disposed of according to the action fields.
If
More
is
Yes
, then
Action Matched
and
Action Not Matched
will be
N/A
.
Log
Press [SPACE BAR] and then [ENTER] to select a logging option from the following:
None
– No packets will be logged.
Action Matched
- Only packets that match the rule parameters will be logged.
Action Not Matched
- Only packets that do not match the rule parameters will be
logged.
Both
– All packets will be logged.
Action Matched
Press [SPACE BAR] and then [ENTER] to select the action for a matching packet.
Options are
Check Next Rule
,
Forward
and
Drop
.
Action Not
Matched
Press [SPACE BAR] and then [ENTER] to select the action for a packet not
matching the rule.
Options are
Check Next Rule
,
Forward
and
Drop
.
When you have
Menu 21.1.1.1 - TCP/IP Filter Rule
configured, press [ENTER] at the message “Press
ENTER to Confirm” to save your configuration, or press [ESC] to cancel. This data will now be
displayed on
Menu 21.1.1 - Filter Rules Summary
.
Table 182
Menu 21.1.1.1: TCP/IP Filter Rule
FIELD
DESCRIPTION
Summary of Contents for ZyXEL ZyWALL 5
Page 1: ...ZyWALL 5 Internet Security Appliance User s Guide Version 3 64 3 2005 ...
Page 2: ......
Page 26: ...ZyWALL 5 User s Guide 24 ...
Page 44: ...ZyWALL 5 User s Guide 42 ...
Page 86: ...ZyWALL 5 User s Guide 84 Chapter 3 Wizard Setup ...
Page 96: ...ZyWALL 5 User s Guide 94 Chapter 4 LAN Screens ...
Page 102: ...ZyWALL 5 User s Guide 100 Chapter 5 Bridge Screens ...
Page 130: ...ZyWALL 5 User s Guide 128 Chapter 7 WAN Screens Figure 45 WAN PPPoE Encapsulation ...
Page 138: ...ZyWALL 5 User s Guide 136 Chapter 7 WAN Screens Figure 50 Dial Backup Setup ...
Page 144: ...ZyWALL 5 User s Guide 142 Chapter 7 WAN Screens ...
Page 152: ...ZyWALL 5 User s Guide 150 Chapter 8 DMZ Screens ...
Page 179: ...ZyWALL 5 User s Guide Chapter 10 Firewall Screens 177 Figure 73 My Service Rule Configuration ...
Page 220: ...ZyWALL 5 User s Guide 218 Chapter 13 Introduction to IPSec ...
Page 238: ...ZyWALL 5 User s Guide 236 Chapter 14 VPN Screens Figure 110 VPN Rules IKE Network Policy Edit ...
Page 261: ...ZyWALL 5 User s Guide Chapter 15 Certificates 259 Figure 122 My Certificate Details ...
Page 280: ...ZyWALL 5 User s Guide 278 Chapter 16 Authentication Server Figure 133 Local User Database ...
Page 317: ...ZyWALL 5 User s Guide Chapter 19 Bandwidth Management 315 ...
Page 318: ...ZyWALL 5 User s Guide 316 Chapter 19 Bandwidth Management ...
Page 352: ...ZyWALL 5 User s Guide 350 Chapter 21 Remote Management ...
Page 366: ...ZyWALL 5 User s Guide 364 Chapter 23 Logs Screens Figure 188 Log Settings ...
Page 389: ...ZyWALL 5 User s Guide Chapter 24 Maintenance 387 Figure 210 Restart Screen ...
Page 390: ...ZyWALL 5 User s Guide 388 Chapter 24 Maintenance ...
Page 416: ...ZyWALL 5 User s Guide 414 Chapter 27 WAN and Dial Backup Setup ...
Page 432: ...ZyWALL 5 User s Guide 430 Chapter 30 DMZ Setup ...
Page 492: ...ZyWALL 5 User s Guide 490 Chapter 37 System Information Diagnosis ...
Page 508: ...ZyWALL 5 User s Guide 506 Chapter 38 Firmware and Configuration File Maintenance ...
Page 520: ...ZyWALL 5 User s Guide 518 Chapter 40 Remote Management ...
Page 536: ...ZyWALL 5 User s Guide 534 Chapter 42 Troubleshooting Figure 343 Java Sun ...
Page 564: ...ZyWALL 5 User s Guide 562 Appendix C IP Subnetting ...
Page 570: ...ZyWALL 5 User s Guide 568 Appendix E PPTP ...
Page 571: ...ZyWALL 5 User s Guide 569 ...
Page 572: ...ZyWALL 5 User s Guide 570 ...
Page 590: ...ZyWALL 5 User s Guide 588 Appendix G Triangle Route ...
Page 620: ...ZyWALL 5 User s Guide 618 Appendix J Importing Certificates ...
Page 622: ...ZyWALL 5 User s Guide 620 Appendix K Command Interpreter ...
Page 628: ...ZyWALL 5 User s Guide 626 Appendix L Firewall Commands ...
Page 632: ...ZyWALL 5 User s Guide 630 Appendix M NetBIOS Filter Commands ...
Page 638: ...ZyWALL 5 User s Guide 636 Appendix O Brute Force Password Guessing Protection ...
Page 660: ...ZyWALL 5 User s Guide 658 Appendix Q Log Descriptions ...










































