User Manual
UMN:CLI
V8102
473
9.18
Source Address Validation
The Reverse Path filter (rp_filter) can reject incoming packets if their source address
doesn
’t match the network interface that they’re arriving on, which helps to prevent IP
spoofing. When source and destination traffic to the same IP using different interface oc-
curs, the Linux kernel drops the traffic as potentially spoofed. This is called reverse-path
filtering.
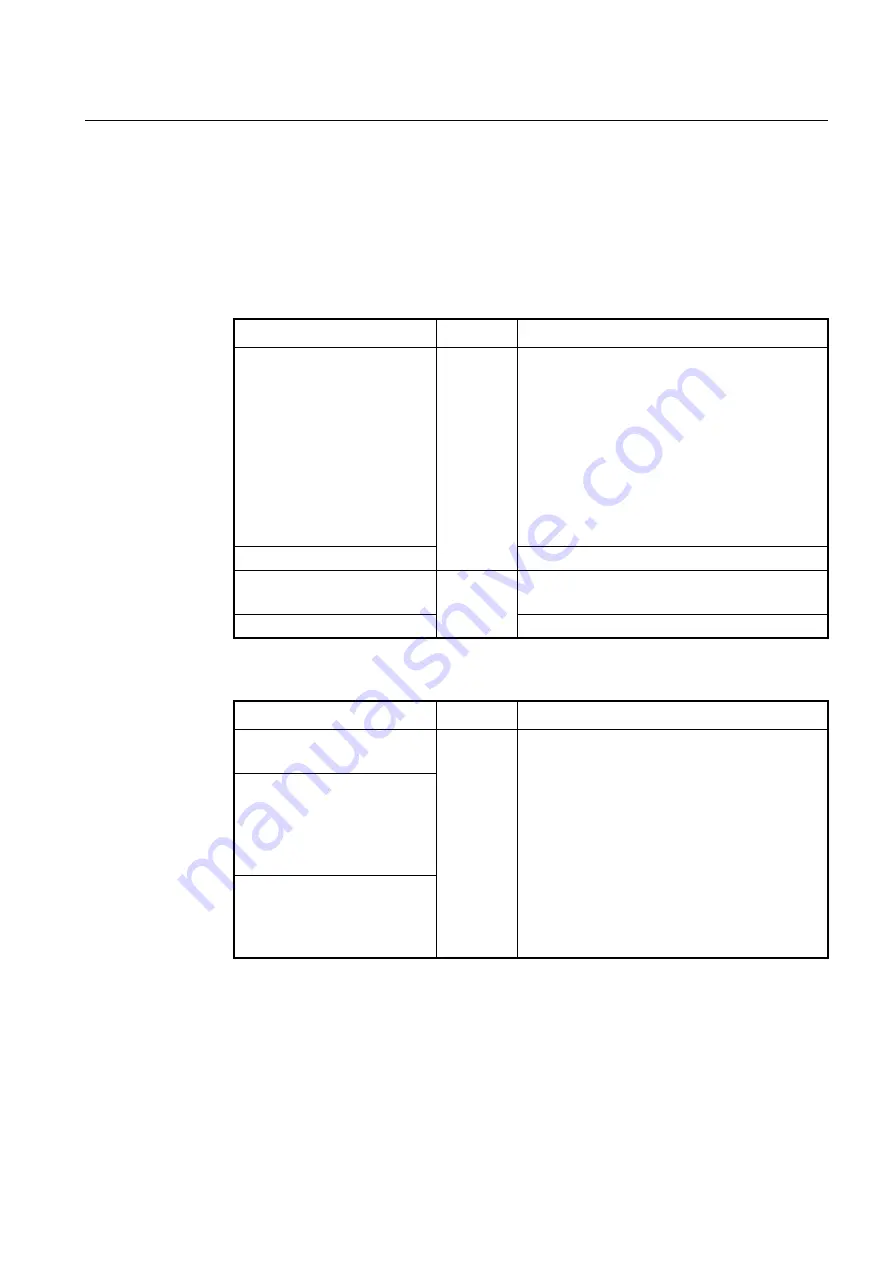
To enable/disable reverse-path filtering, use the following command.
Command
Mode
Description
ip configuration all rp_filter
<0-
2>
Global
Enables reverse-path filtering for source validation.
0: no source validation (default)
1: strict mode- Each incoming packet is tested against
the FIB and if the interface is not the best reverse path
and the packet check will fail. The failed packets are
discarded.
2: loose mode- Each incoming packet
’s source address
is also tested against the FIB and if the source address
is not reachable via any interface the packet check will
fail.
no ip configuration all rp_filter
Disables reverse-path filtering for source validation.
ip configuration rp_filter
<0-2>
Interface
[VLAN]
Enables reverse-path filtering for source validation on
the interface.
no ip configuration rp_filter
Disables reverse-path filtering for source validation.
To display reverse-path filtering status, use the following command.
Command
Mode
Description
show
ip
configuration
all
rp_filter
Global
Shows reverse-path filtering status.
show ip configuration manage-
ment
{
tengigabitethernet
IFPORT
|
gpon IFPORT
|
chan-
nelgroup
IFPORT
|
vlan VLANID
}
rp_filter
show ip configuration loopback
{
tengigabitethernet
IFPORT
|
gpon IFPORT
|
channelgroup
IFPORT
|
vlan VLANID
}
rp_filter
9.19
Blocking Direct Broadcasting Packets
RFC 2644 recommends that system blocks broadcast packet of same network bandwidth
with interface of equipment, namely direct broadcast packet. Hereby, V8102 is supposed
to block direct broadcast packet by default setting. However, you can enable or disable it
in V8102.
















































